Method for controlling access of wireless terminal and wireless access point
A wireless access point and wireless terminal technology, applied in the field of wireless communication, can solve problems such as embezzlement of wireless signals and hijacking of private information, and achieve the effect of ensuring security and reliability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0051] Embodiment 1: a method for controlling wireless terminal access, the specific steps are as follows:
[0052] Step 1: The wireless access point sends out a wireless signal, and the wireless terminal receives the wireless signal and sends authentication information with address information to the wireless access point.
[0053] Step 2: After receiving the authentication information, the wireless access point performs authentication and saves the authentication information, and if the authentication is passed, sends a request for permission to the wireless terminal and interacts with the wireless terminal.
[0054] Step 3: The wireless access point establishes a common address information database. The wireless access point regularly calls the address information of the wireless terminal and searches it in the common address information database stored by itself.
[0055] Step 4, if not retrieved, send an address call request to the wireless terminal.
[0056] Step 5: Af...
Embodiment 2
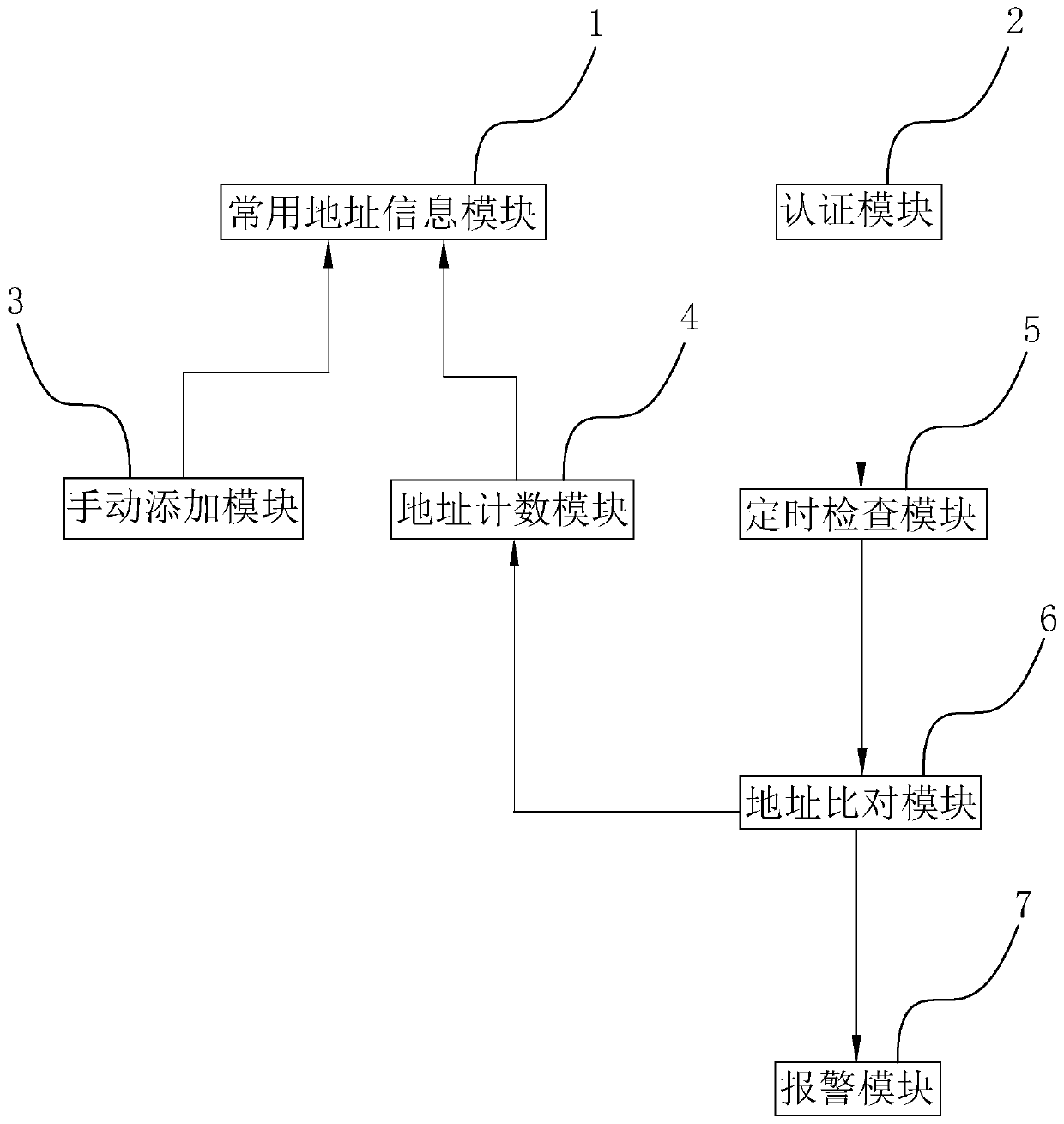
[0061] Embodiment 2. A wireless access point, such as figure 1 As shown, the control system includes a common address information module 1, an authentication module 2, a regular inspection module 5, an address comparison module 6, a manual addition module 3, an address counting module 4 and an alarm module 7.
[0062] Such as figure 1 As shown, the frequently used address information module 1 stores frequently used address information as a frequently used address information database. The manual adding module 3 receives the address information input from the outside and transmits the address information to the common address information module 1 for storage. Users can directly manage common address information databases by manually adding module 3.
[0063] Such as figure 1 As shown, the authentication module 2 stores authentication rules. The authentication module 2 receives the authentication information input from the outside and authenticates the authentication informat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com