Method for generating secret key and device thereof
A technology for generating keys and communication keys, applied to security devices, secure communication devices, and key distribution, which can solve problems affecting HSS development and HSS service pressure, reduce signaling overhead, improve transmission performance, and ensure security Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
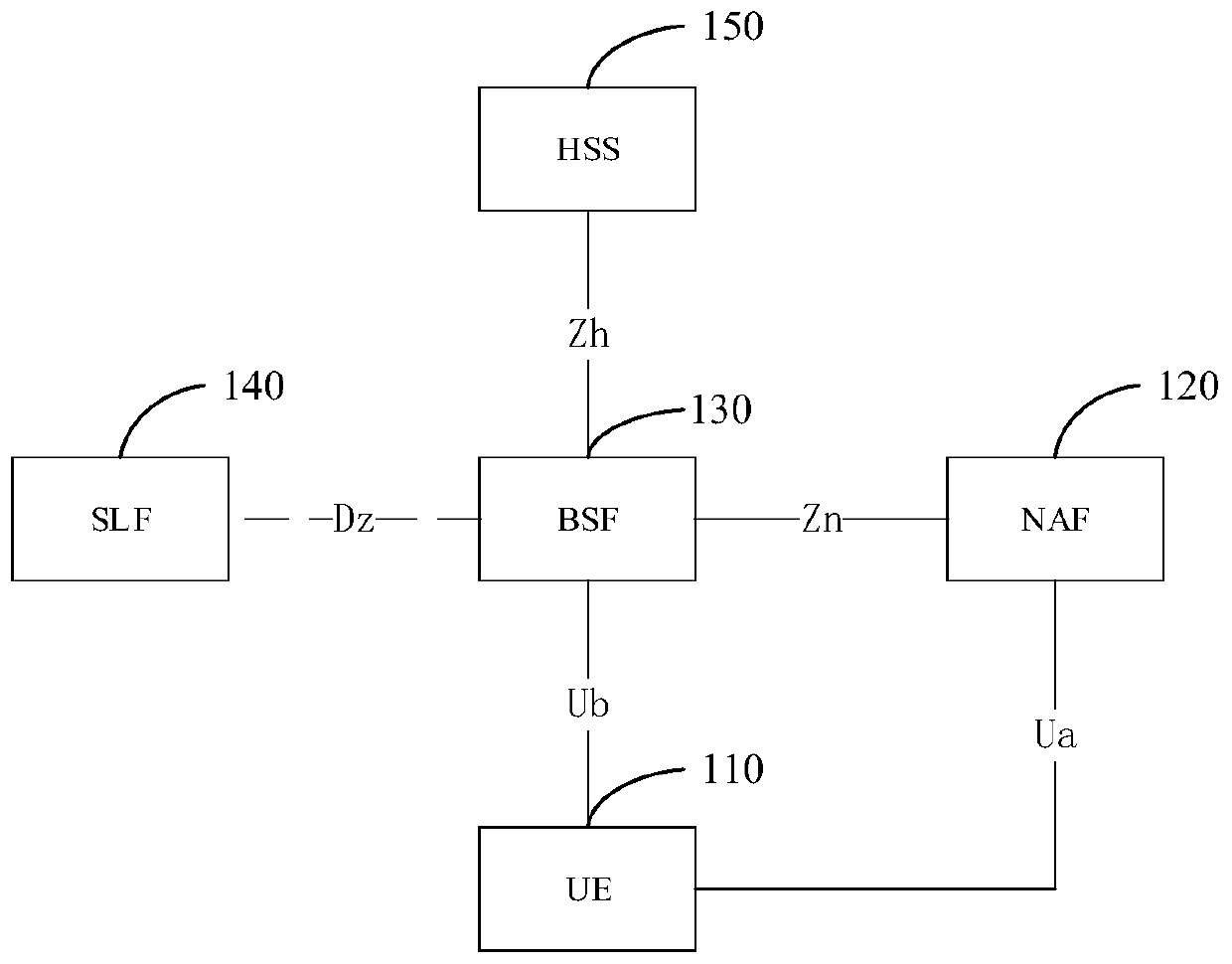
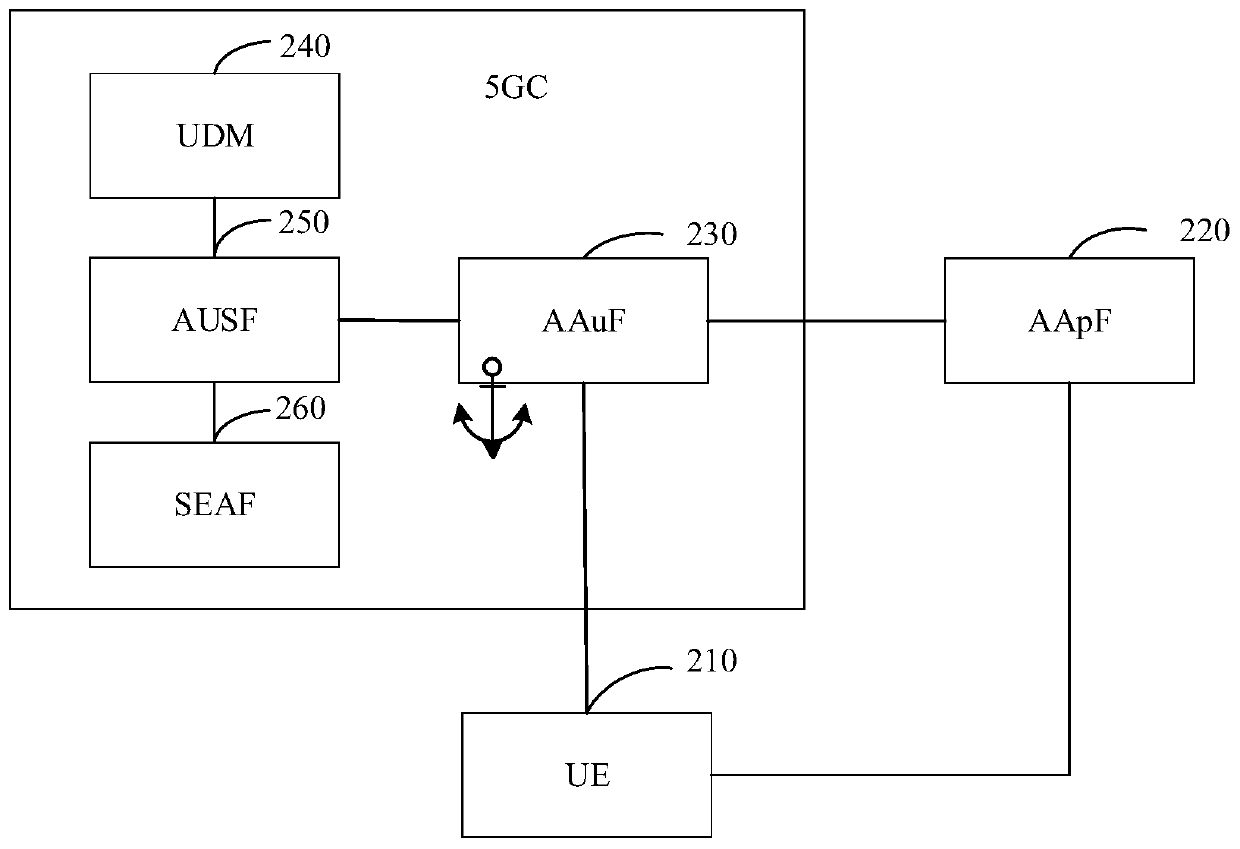
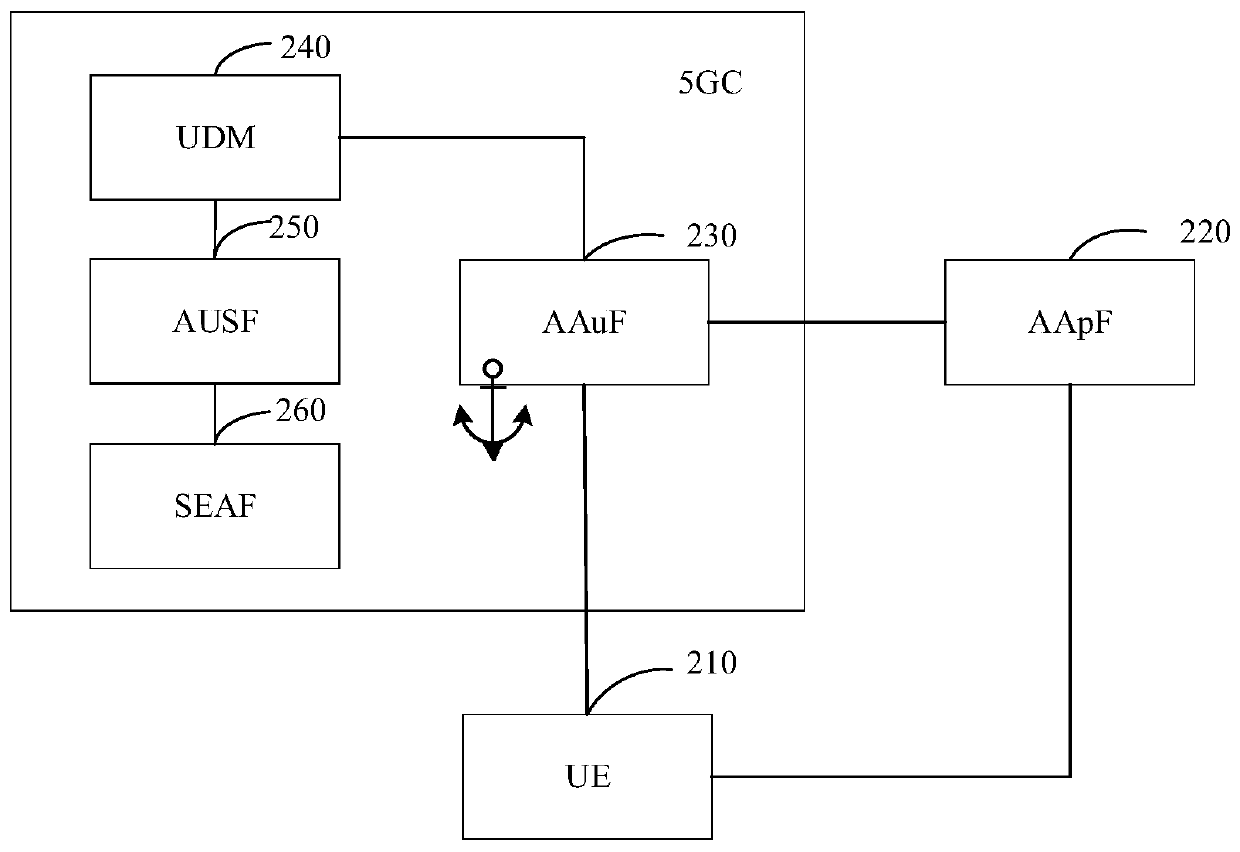
[0189] The technical solution in this application will be described below with reference to the accompanying drawings.
[0190] In the embodiments of the present application, "at least one" means one or more, and "multiple" means two or more. "And / or" describes the association relationship of associated objects, indicating that there may be three types of relationships, for example, A and / or B, which can mean: A exists alone, A and B exist simultaneously, and B exists alone, where A, B can be singular or plural. The character " / " generally indicates that the contextual objects are an "or" relationship. "At least one of the following" or similar expressions refer to any combination of these items, including any combination of single or plural items. For example, at least one item (unit) in a, b or c can represent: a, b, c, a-b, a-c, b-c or a-b-c, wherein a, b, c can be single or multiple. "A belongs to B" can mean that A is a subset of B, or that the content of A is the same...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More