Network authentication and key allocation method across secure domains
A technology of key distribution and network authentication, applied in the field of network authentication and key distribution across security domains, can solve the problems of high complexity, cumbersome, inconvenient management, etc., and achieve the effect of preventing infiltration into the network
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0050] The present invention will be described in further detail below with reference to the accompanying drawings.
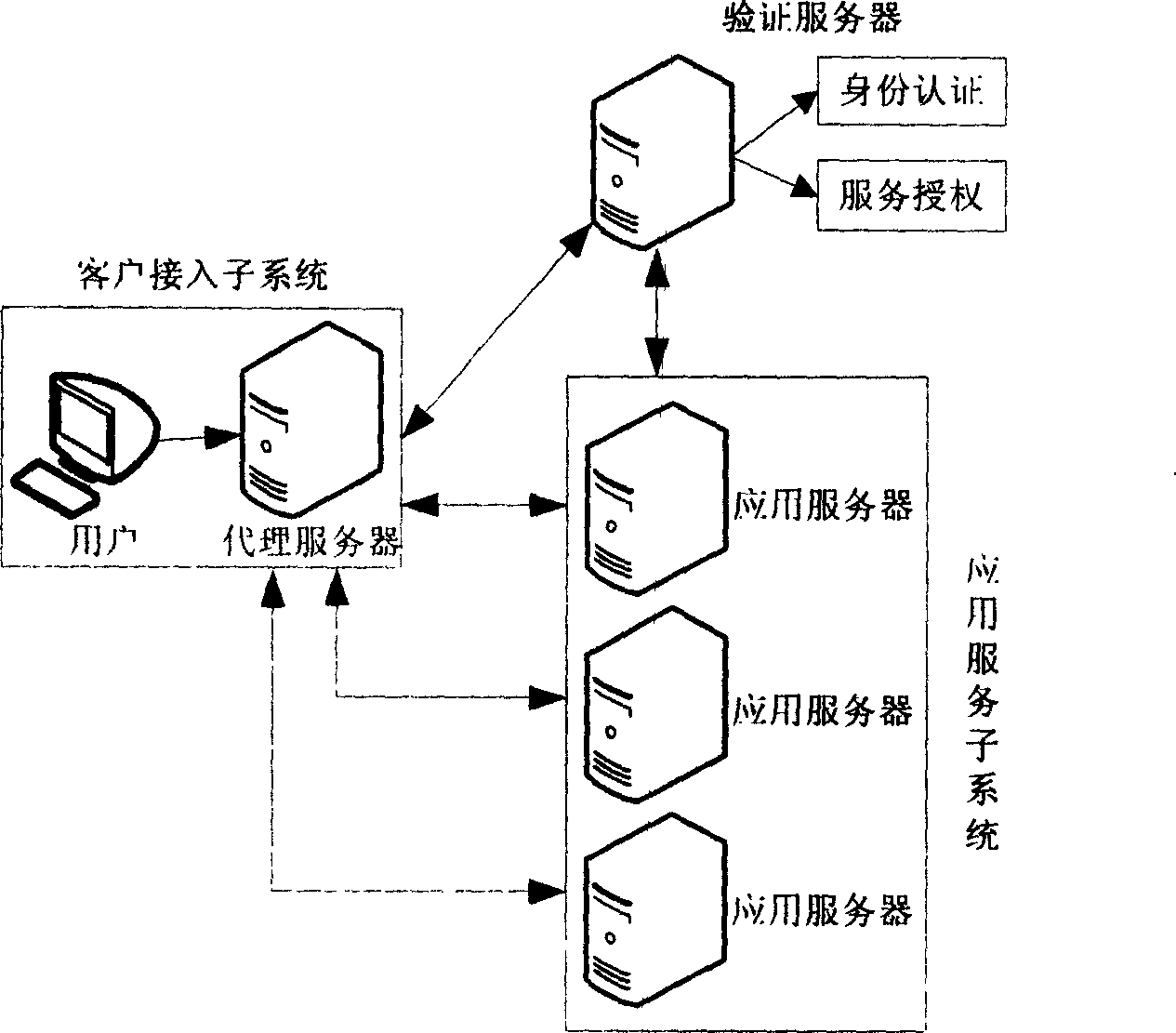
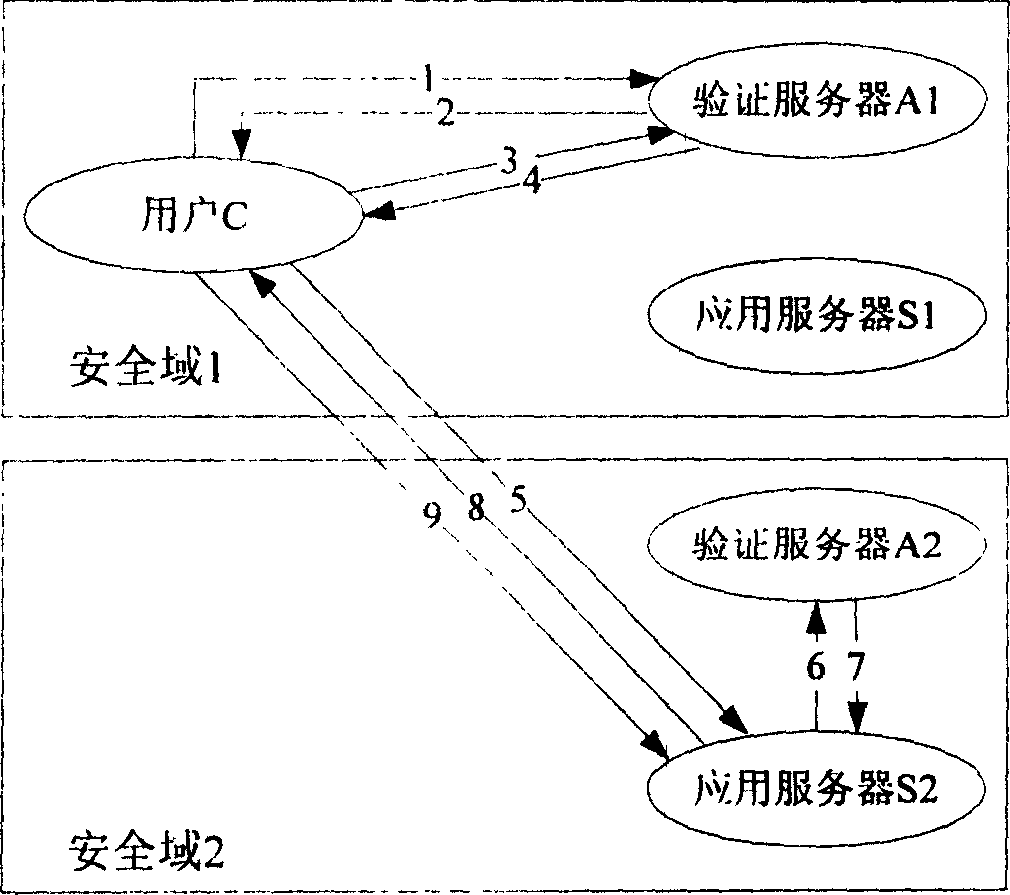
[0051] refer to figure 1 , The cross-security domain network authentication and key distribution system of the present invention includes: a verification server, a client access subsystem, and an application service subsystem. Among them, the client access subsystem is composed of users and proxy servers; the application service subsystem is composed of several application servers. The working process of the system is:
[0052] First, in the client access subsystem, the user accesses the authentication server through a proxy server, and forwards the user's public key certificate and user identity information with digital signature to the authentication server. The proxy server only plays a role in the authentication process. "Transparent transmission" function, the user authentication work is completed by the authentication server.
[0053] Secondly, after r...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More