Identity authentication method and device
An identity authentication and identity technology, which is applied in the field of identity authentication methods and devices, can solve the problems of identifying access controllers, requesting equipment, and network security risks, and achieve the effects of real-time authentication, exposure prevention, and confidentiality protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
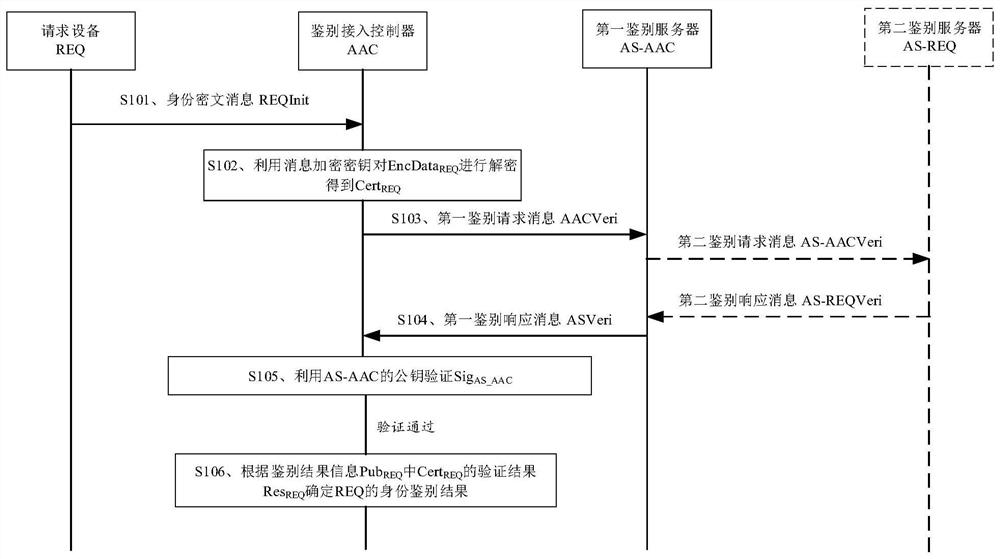
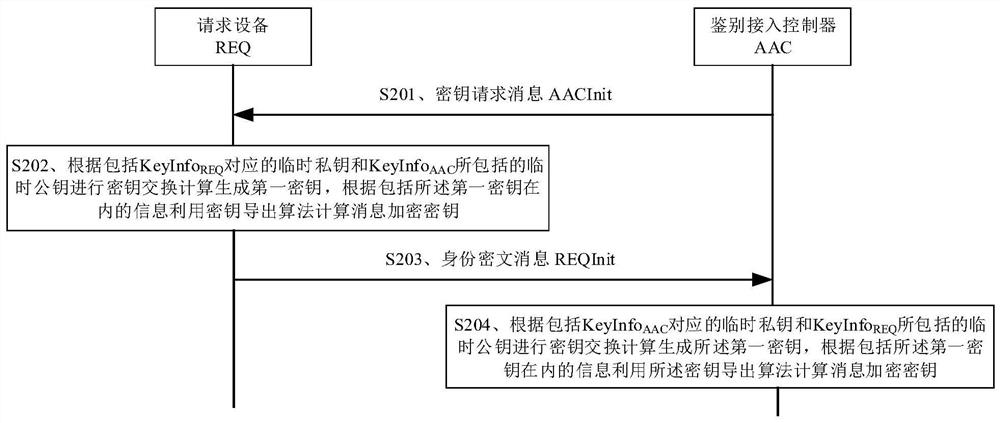
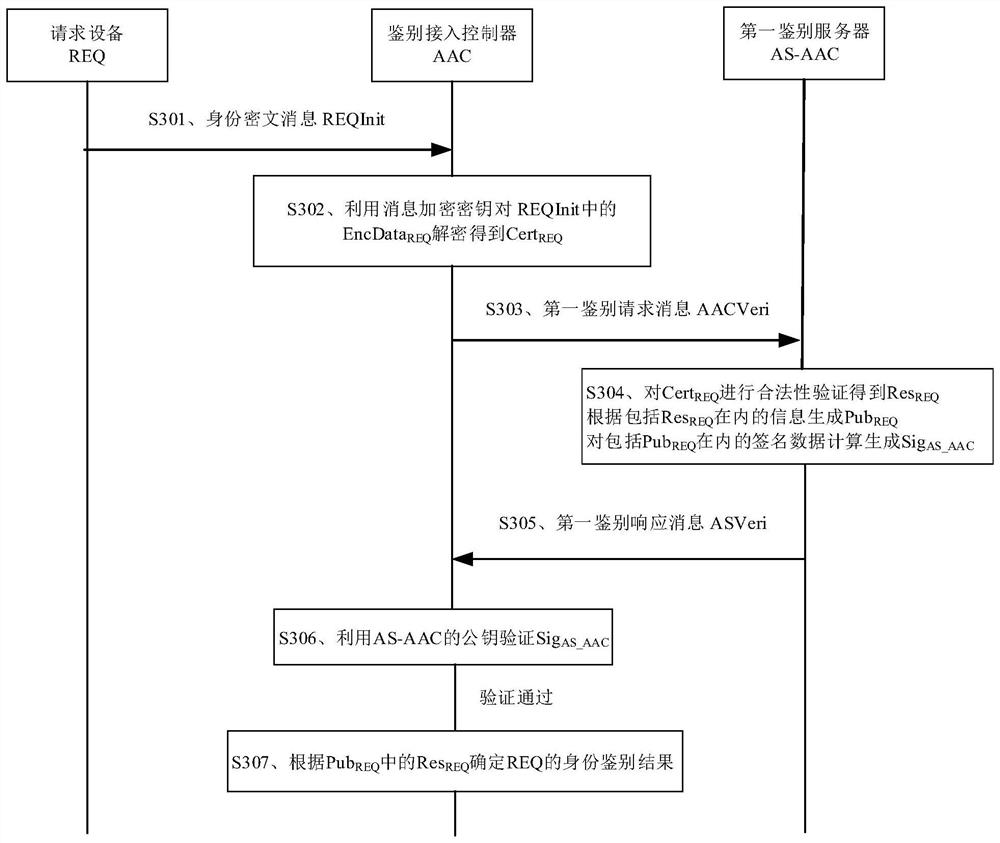
[0033] In a communication network, the requesting device can access the network through the authentication access controller. In order to ensure that the requesting device accessing the network belongs to a legitimate user, the authentication access controller needs to authenticate the identity of the requesting device.
[0034] Taking the current wireless communication and mobile communication scenarios as an example, in the scenario where the requesting device accesses the wireless network through the authentication access controller, the requesting device may be a mobile phone, a personal digital assistant (PDA), a tablet computer, etc. The terminal device, the authentication access controller can be a network side device such as a wireless access point and a wireless router. In the scenario where the requesting device accesses the 4th / 5th Generation mobile communication technology (4G / 5G) network through the authentication access controller, the requesting device may be a t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More