TEE-based Internet of Things secure startup implementation method
A technology for secure startup and implementation methods, applied in computer security devices, program/content distribution protection, digital data authentication, etc., can solve the problem of private data theft or tampering damage, TEE or trusted applications cannot provide normal services, cannot boot, etc. question
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. All other embodiments obtained by persons of ordinary skill in the art based on the embodiments of the present invention belong to the protection scope of the present invention.
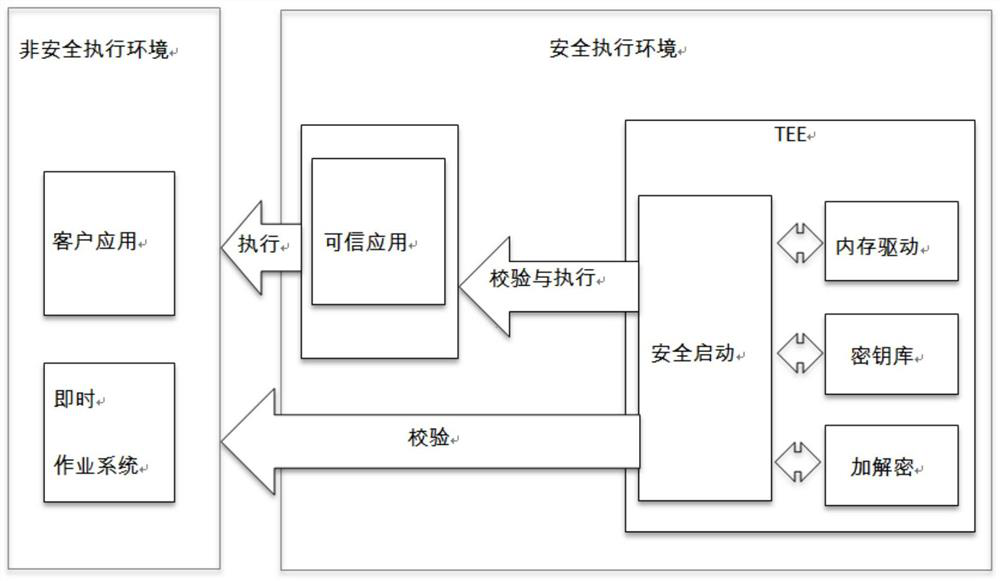
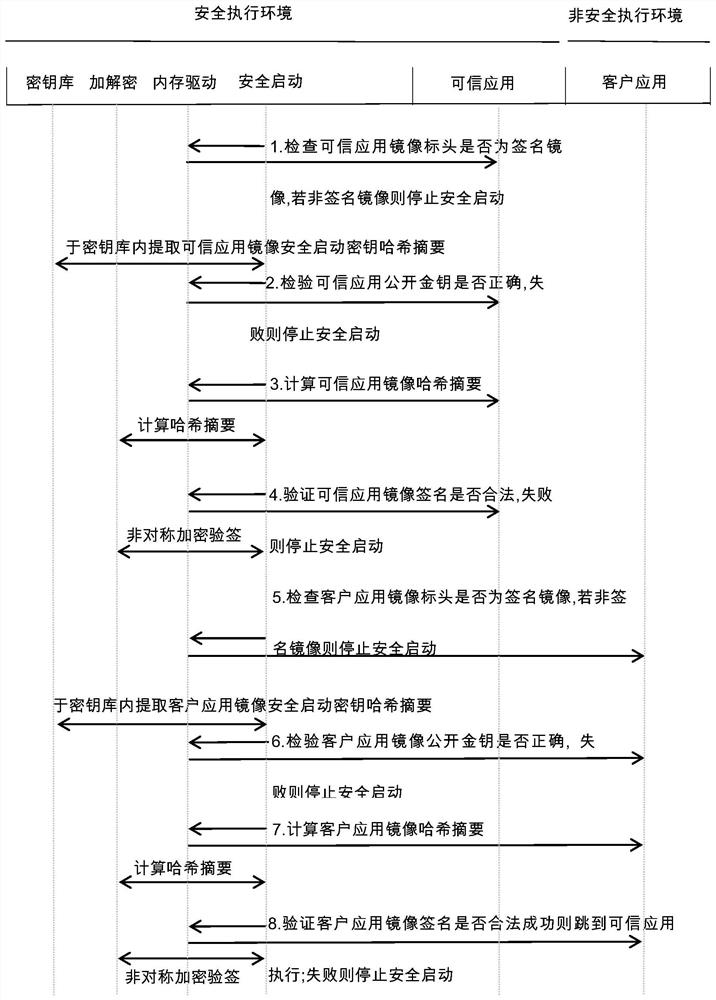
[0030] Such as figure 1 , 3 As shown, a method for implementing secure start-up based on the TEE Internet of Things according to an embodiment of the present invention includes the following steps:
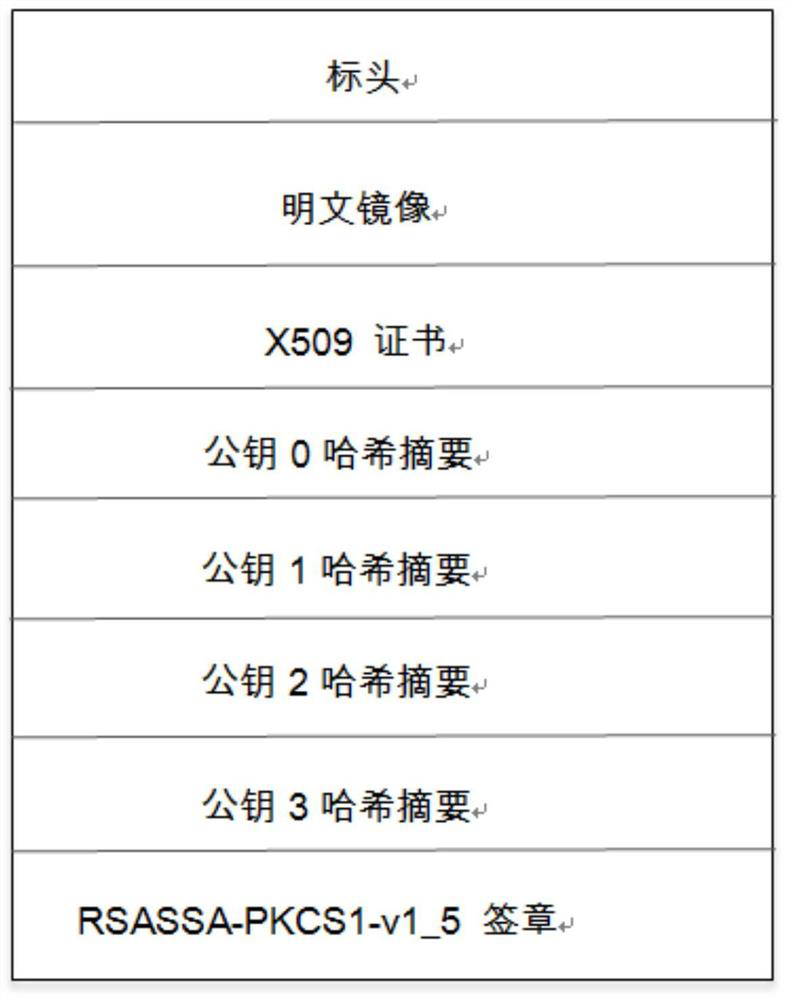
[0031] S1: Check the validity of the trusted application image header, find out the trusted application image that is a signed image, and use the flag contained in the signature header to identify whether the image is signed. If the flag is not a signed image, stop security start up;
[0032] ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More