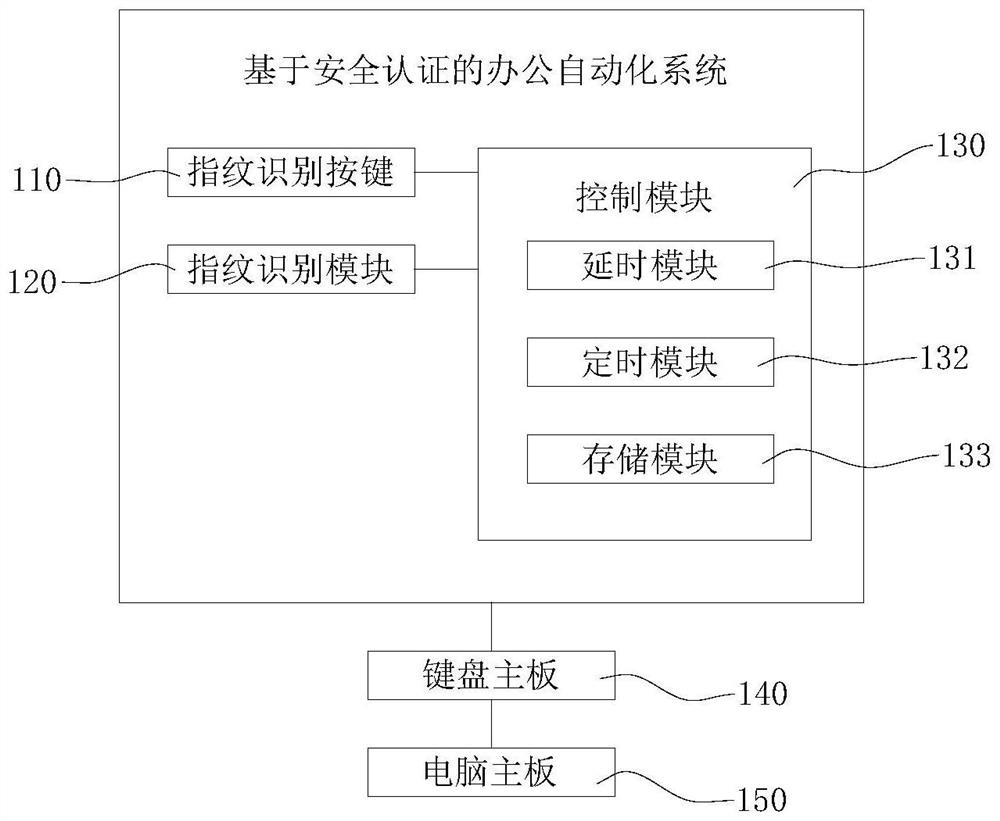
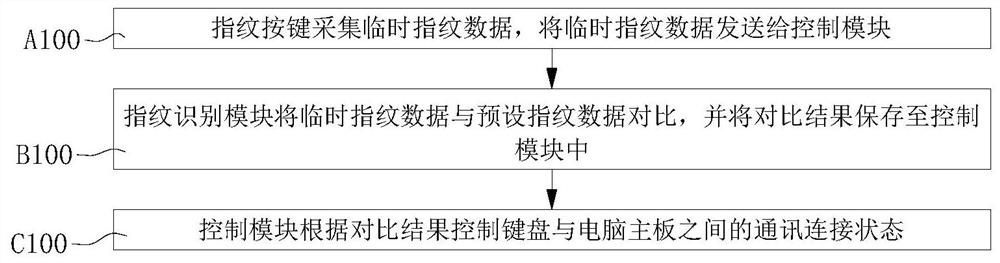
Office automation method and system based on security authentication
A technology for office automation and security authentication, applied in digital data authentication, internal/peripheral computer component protection, etc., can solve problems such as password leakage and forgetting, and achieve high security and convenient use
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] The implementation manner of the present application will be further described in detail below with reference to the drawings and embodiments. The following examples are used to illustrate the present application, but cannot be used to limit the scope of the present application.
[0046] The terms "first", "second", "third", "fourth", etc. (if any) in the specification and claims of the present application and the above drawings are used to distinguish similar objects, and not necessarily Used to describe a specific sequence or sequence. It is to be understood that the data so used are interchangeable under appropriate circumstances such that the embodiments of the application described herein, for example, can be practiced in sequences other than those illustrated or described herein. Furthermore, the terms "comprising" and "having", as well as any variations thereof, are intended to cover a non-exclusive inclusion, for example, a process, method, system, product or d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More