High-security special document transmission method and system
A high-security, transmission system technology, which is applied in the field of high-security special document transmission methods and systems, can solve problems such as privacy leakage of parties, and achieve the effect of reducing risks and improving privacy protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
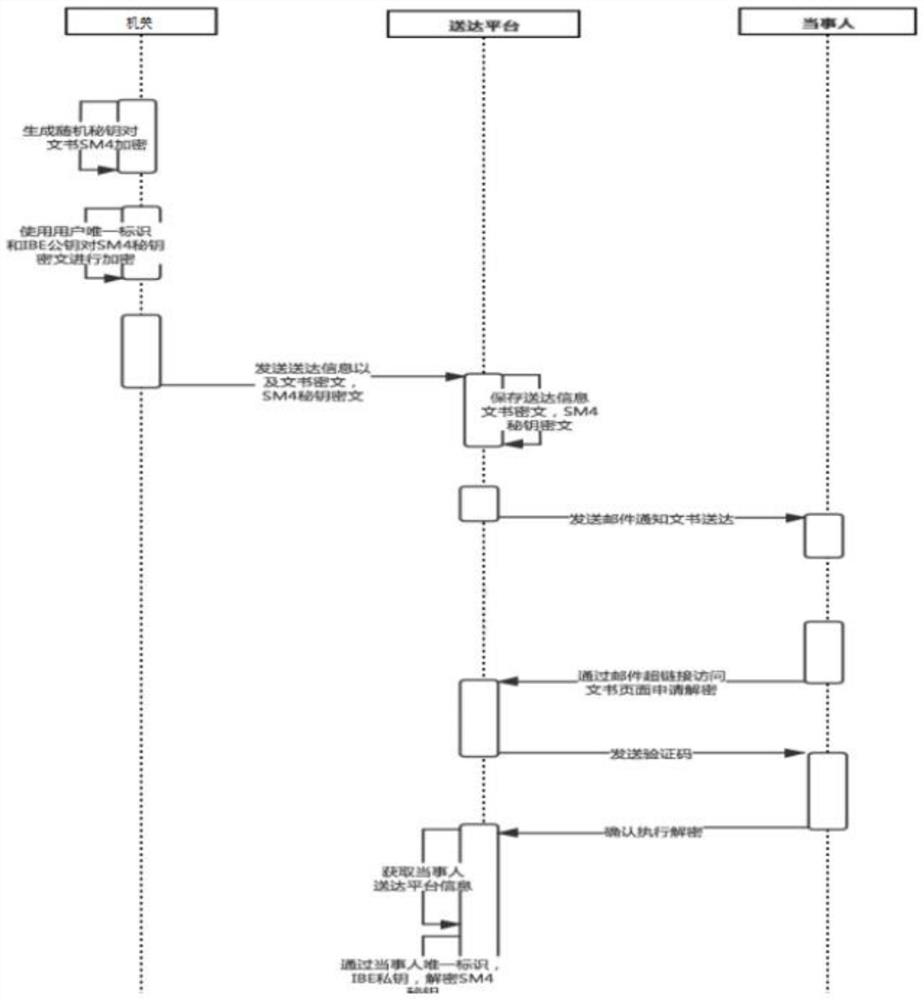
[0051] A high-security proprietary document transfer method, see figure 1 , including the following steps:
[0052] S1: The authority randomly generates an SM4 symmetric key, and uses the SM4 symmetric key to encrypt the special document to be delivered to obtain the encrypted document;
[0053] S2: The agency end encrypts the SM4 symmetric key to obtain the encryption key, including:
[0054] The agency end receives the entered unique ID of the party; the unique ID of the party is used to uniquely identify the party.
[0055] The agency uses the unique identifier of the party and the IBE asymmetric public key to perform IBE encryption on the SM4 symmetric key to obtain the encryption key.
[0056] S3: The agency side delivers the encrypted document and encryption key to the party side through the delivery platform, including:
[0057] The agency generates delivery information;
[0058] The agency sends the delivery information, encrypted documents and encryption keys to t...
Embodiment 2
[0074] A high security dedicated document delivery system, see figure 2 ,include:
[0075] Agency end: used to randomly generate SM4 symmetric key, and use the SM4 symmetric key to encrypt the special document to be delivered to obtain the encrypted document; the agency end is also used to encrypt the SM4 symmetric key to obtain the encryption key , deliver the encrypted document and encryption key to the parties through the delivery platform;
[0076] delivery platform;
[0077] Party side: used to decrypt the received encryption key to obtain the plaintext of the SM4 symmetric key, and use the plaintext of the SM4 symmetric key to decrypt the received encrypted document to obtain the plaintext of the special document.
[0078] Preferably, the organ end is specifically used for:
[0079] Receive the entered unique identifier of the party, and use the unique identifier of the party and the IBE asymmetric public key to perform IBE encryption on the SM4 symmetric key to obta...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More