Secret communication method for implementing wireless local area network by using multi-algorithm
A wireless local area network and secure communication technology, applied in the field of secure communication, can solve the problems of insufficient storage capacity of wireless access points, heavy key management tasks, etc., and achieve data security improvement, security assurance, and system resource saving Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
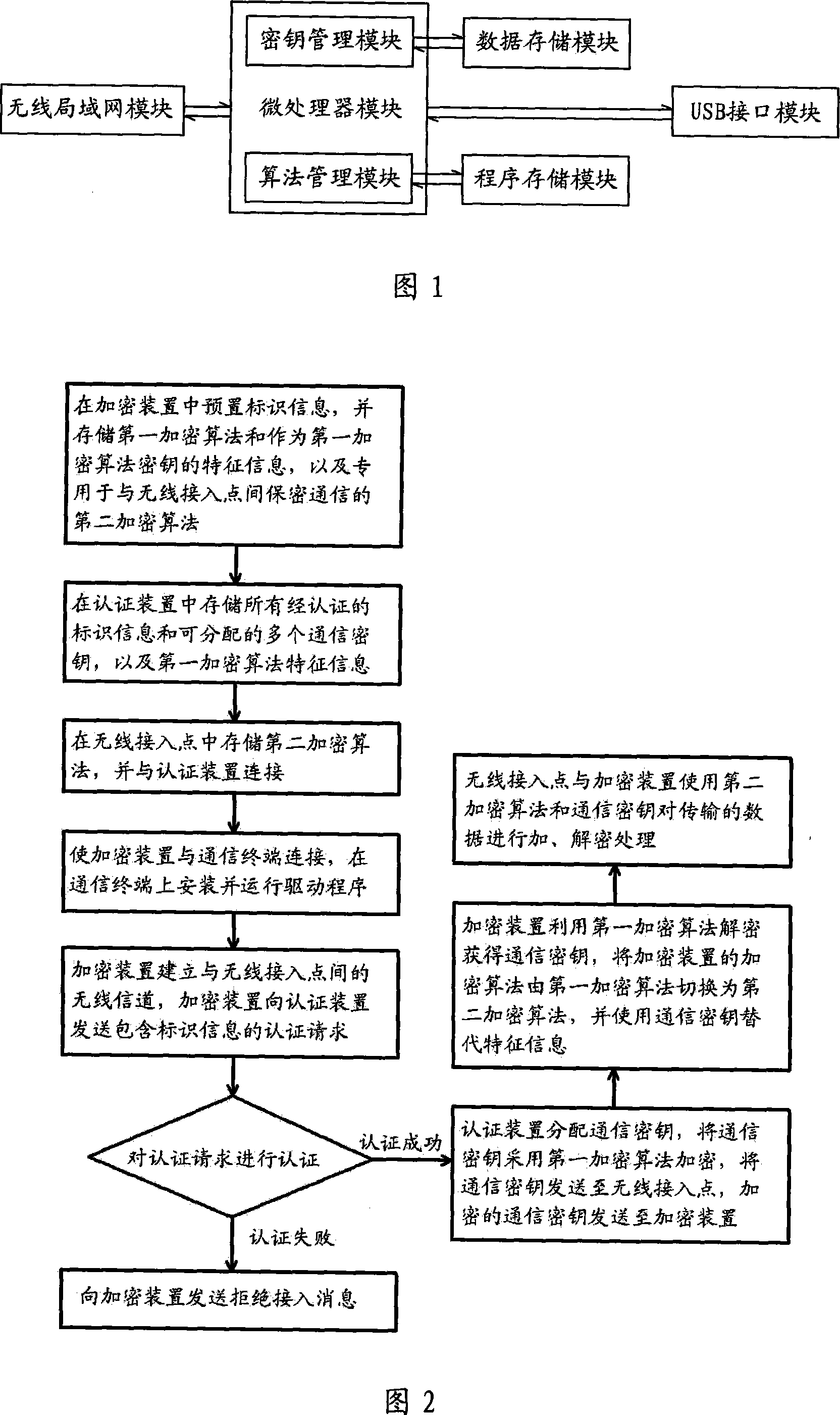
[0020] In order to further illustrate the technical means and functions adopted by the present invention to achieve the intended purpose, the detailed description is as follows in conjunction with the accompanying drawings and embodiments.
[0021] see figure 1 Shown is the structural block diagram of encryption device of the present invention, and this encryption device comprises:
[0022] Microprocessor module: responsible for data calculation, by calling the data and programs in the data storage module and program storage module, to perform encryption and decryption operations, to complete the encryption and decryption of the information transmitted in the communication, and to prepare to send it through the wireless LAN module The data is encrypted, and the data obtained through the wireless LAN module is decrypted.
[0023] Program storage module: connected with the microprocessor module, it mainly stores two or more encryption algorithms and integrity protection algorit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More