Authorization authentication method and device of application program and medium
A technology of application programs and authentication methods, which is applied in the field of network communication, can solve problems such as developer losses, and achieve the same effect as above
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
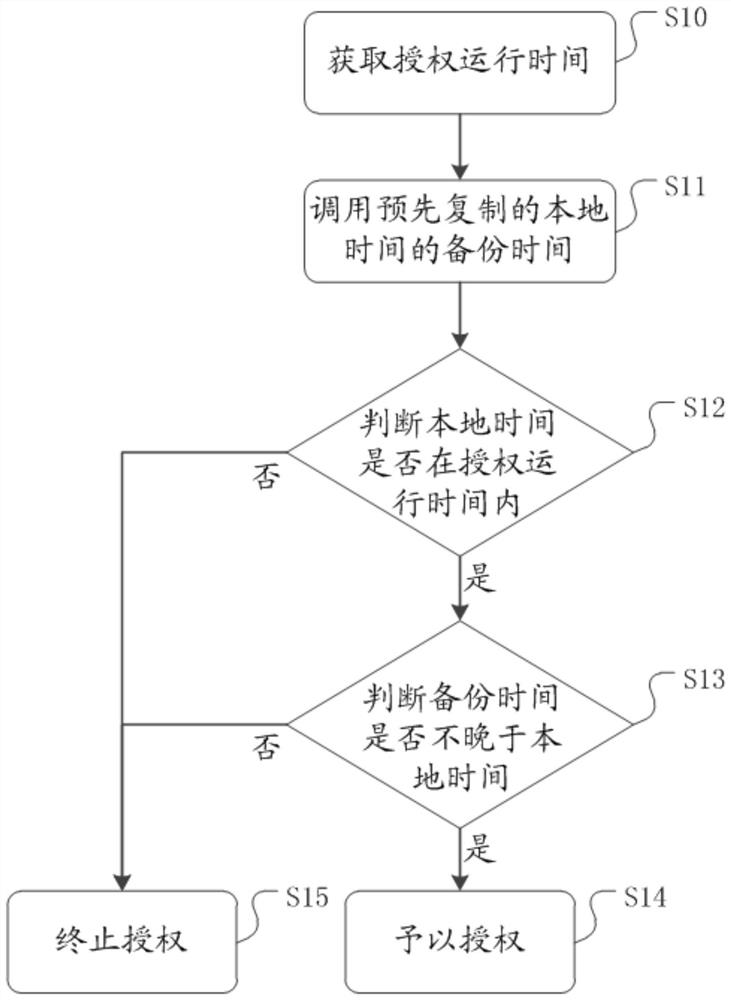
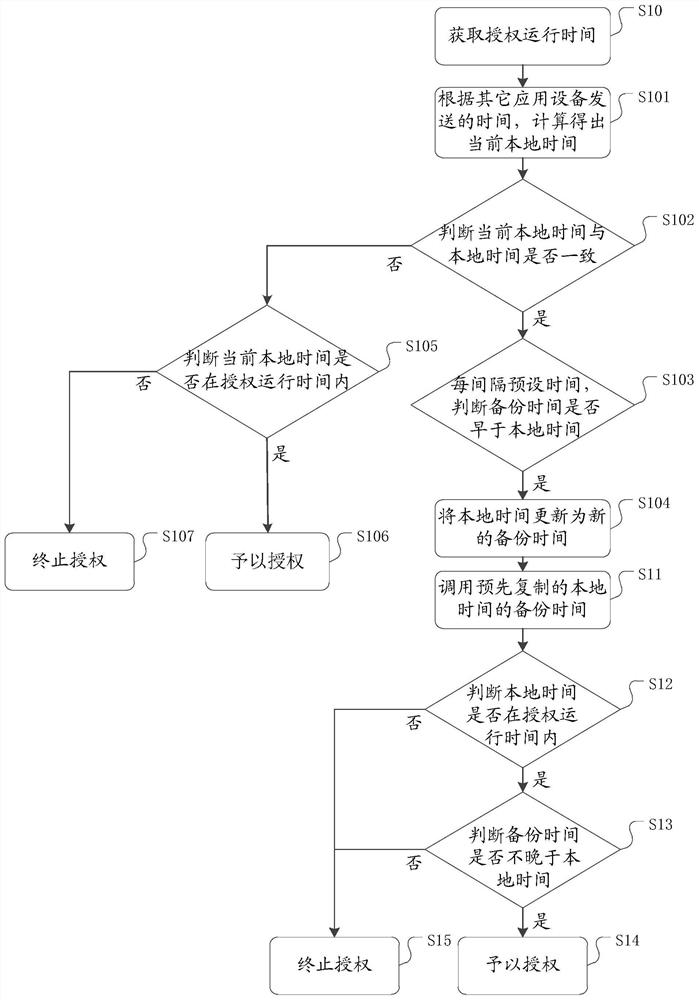
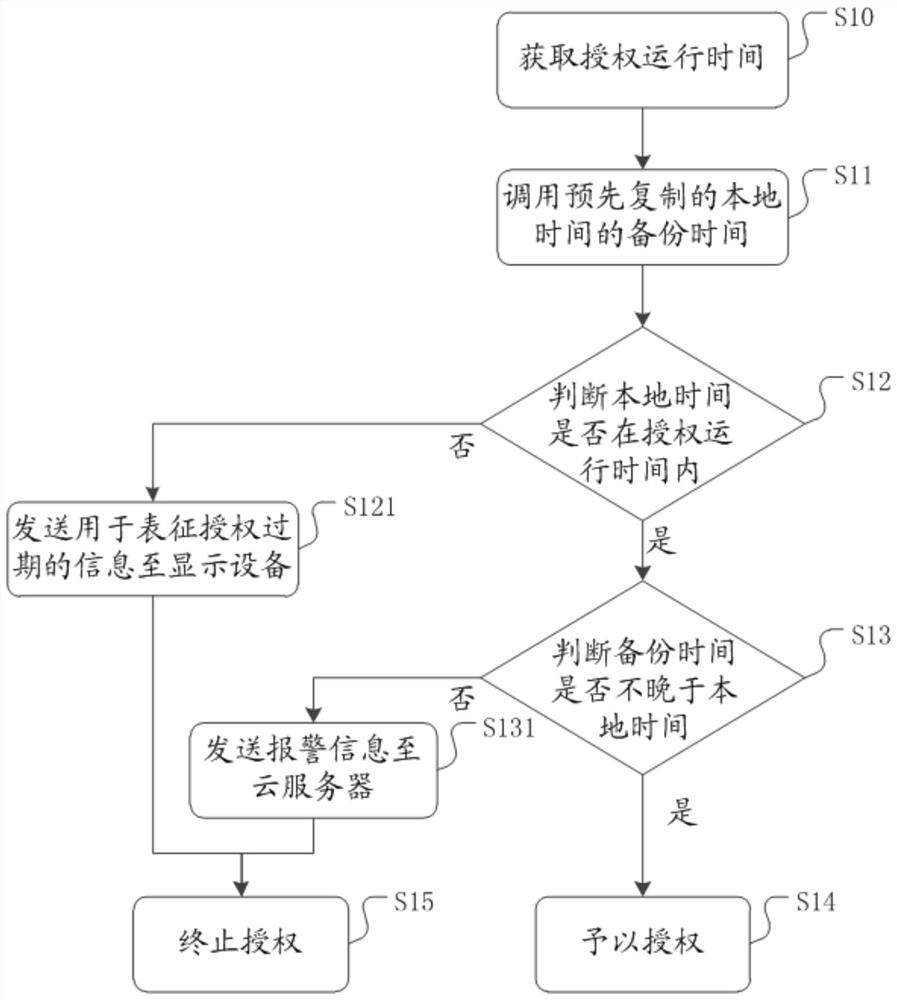
[0037] In conjunction with the following drawings of the present application example embodiments, the technical solutions in the embodiments of the present application will be clearly and completely described, obviously, the described embodiments are merely part of embodiments of the present application, but not all embodiments. Based on the embodiments in the present application, those of ordinary skill in the art without creative efforts shall, all other embodiments obtained are within the scope of protection of the present application.
[0038] Incidentally, applications typically require the processor to be loaded, for example, using a CPU (Central ProcessingUnit, central processing unit), each application has its corresponding key, the application developer when sold to the user when, also corresponding to the application key to the user, the user can use the application through the input key. When the processor to get the key, through decryption algorithm to decrypt the key,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More