Transformer-based application layer malicious payload detection method, system, device and medium
A technology of payload and detection method, applied in neural learning methods, instruments, biological neural network models, etc., can solve the problems of non-convergence of models and loss of detailed information, and achieve the effect of accurate load detection and fast convergence
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
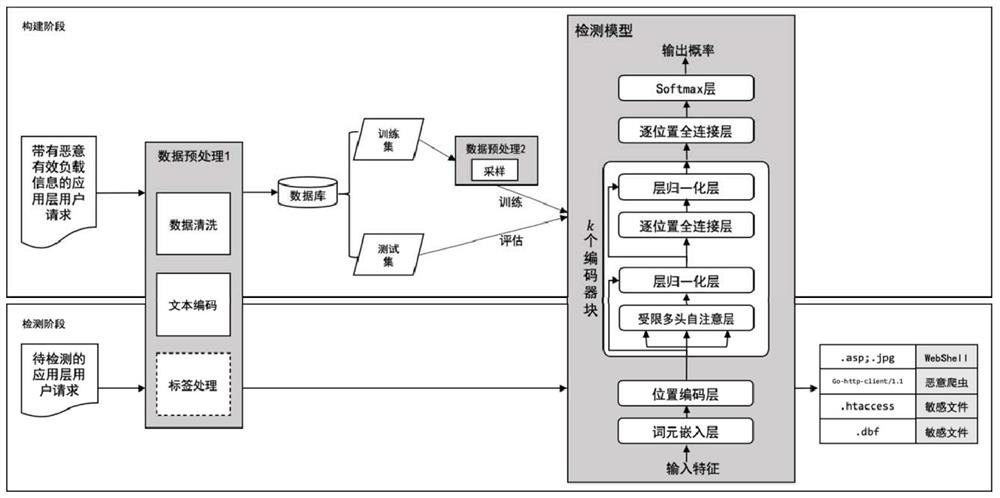
[0059] as attached figure 1 As shown, this embodiment discloses a Transformer-based application-layer malicious payload detection method, and its implementation of application-layer malicious payload detection includes two stages, namely the construction stage and the detection stage. In the construction phase, data preprocessing is first performed on application layer user requests with malicious payload information, and then a Transformer-based application layer malicious payload detection model is constructed and trained; in the detection phase, data preprocessing is first performed on application layer user requests to be detected, Then use the trained model for malicious payload detection. Below, the above two stages will be described in detail:
[0060] 1. Construction phase
[0061] 1. Data acquisition and labeling
[0062] Obtain application layer user request data through enterprise cooperation, experimental simulation, etc., and use manual marking or other methods...
Embodiment 2
[0122] This embodiment discloses a Transformer-based application layer malicious payload detection system, including:
[0123] The sample set building module is used to: construct the application layer user request sample set D, wherein each sample d i Include an application layer user request x i and its malicious payload information, which includes one or more groups of specific malicious payloads p ij and its class y ij ;The subscript i is used to distinguish different application layer user requests, and the subscript j is used to distinguish different types of malicious payloads;
[0124] The data preprocessing module is used to: convert the application layer user request sample d in D i Carry out data preprocessing to obtain a number of words composed user request and the class-true label of each lemma The l in the subscript is used to distinguish different lexical units;
[0125] The detection model training module is used for: preprocessing the data in the ap...
Embodiment 3
[0129] This embodiment discloses an electronic device, including a processor and a memory, where a computer program is stored in the memory, and when the computer program is executed by the processor, the processor implements the method described in Embodiment 1.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More