A container application authentication method, system, computing device and readable storage medium
An application system and authentication system technology, applied in the system, container application authentication method, computing device and readable storage medium field, can solve the problem of identifying the container environment, distinguishing the physical host from the inability to realize docker internal software protection, etc., to avoid arbitrary copying Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] Exemplary embodiments of the present disclosure will be described in more detail below with reference to the accompanying drawings. Although exemplary embodiments of the present disclosure are shown in the drawings, it should be understood that the present disclosure may be embodied in various forms and should not be limited by the embodiments set forth herein. Rather, these embodiments are provided for more thorough understanding of the present disclosure and to fully convey the scope of the present disclosure to those skilled in the art.
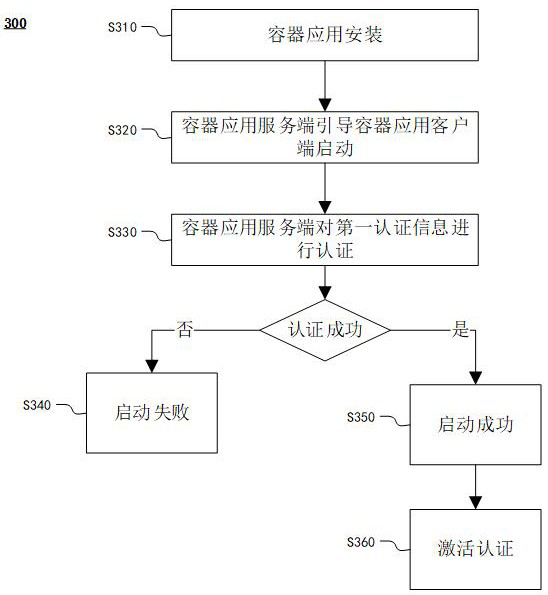
[0023] According to the characteristic that the container application can be copied and run on the same host computer, in order to prevent other copied illegal container applications from running on the host computer, the present invention provides a method of controlling and implementing the authorization authentication of the container application through the service authentication mechanism.
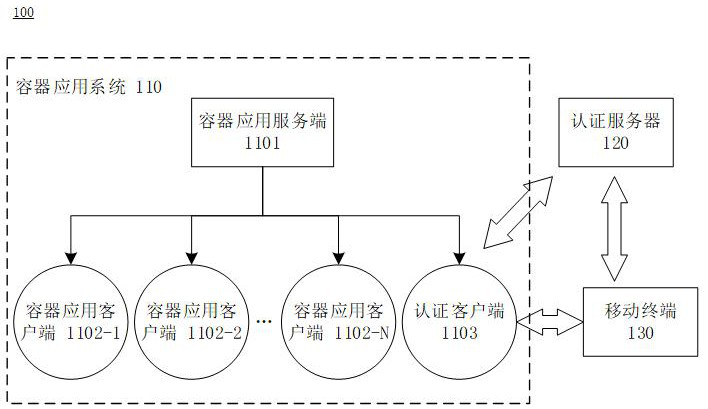
[0024] figure 1 A schematic diagram...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More