Method and device for protecting CC attack, medium and computer equipment
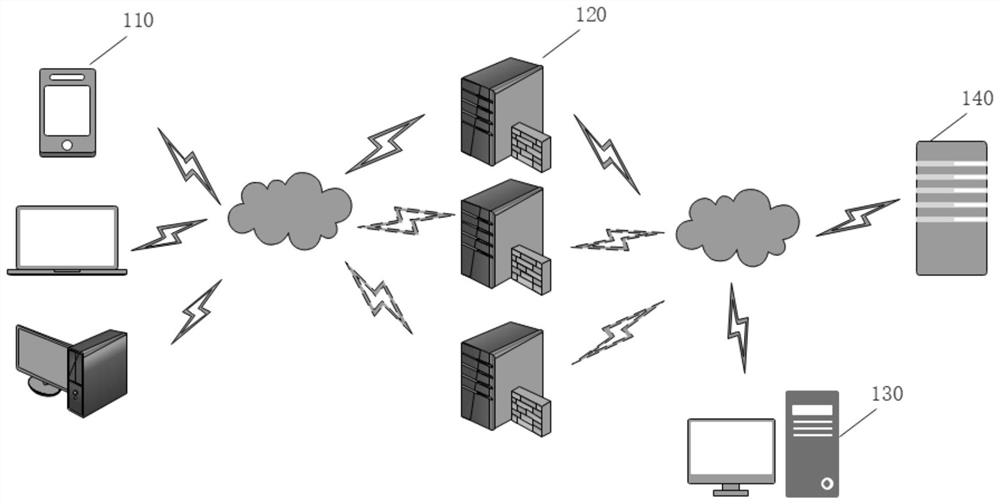
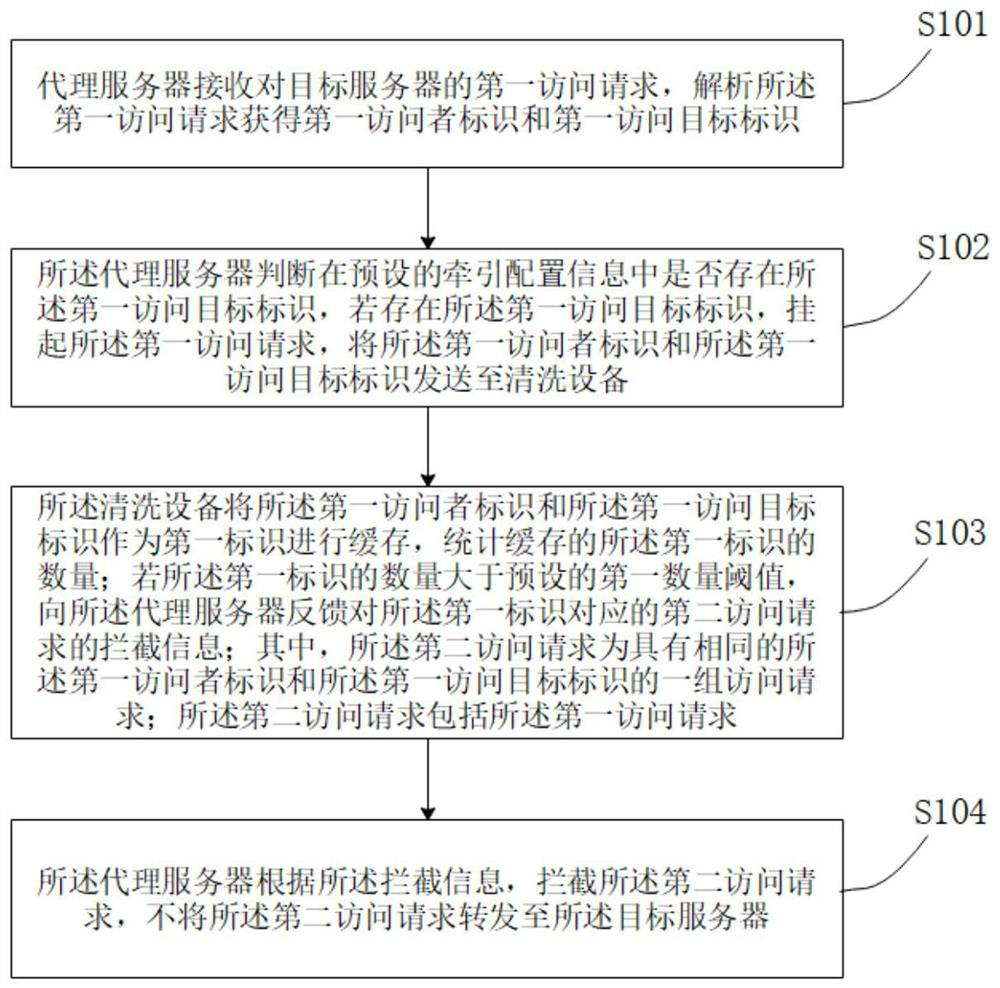
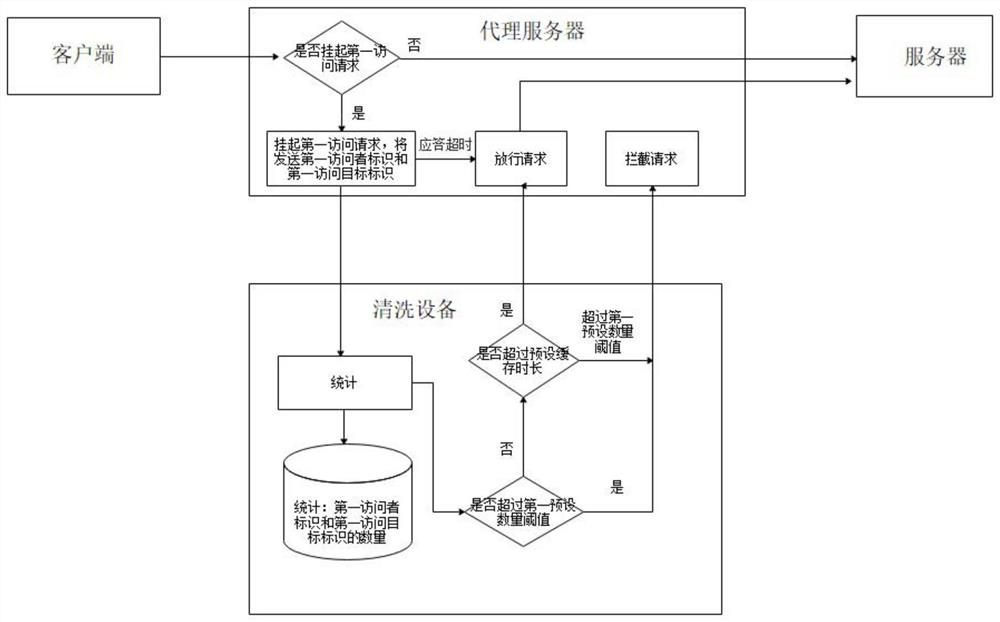
A technology for cleaning equipment and configuring information, applied in the field of network security, it can solve problems such as difficulty in prevention, exhaustion of server resources, and inability to respond to normal access requests, so as to avoid exhaustion of server resources and reduce downtime and crashes.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] In order to make the purpose, technical solution and advantages of the present application clearer, the embodiments of the present application will be further described in detail below in conjunction with the accompanying drawings.
[0034] It should be clear that the described embodiments are only some of the embodiments of the present application, rather than all of the embodiments. Based on the embodiments in the embodiments of the present application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the embodiments of the present application.
[0035] When the following description refers to the accompanying drawings, the same numerals in different drawings refer to the same or similar elements unless otherwise indicated. In the description of the present application, it should be understood that the terms "first", "second", "third", etc. are only used to distinguish similar obje...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More