Vulnerability defense method and device and computer equipment
A computer and computer program technology, applied in the direction of platform integrity maintenance, etc., can solve the problem of inability to protect the security of user equipment, and achieve the effect of improving efficiency and security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] In order to better understand the above technical solutions, the technical solutions of the embodiments of the present application will be described in detail below through the accompanying drawings and specific examples. It should be understood that the embodiments of the present application and the specific features in the embodiments are the technical solutions of the embodiments of the present application. A detailed description, rather than a limitation to the technical solutions of the present application, the embodiments of the present application and the technical features in the embodiments can be combined with each other under the condition of no conflict.
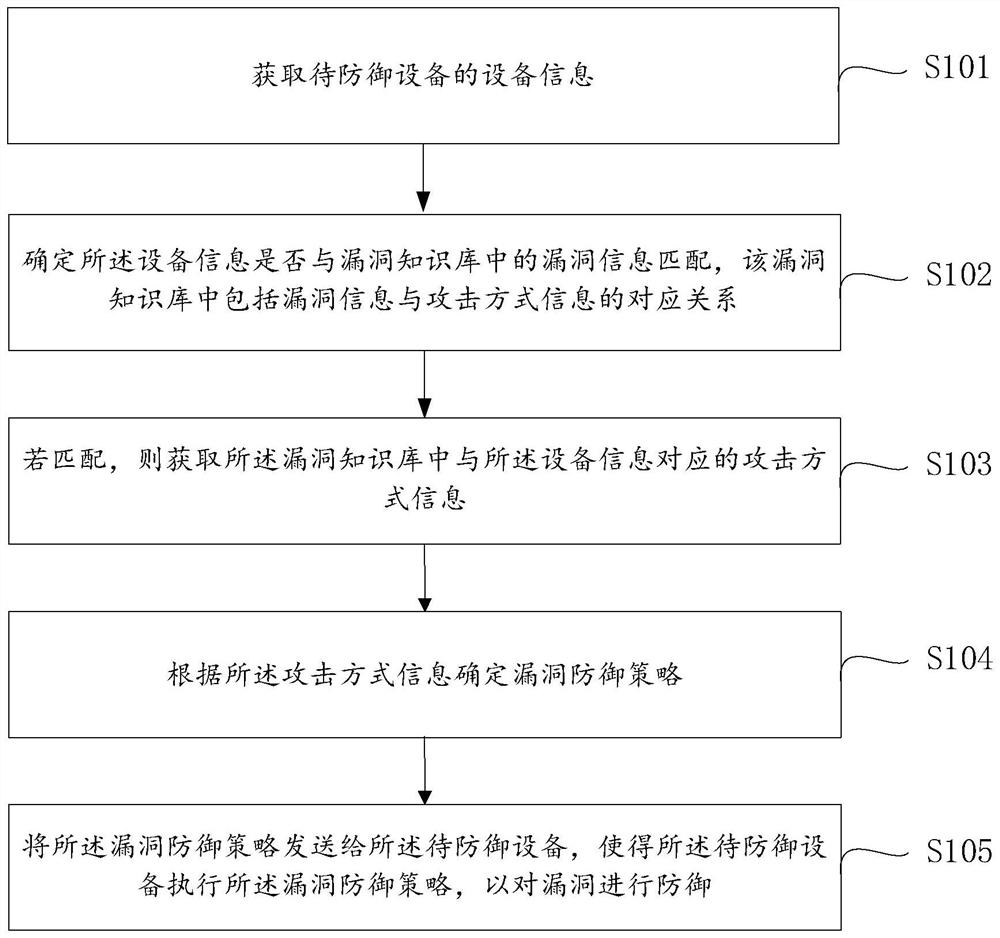
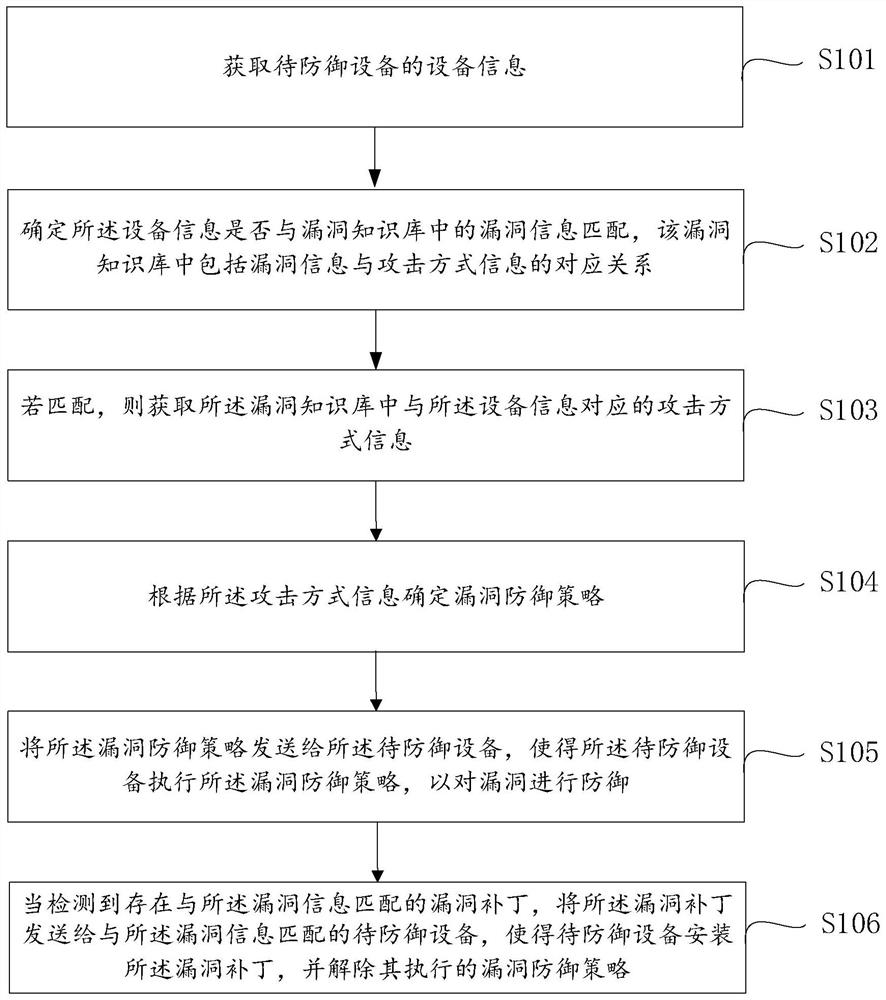
[0025] see figure 1 , a vulnerability defense method provided by an embodiment of the present invention is applied to a security monitoring center, and the method specifically includes steps S101-step S105:
[0026] Step S101, acquiring device information of a device to be defended.
[0027] Wherein, the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More