Plug-in processing method and device
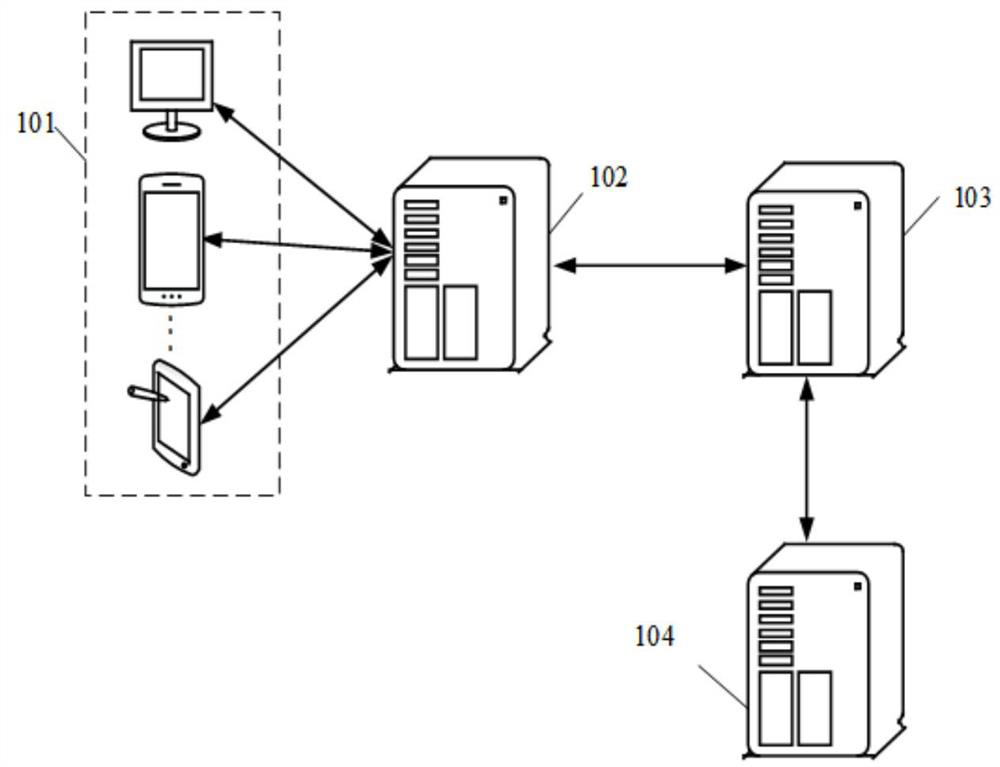
A processing method and plug-in technology, applied in the computer field, can solve the problems that the scanner cannot adapt to the vulnerability scanning scene, cannot accurately describe the vulnerability, cannot obtain the vulnerability scanning logic, etc., and achieve the effect of language compatibility and strong versatility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
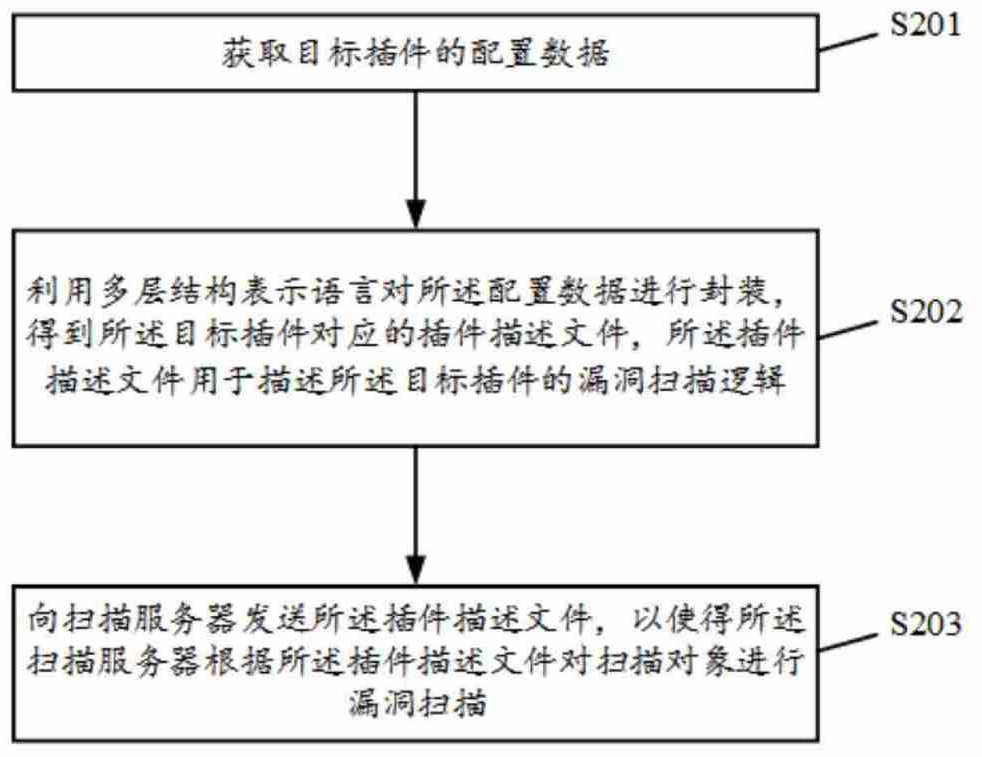
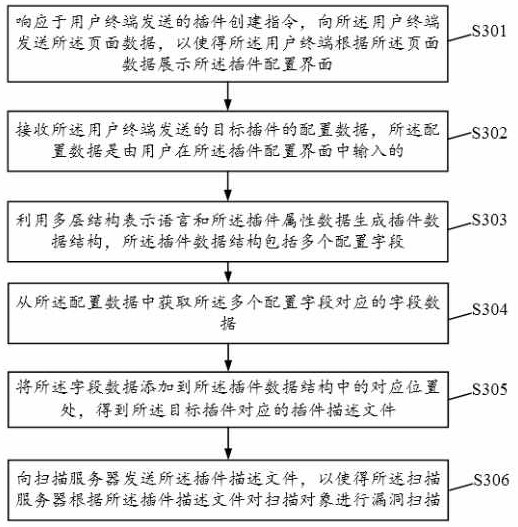
[0038] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of this application.
[0039] Cloud technology (Cloud technology) is a general term for network technology, information technology, integration technology, management platform technology, application technology, etc. based on cloud computing business model applications. Cloud computing technology will become an important support. The background services of technical network systems require a lot of computing and storage resources, such as video websites, picture websites and more portal websites. With the rapid ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More