Network controller, network control system and network control method
A network control and network technology, which is applied in the direction of transmission system, digital transmission system, data exchange network, etc., can solve the problem of difficult to prevent traffic error control, no consideration, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
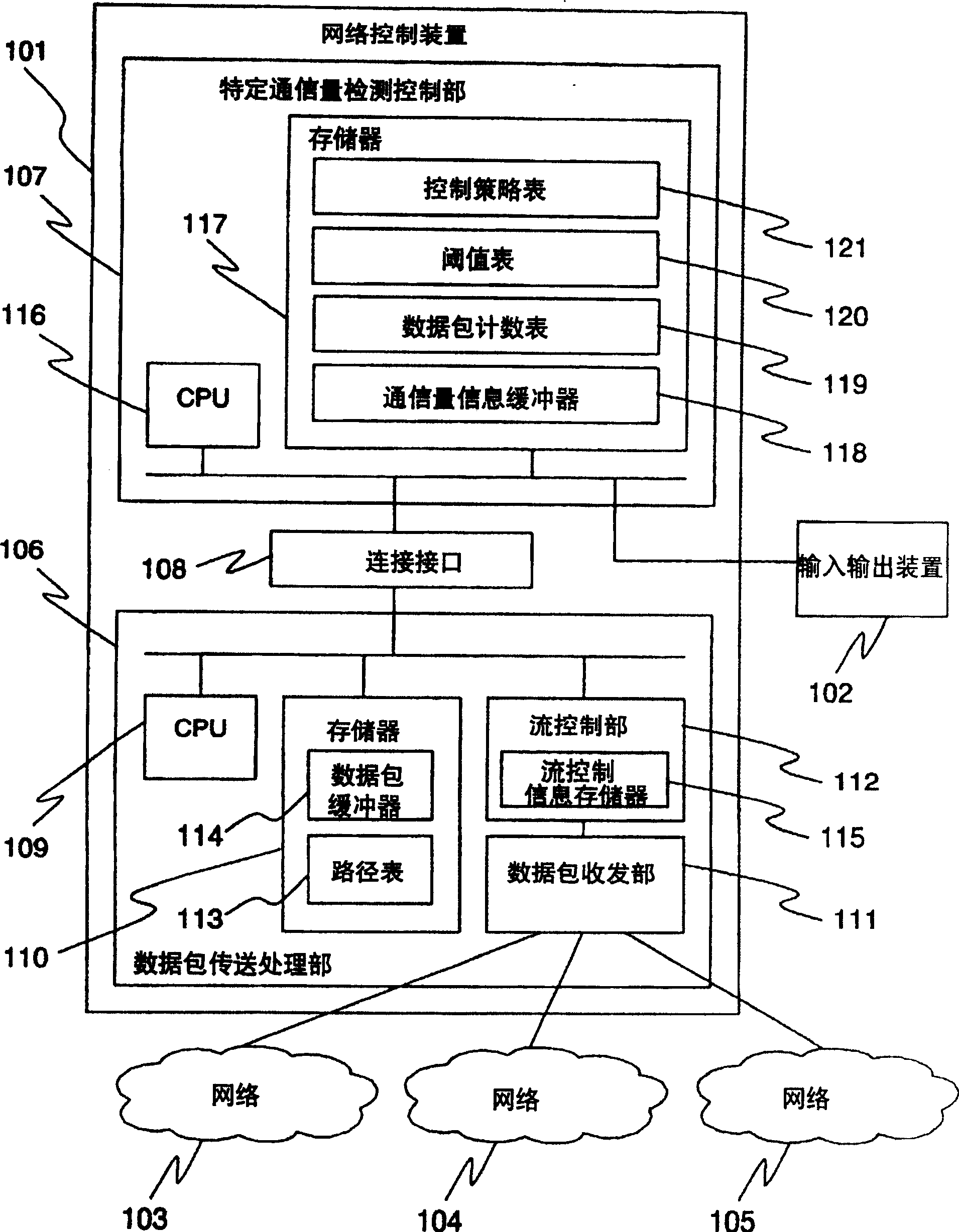
[0042] Example 1 will be described. figure 1 A configuration diagram of a network control device according to an example of this embodiment is shown. In the figure, 101 is the network control device of this embodiment, 102 is an input / output device for giving instructions to the network control device 101 or displaying the status, and 103 , 104 , 105 are networks connected to the network control device 101 .
[0043] The network control device 101 is composed of a packet transfer processing unit 106 and a specific traffic detection control unit 107 . The connection interface 108 connects the packet transfer processing unit 106 and the specific traffic detection control unit 107 , and enables data exchange between the packet transfer processing unit 106 and the specific traffic detection control unit 107 .
[0044]The packet transfer processing unit 106 includes a CPU 109 , a memory 110 , a packet transceiver unit 111 for transmitting and receiving packets between the networks...
Embodiment 2
[0099] Example 2 will be described. Figure 11 A configuration diagram of a network control system according to a second example of this embodiment is shown. In the figure, 1101 is a packet transfer processing device that performs packet transfer between the networks 103, 104, and 105, and 1102 is a network control device that analyzes information received from the packet transfer processing device.
[0100] The packet transfer processing device 1101 includes a CPU 1103 , a memory 1104 , a packet transmission and reception unit 1105 for transmitting and receiving packets between the networks 103 , 104 , and 105 and the network control device 1102 , and a flow control unit 1106 . The memory 1104 includes a route table 1107 for determining a network to be transferred according to the destination address included in the packet, and a packet buffer 1108 for temporarily storing packets received by the packet transceiver 1105 . In addition, the flow control unit 1106 includes a flo...
Embodiment 3
[0117] Example 3 will be described. Figure 13 is shown figure 2 The diagram of another embodiment of the packet count table 119 in Embodiment 1 shown in the above is similar to the packet count table 119 for generating arbitrary combinations of items constituting the traffic information and performing combinations including the above items. A table of the cumulative number of packets processed.
[0118] In the case of this embodiment, the items constituting the above traffic information include source IP address (srcip), receiver IP address (dst ip), source port number (src port), and receiver port number (dst port). Generating any combination of n items (1≦n≦4) from the above four types of items.
[0119] In addition, in this embodiment, the processing target items are set to the above four types, but other items may be further added or deleted according to the characteristics of the traffic to be detected. For example, flag information in the TCP header may be included ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More