Identity verification method and device, computer equipment and readable storage medium
An identity verification and verification code technology, applied in the Internet field, can solve problems such as different identity authentication methods of business systems, and achieve the effects of reducing cumbersome work, improving security, and reducing maintenance costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
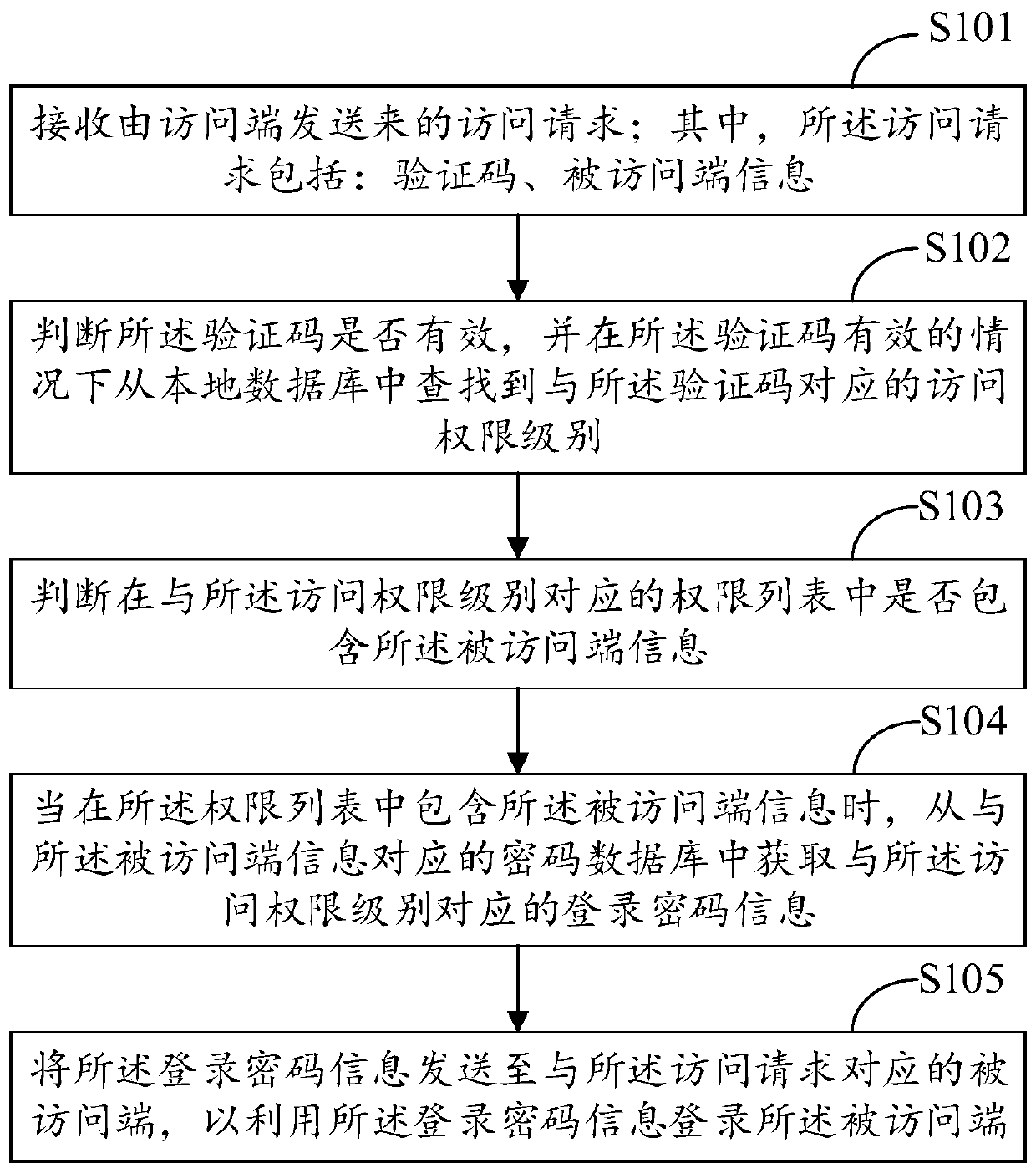
[0041] The embodiment of the present invention provides an identity verification method, which is applied to an asset management integration platform in the financial industry, such as figure 1 As shown, the method specifically includes the following steps:
[0042] Step S101: Receive an access request sent by an access terminal; wherein, the access request includes: a verification code and information of the accessed terminal.
[0043] In this embodiment, the asset management integration platform is an integrated platform that integrates multiple asset management business systems; the access terminal is a user terminal used to access each asset management business system through the asset management integration platform; each integrated in the asset management The asset management business system of the integrated platform can be regarded as a visited end. Preferably, the accessed terminal information is the IP address information or identity ID information of the accessed termina...
Embodiment 2
[0073] The embodiment of the present invention provides an identity verification method, which is applied to an asset management integration platform. The asset management integration platform integrates various asset management business systems, and the access terminal can access various assets through the asset management integration platform. Management business system; specifically, the asset management integration platform includes: a user interaction module, an identity verification module, and a business module; wherein the user interaction module is connected to the access terminal for the access terminal to log in to the office through the user interaction module The asset management integration platform; the identity verification module is used to perform identity verification and authorization verification for users logging in the asset management integration platform, and only users who have passed the identity verification and have corresponding permissions can acces...
Embodiment 3
[0107] The embodiment of the present invention provides an identity verification device, which is applied to an asset management integration platform, such as figure 2 As shown, the device specifically includes the following components:
[0108] The receiving module 301 is configured to receive an access request sent by an access terminal; where the access request includes: a verification code and information of the accessed terminal.
[0109] Specifically, the device further includes:
[0110] The processing module is configured to receive platform registration information sent by the access terminal; wherein the platform registration information includes: login account information and user basic information; the verification code is generated according to the login account information, and the verification code is generated according to the login account information. The user basic information determines the access authority level; the verification code and the access authority le...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More