Decentralized data transaction method based on block chain
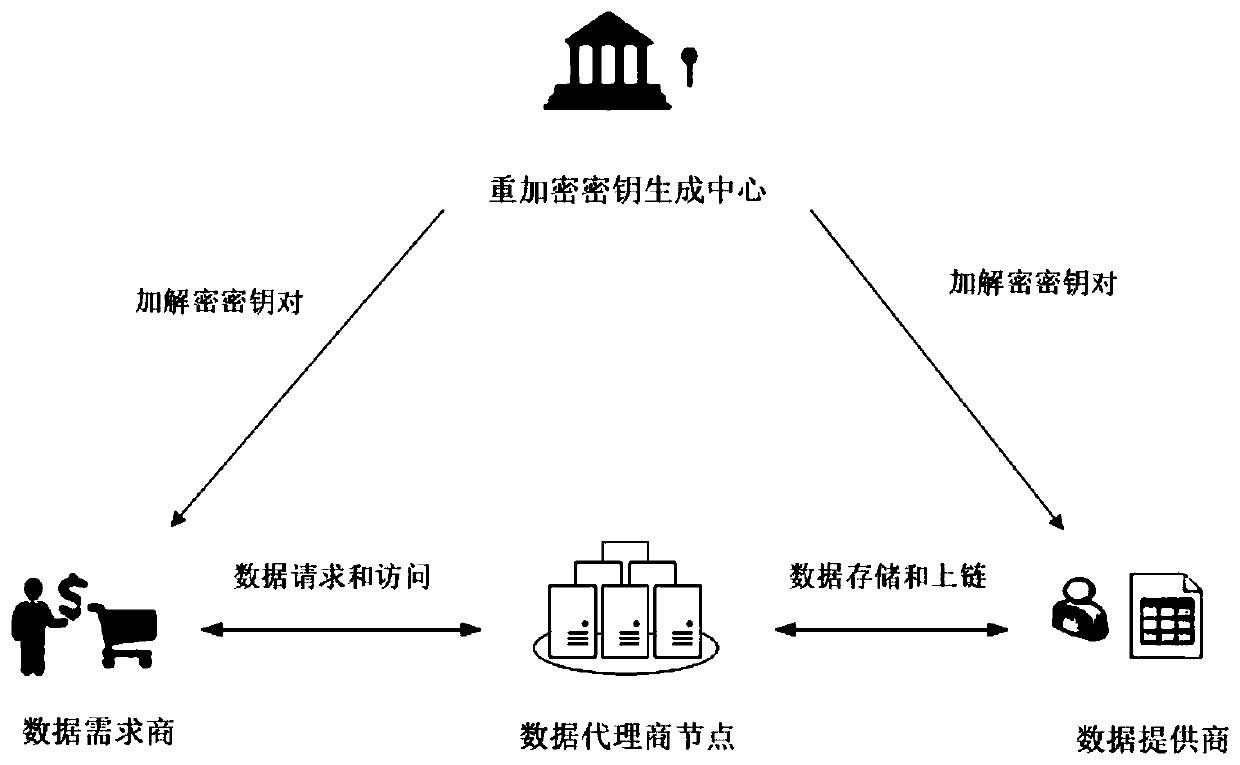
A transaction method and decentralized technology, applied in the field of information security, can solve problems such as untrustworthy third-party data centers, data and identity privacy security issues, untrustworthy data centers, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0100] Data demander j requires data type D S It is the running monitoring data of the smart bracelet, and the required data entry is D A =1000, the data quality score requires β≥6.0, and the size of the candidate pool is N=3×D A . The data demander j publishes the data demand through the smart contract, which contains the above fields, and pays the reward τ=1000 of the payment data set to the contract account in advance.
[0101] In the blockchain-based big data trading platform, multiple data providers own this type of data. After the data demand contract is released, the data provider can summarize the blockchain data through the contract address of the smart contract and the interface provided. The information is sent to the smart contract to authorize the data transaction, and the data is agreed to participate in the transaction, and the smart contract will match the data. Table 1 represents the data information of the data providers authorized to participate in this d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More