Certificateless searchable encryption method and system applied to multiple receiving ends
A multi-receiver and encryption method technology, applied in the field of information security, can solve the problems of only considering a single receiver application scenario and large computing overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
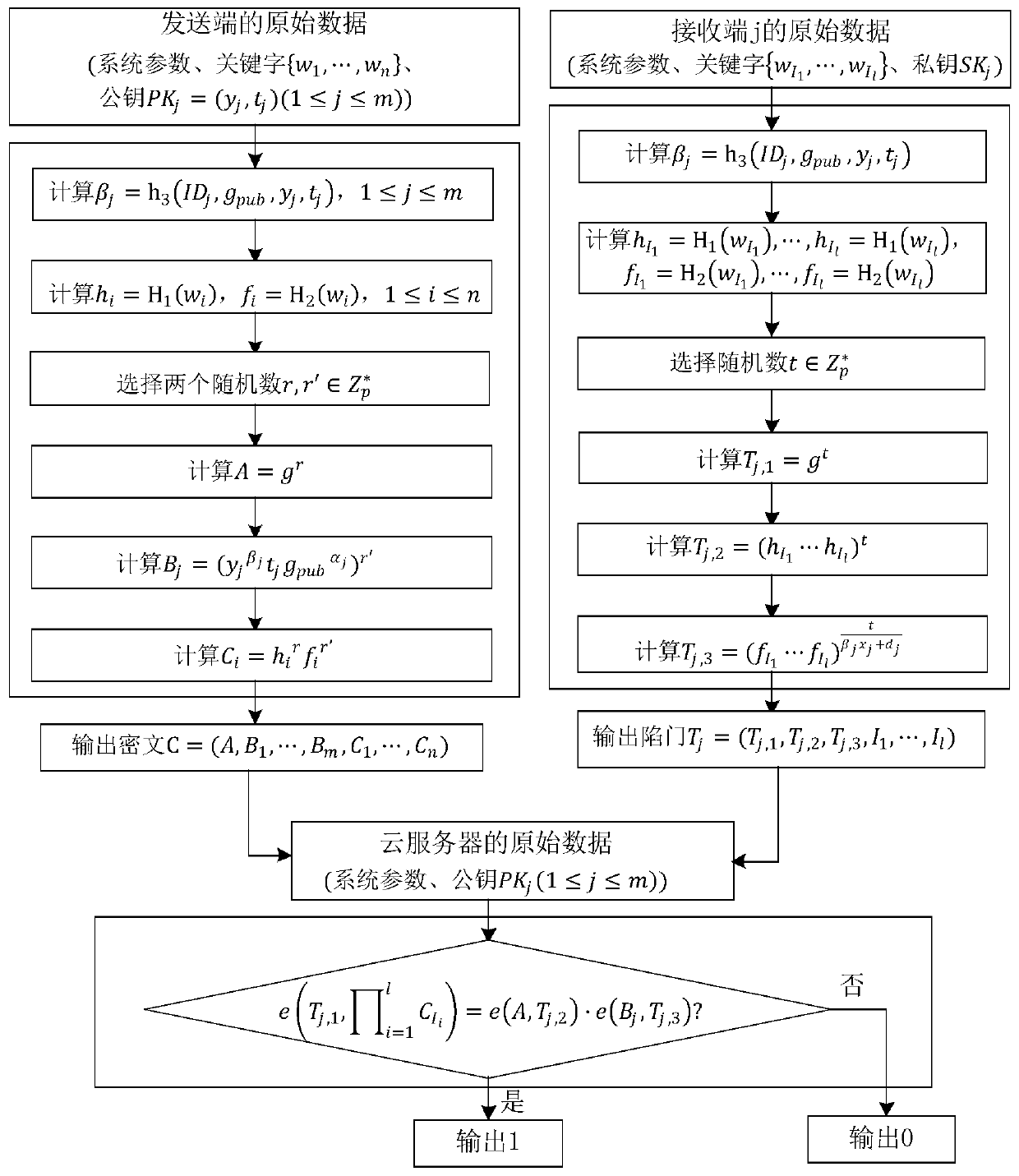
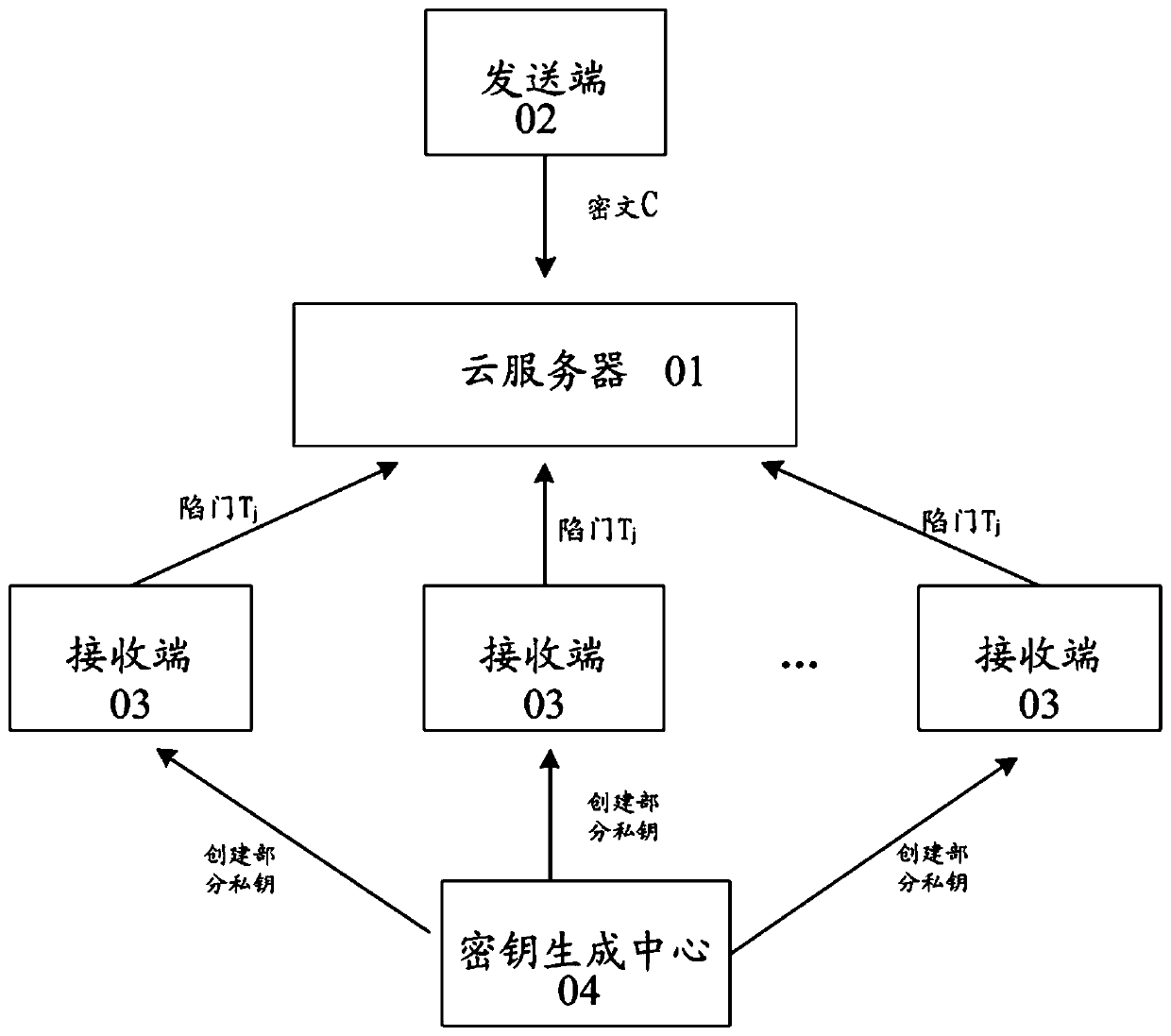
Method used
Image
Examples
Embodiment Construction
[0068] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0069] The symbols of the embodiments of the present invention are described as follows:
[0070] p: a large prime number.
[0071] A set of integers consisting of 1, 2, ..., p-1.
[0072] G 1 , G 2 : A cyclic group of order p.
[0073] g: for group G 1 generator of .
[0074] g u : Group G1 The u power of the element g in .
[0075] e: from G 1 ×G 1 to G 2 The bilinear pairing map of .
[0076] h 0 (·), H 1 (·), H 2 (·), h 3 ( ): Collision-resistant cryptographic hash function
[0077] s: The system master key secretly held by the key generation center (KGC, key generation center).
[0078] g pub : The system master public key published by KGC, the calculation formula is g pub =g s .
[0079] ID j : Distinguished identifier of user j.
[0080] d j : Partial private key of user j.
[0081] x...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More