Method and system based on EAP authentication
An authentication terminal and authentication information technology, applied in the field of information security, can solve problems such as low security and inconvenient unified management
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
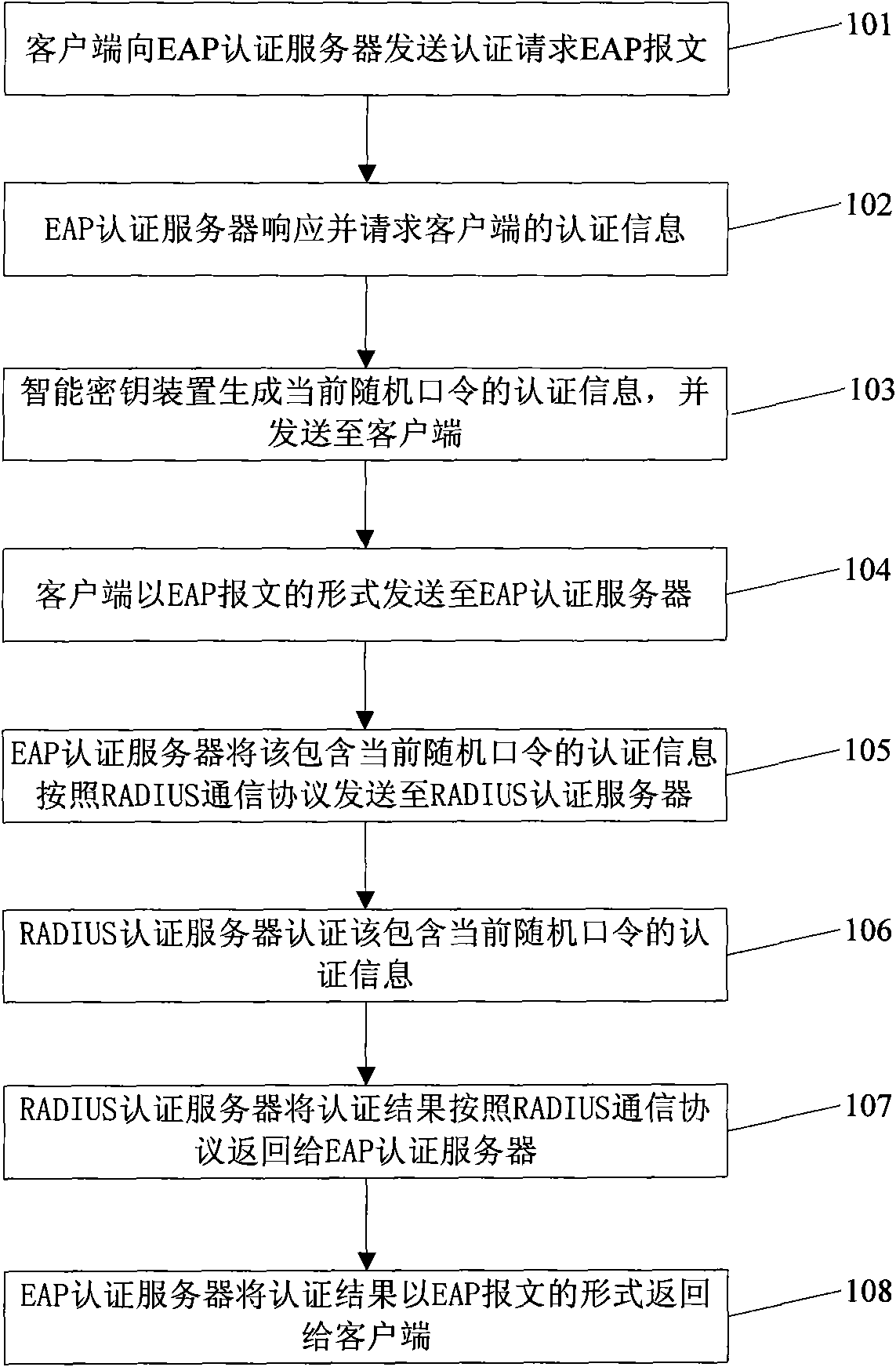
[0094] see figure 1 , the embodiment of the present invention provides a method based on EAP authentication, which specifically includes the following steps:
[0095] Step 101: the client sends an authentication request EAP packet to the EAP authentication server.
[0096] Step 102: The EAP authentication server responds and requests authentication information of the client.
[0097] The EAP authentication server may also be other forms of network access control terminals, such as routers.
[0098] Step 103: The smart key device generates the authentication information of the current random password and sends it to the client.
[0099] The step of generating the current random password by the smart key device is specifically: the smart key device calculates the built-in generating elements according to the preset random password algorithm to generate the current random password. The generation element is a time generation element, an event generation element, or the like. ...
Embodiment 2
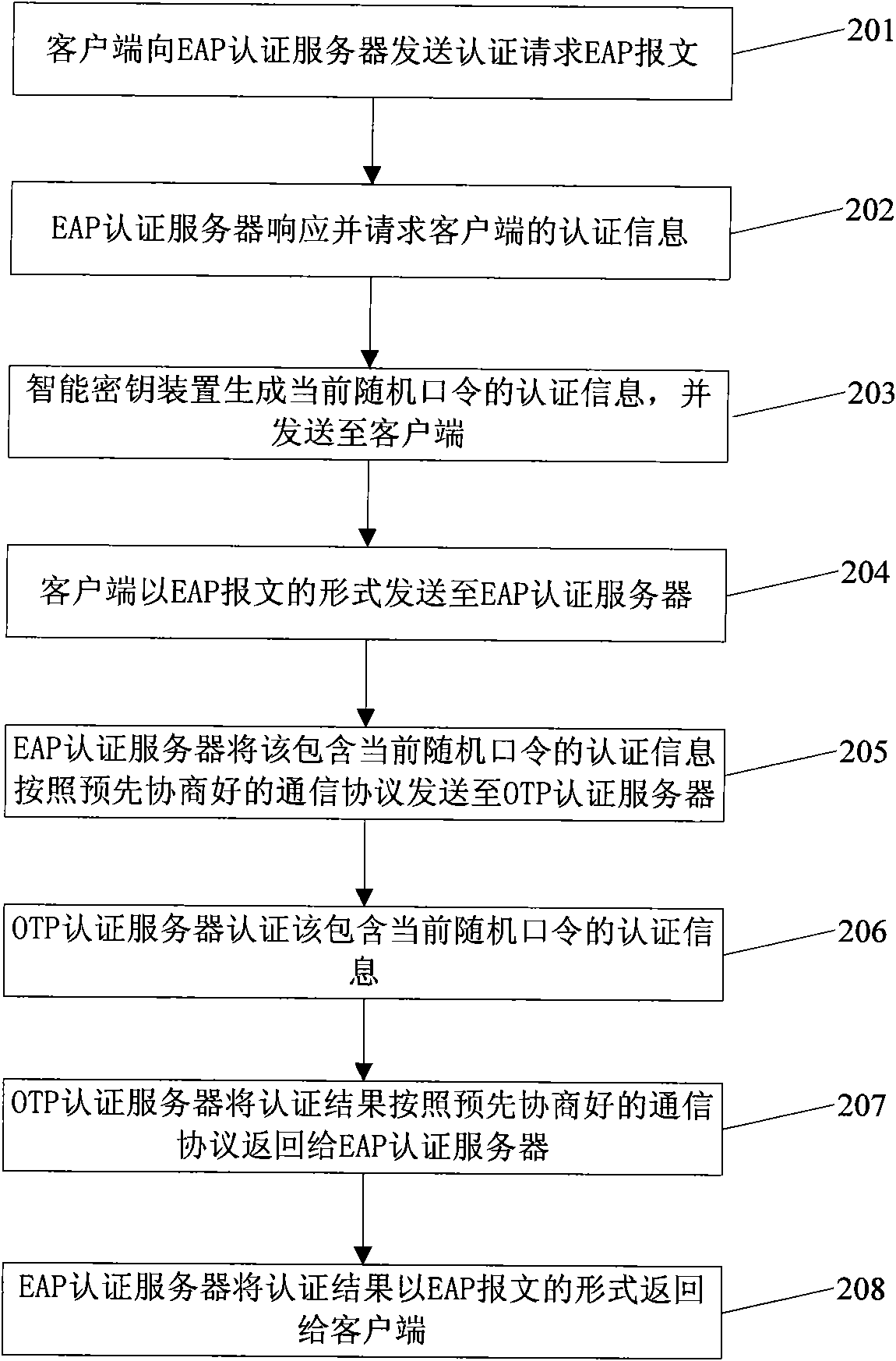
[0113] see figure 2 , the embodiment of the present invention provides a method based on EAP authentication, which specifically includes the following steps:
[0114] Step 201: the client sends an authentication request EAP packet to the EAP authentication server.
[0115] Step 202: The EAP authentication server responds and requests authentication information of the client.
[0116] The EAP authentication server may also be other forms of network access control terminals, such as routers.
[0117] Step 203: The smart key device generates the authentication information of the current random password and sends it to the client.
[0118] The step of generating the current random password by the smart key device is as follows: the smart key device calculates the built-in generating elements according to the preset random password algorithm to generate the current random password. The generation element is a time generation element, an event generation element, or the like. A...
Embodiment 3
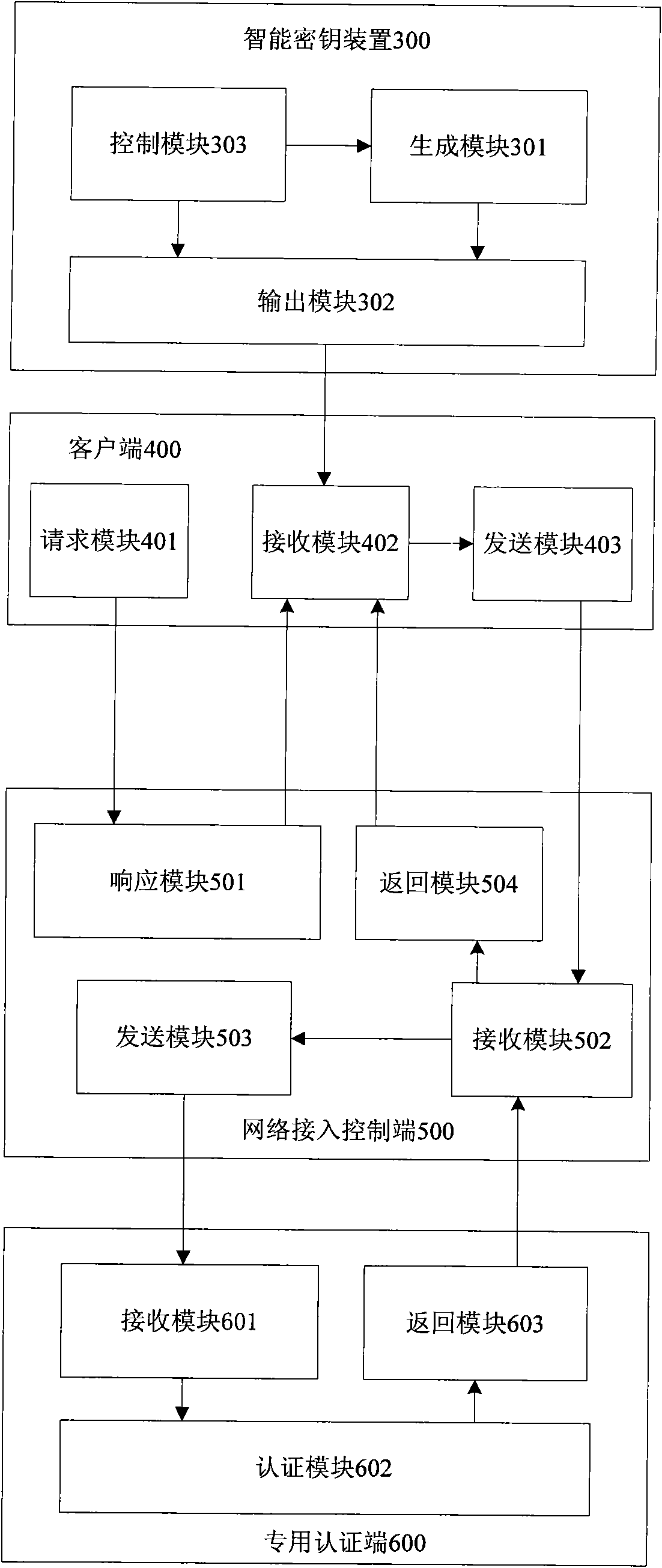
[0136] see image 3 , the embodiment of the present invention provides a system based on EAP authentication, including a smart key device 300, a client 400, a network access control terminal 500 and a dedicated authentication terminal 600,
[0137] The smart key device 300 includes a generation module 301, an output module 302 and a control module 303:
[0138] The generation module 301 is used to generate the current random password according to the preset random password algorithm under the control of the control module 303, and send the current random password to the output module 302;
[0139] The output module 302 is used to send the authentication information including the current random password to the client 400 under the control of the control module 303;
[0140] The control module 303 is used to control the generating module 301 to generate the current random password, and control the output module 302 to output the authentication information including the current ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com