Malicious encrypted traffic detection method and system based on behavior analysis
A traffic detection and behavior analysis technology, applied in transmission systems, digital transmission systems, electrical components, etc., can solve the problems of inaccurate detection results of encrypted traffic, and reduce the false alarm rate.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
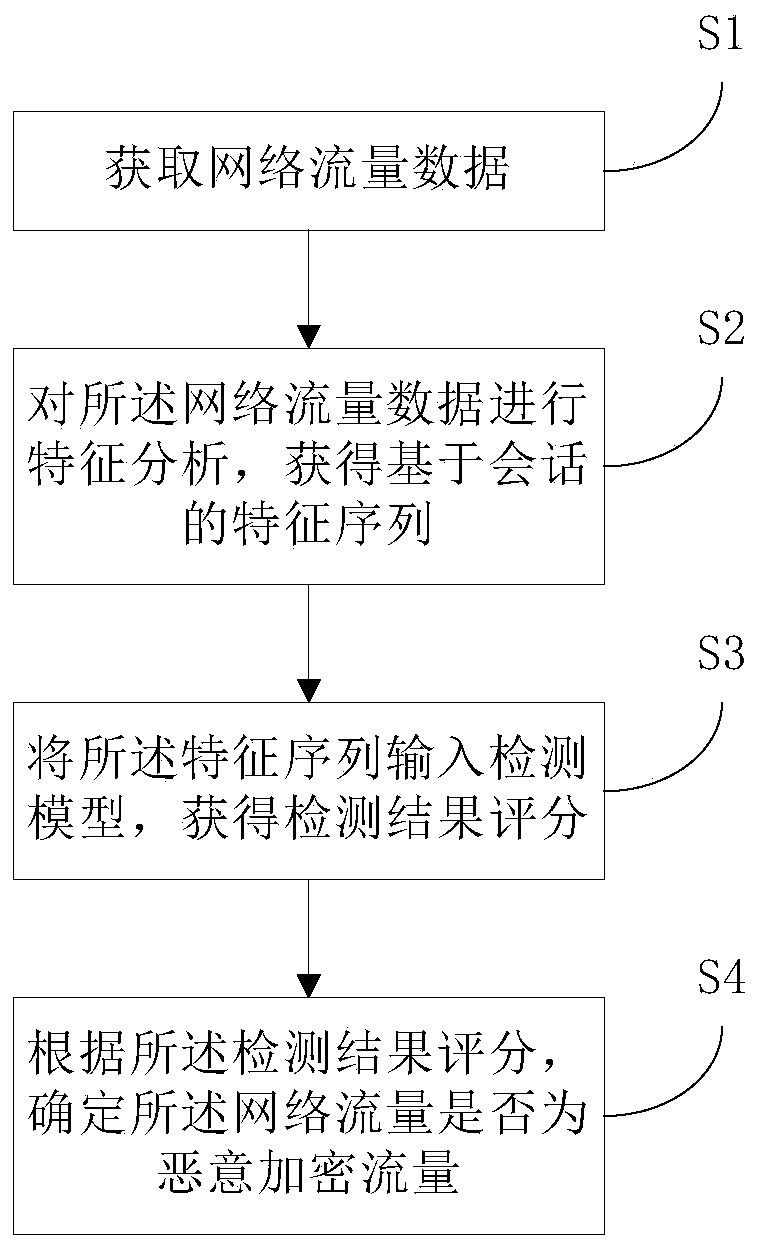
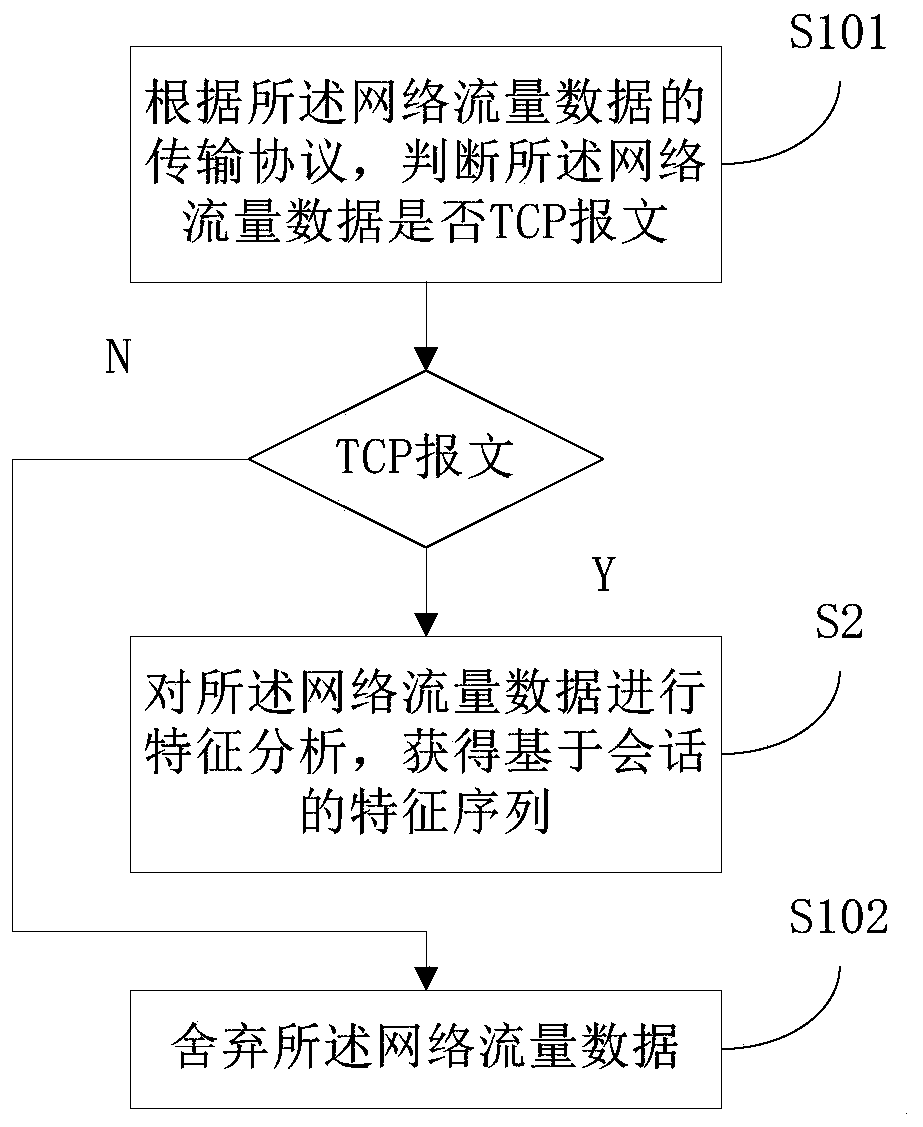
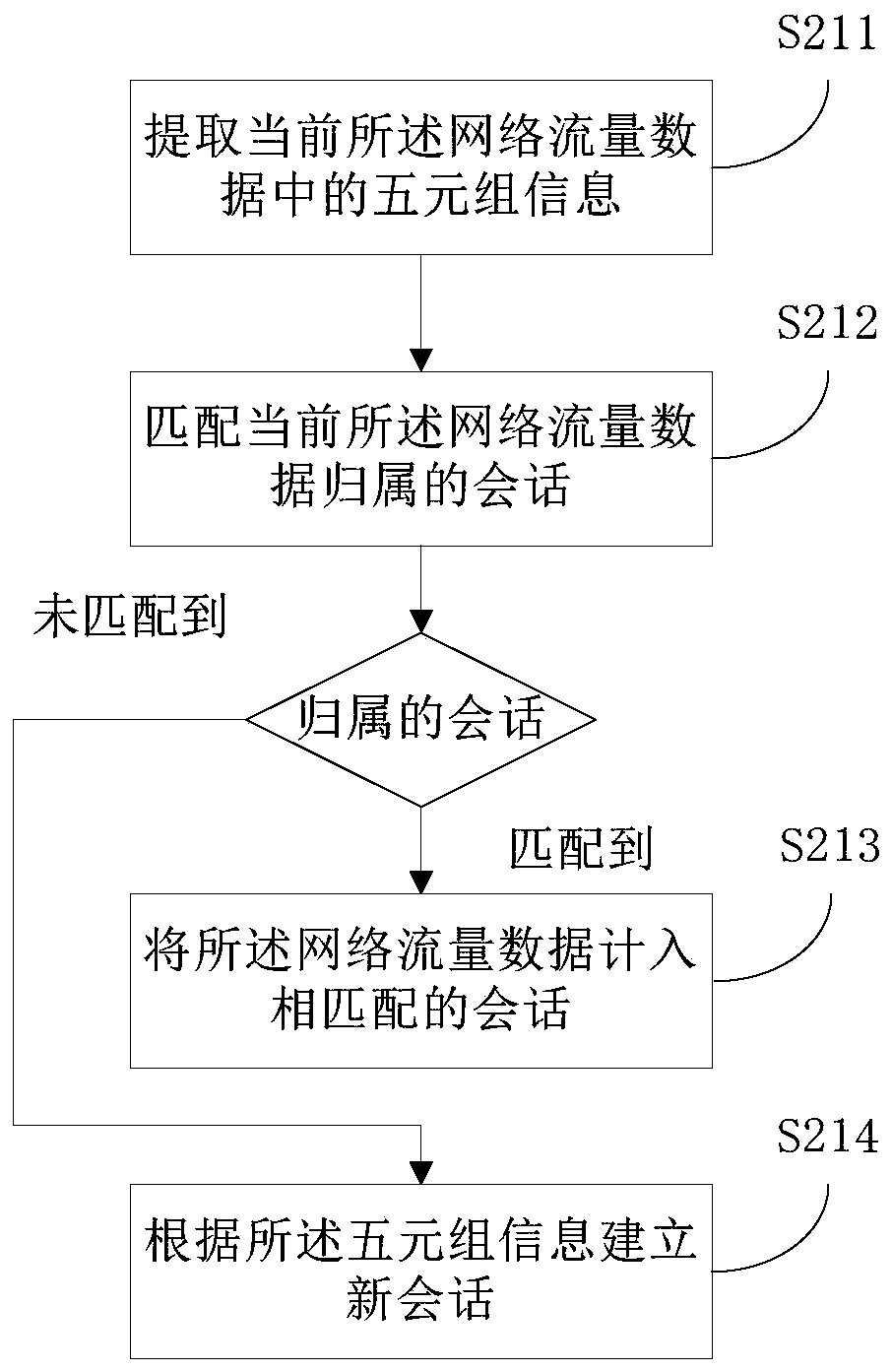
[0054] The embodiments will be described in detail hereinafter, examples of which are illustrated in the accompanying drawings. When the following description refers to the accompanying drawings, the same numerals in different drawings refer to the same or similar elements unless otherwise indicated. The implementations described in the following examples do not represent all implementations consistent with this application. These are merely examples of systems and methods consistent with aspects of the present application as recited in the claims.
[0055] The malicious encrypted traffic detection method based on behavior analysis provided by this application can be applied to Internet behavior management equipment, so as to detect traffic data in the network and prevent users from being threatened by malicious traffic. The online behavior management device is a device that helps Internet users to control and manage Internet usage. Access web page filtering, network applica...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More