Method and apparatus for preventing reject access aggression
A technology of denying access and purpose, applied in the network field, can solve the problem of inability to accurately judge the legitimacy of the connection, and achieve the effect of low cost, high reliability and high speed.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be described in further detail below in conjunction with the embodiments and accompanying drawings. Here, the exemplary embodiments and descriptions of the present invention are used to explain the present invention, but not to limit the present invention.
[0041] Embodiments of the present invention provide a method and device for preventing access denial attacks. The present invention will be described in detail below in conjunction with the accompanying drawings.
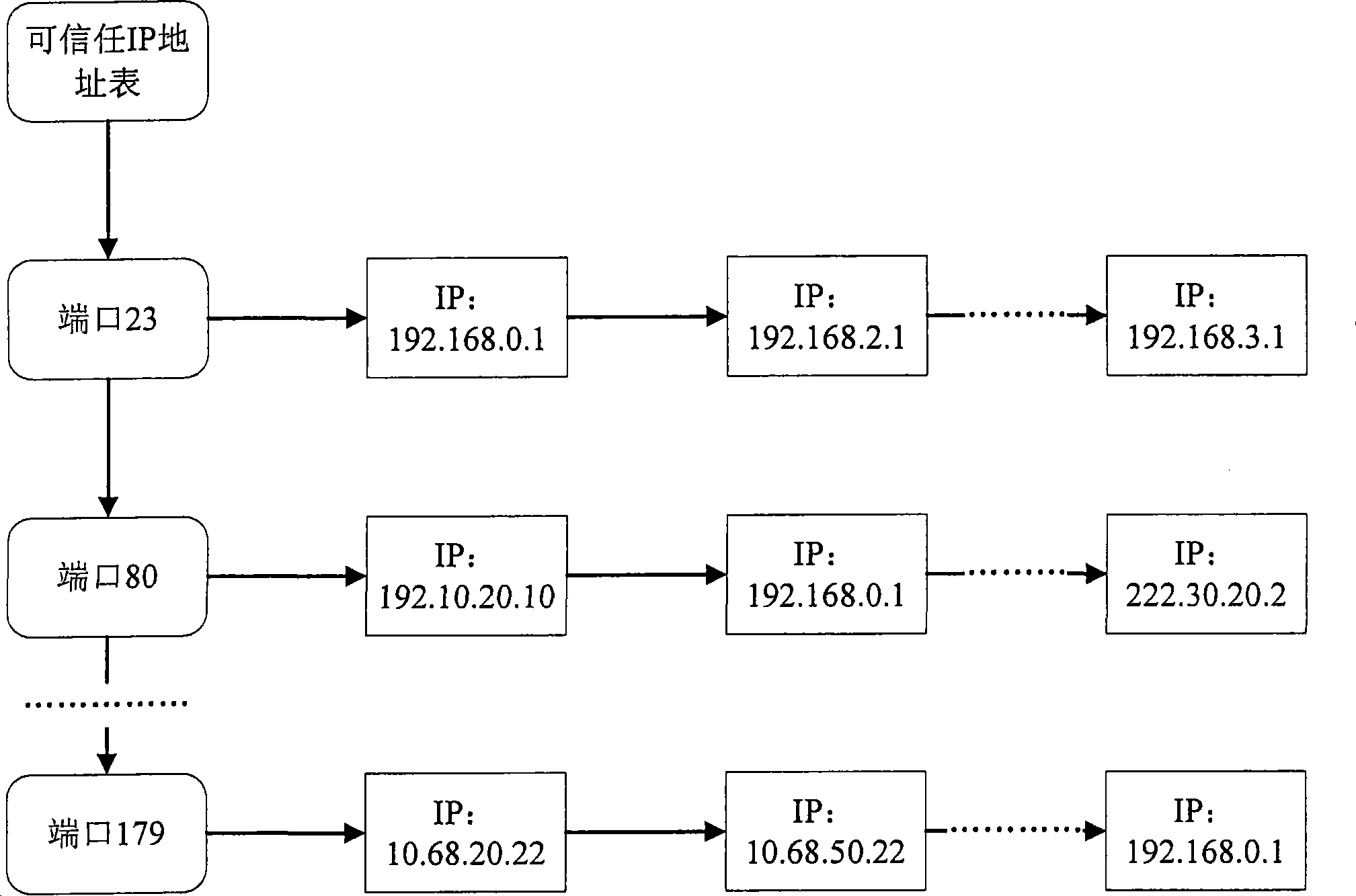
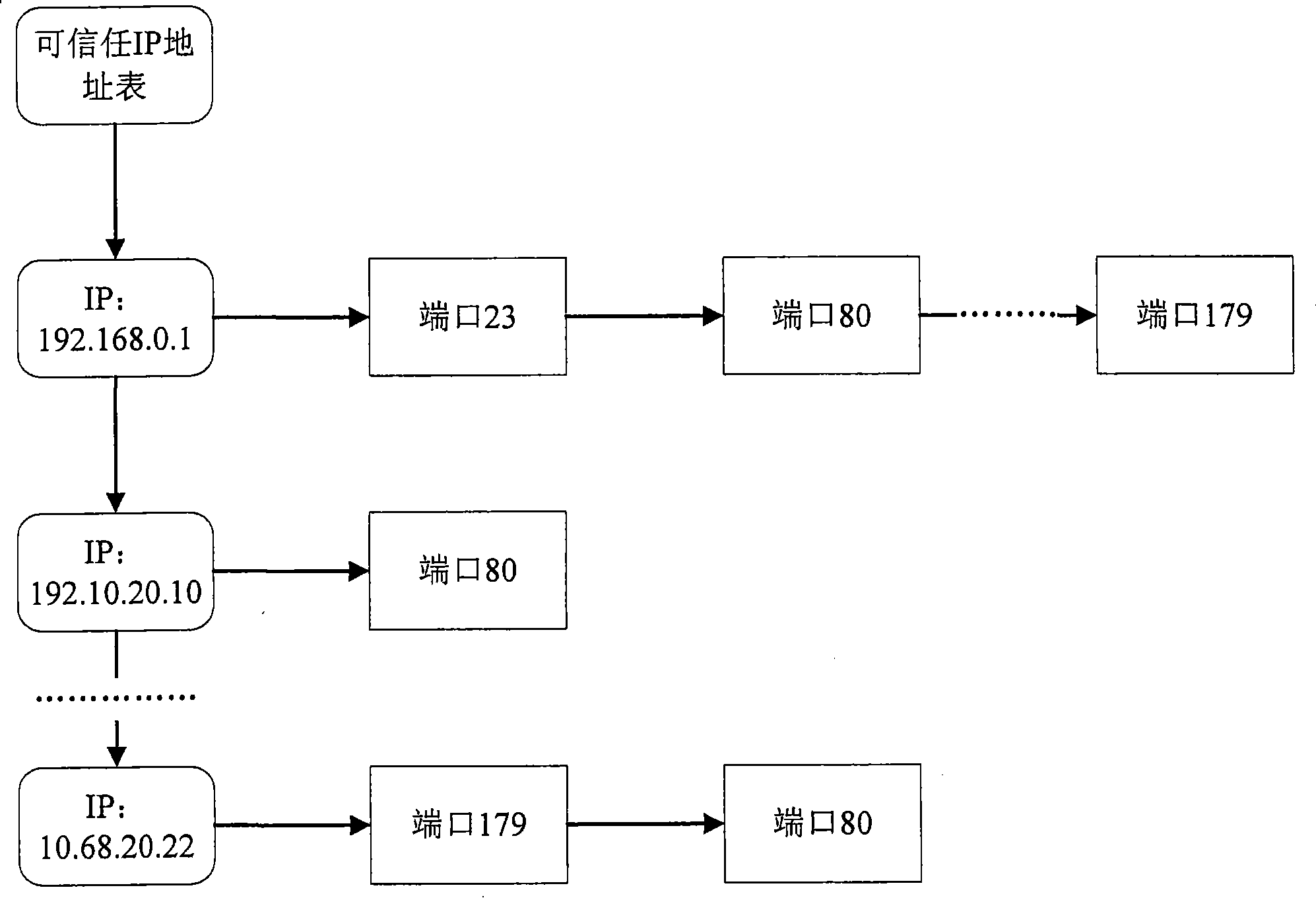
[0042] Such as figure 2 Shown is a schematic diagram of the trusted IP address table established in the first embodiment of the present invention. The trusted IP address table shown in the figure is configured on the server or relay device in the network. The IP addresses in the table are all for The trusted IP address of a certain service port, which restricts the source IP addre...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More