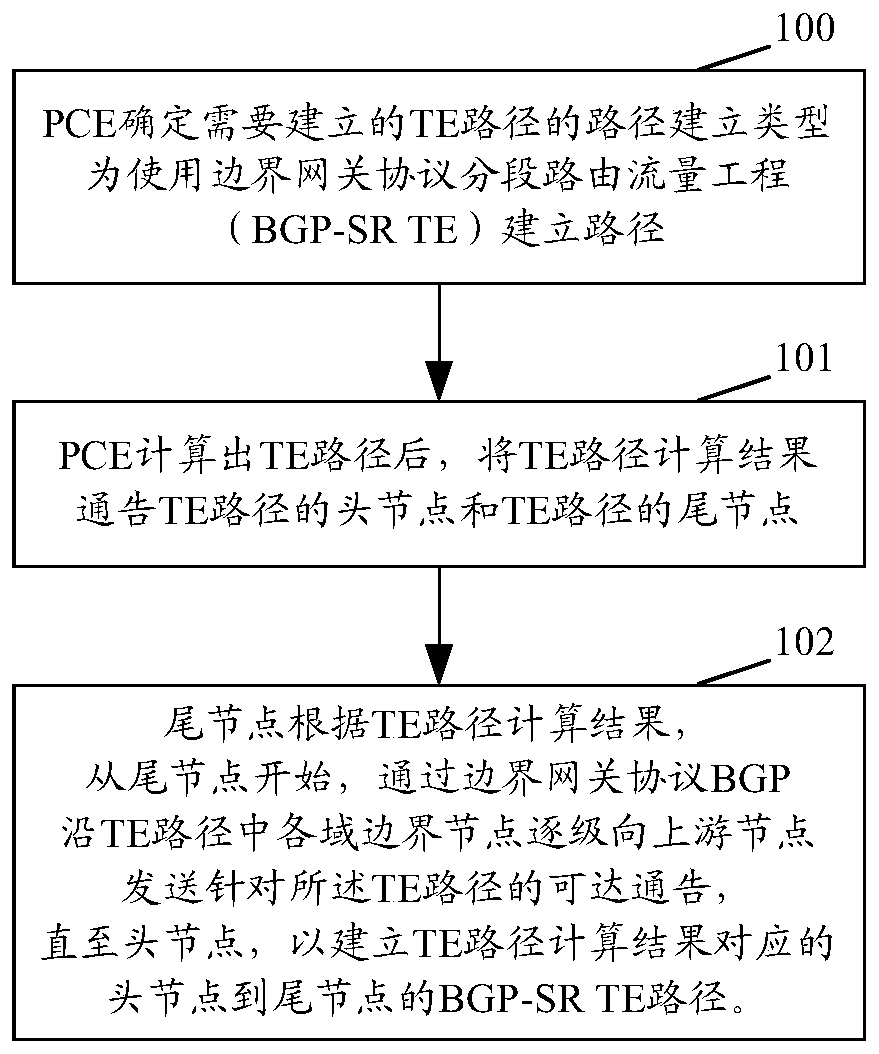
Traffic engineering path establishing method, device and system
A method of establishment and technology of traffic engineering, applied in the field of data communication, can solve the problems of forwarding efficiency beyond the label encapsulation capability of the device, MTU, label stack depth, etc., so as to improve the packet load efficiency, facilitate status detection, and reduce the label stack depth. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example
[0215] The tail node D uses the local unique absolute label value corresponding to the first SLID as the key value to create a corresponding ILM forwarding entry as the first forwarding table (the label operation is POP). In an illustrative example, including:
[0216] When the first SLID is a globally unique index value, the tail node D obtains the corresponding local unique absolute label value by offsetting the first SLID in the SRGB of the tail node D itself, and establishes the ILM with the obtained local unique absolute label value as the key value A forwarding entry: when the first SLID is already a globally unique absolute label value or a local unique absolute label value, an ILM forwarding entry is directly established with the first SLID as a key value.
[0217] In an exemplary instance, when the node is a tail node D, the second notification module is specifically used to:
[0218] The tail node D advertises the TE path and the obtained first SLID to its upstream ...
no. 2 example
[0292] The second embodiment combines Figure 13 , based on the first embodiment, in the case that the intra-domain topology information needs to be kept secret, each sub-PCE may return intra-domain path segment information composed of Path-key subobjects to the parent PCE. In the second embodiment, it is assumed that the path segment information returned by the sub-PCE1, sub-PCE2, and sub-PCE3 to the parent PCE4 are path-key1, path-key2, and path-key3 respectively. After inter-domain links and domain boundary nodes are added to PCE4, the Get the complete end-to-end TE path: {bn(S),path-key1,bn(A1),link(A1->A2),bn(A2),path-key2,bn(A3),link(A3- >A4), bn(A4), path-key3, bn(D)}, the TE path will be sent to the head node S via PCE1, and sent to the tail node D via PCE3. Similar to the first embodiment, the tail node D will send the BGP-SR TENLRI reachability notification of the SR-TE path to the upstream domain border node A4 through BGP, and so on, triggering the allocation of S...
no. 3 example
[0307] The third embodiment combines Figure 13 , based on the first embodiment, when the topology in the network changes and there is no longer a TE path that meets the corresponding constraint conditions, the parent PCE4 will send a PCUpd message to the child PCE1 and child PCE3, and the EROobject included in it is empty. It should be noted that , PCE1 has authorized PCE4 in advance for the calculation of the BGP-SR TE path.
[0308] Furthermore, PCE1 sends a PCUpd message to the head node S, and the ERO object included in it is empty; PCE3 sends a PCUpd message to the tail node D, and the ERO object included in it is empty.
[0309] After receiving the PCUpd message, the head node S can clear the FTN forwarding information corresponding to the BGP-SR TE path. However, in order to avoid unnecessary traffic interruption, the head node S can delay clearing the FTN forwarding information.
[0310] After the tail node D receives the above PCUpd message, it releases the SLID loc...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap