TOCTOU attack response method aiming at TPM trusted computation
A technology of trusted computing and equipment, applied in computing, computer security devices, instruments, etc., can solve the problem of not reflecting the current security status of the customer virtual domain platform, achieve strong scalability, maintain effective utilization, and defend against TOCTOU attacks. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
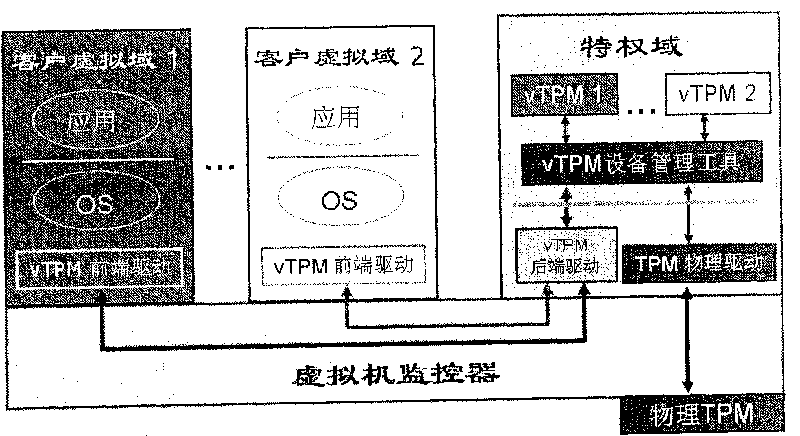
[0022] The invention assumes figure 2 system and image 3 The detection system has been deployed, and the deployment steps of the response method of the present invention are provided below:
[0023] Step 1, replace the vTPM device program with enhanced functions figure 2 method provided by the vTPM device program.
[0024] Step 2, loading the privileged domain proxy module in the privileged domain.
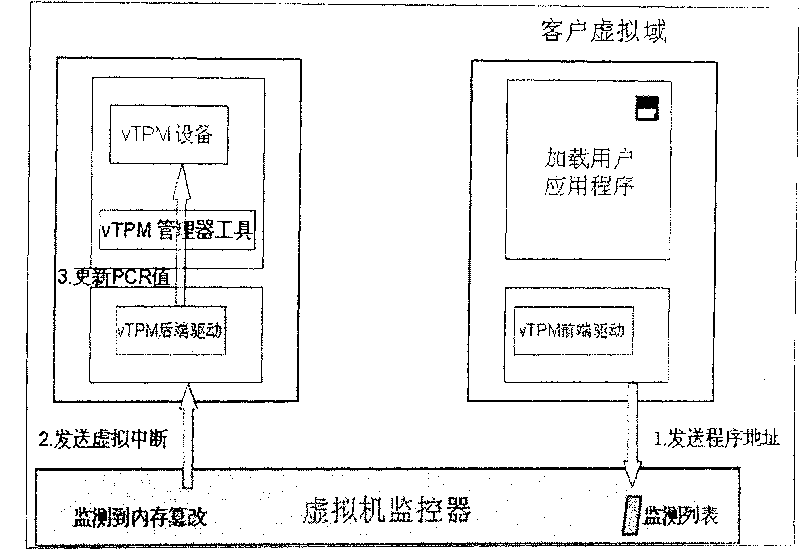
[0025] Combine below Figure 4 and Figure 5 The workflow of the present invention's design TOCTOU attack response method is described in detail:
[0026] (1) When the privileged domain proxy module receives the TOCTOU attack message from the virtual machine monitor, it will immediately create a specific flag file in the / proc directory, and set the content to 1, indicating that the virtual domain memory has been tampered with.
[0027] (2) When the function-enhanced vTPM device program receives the TPM command from the customer's virtual domain, it does not process the T...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More