User access control method
An access control and user technology, applied in the communication field, can solve problems such as the inability to guarantee the security performance of the 3GHNB system, and achieve the effect of reducing complexity and improving security performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
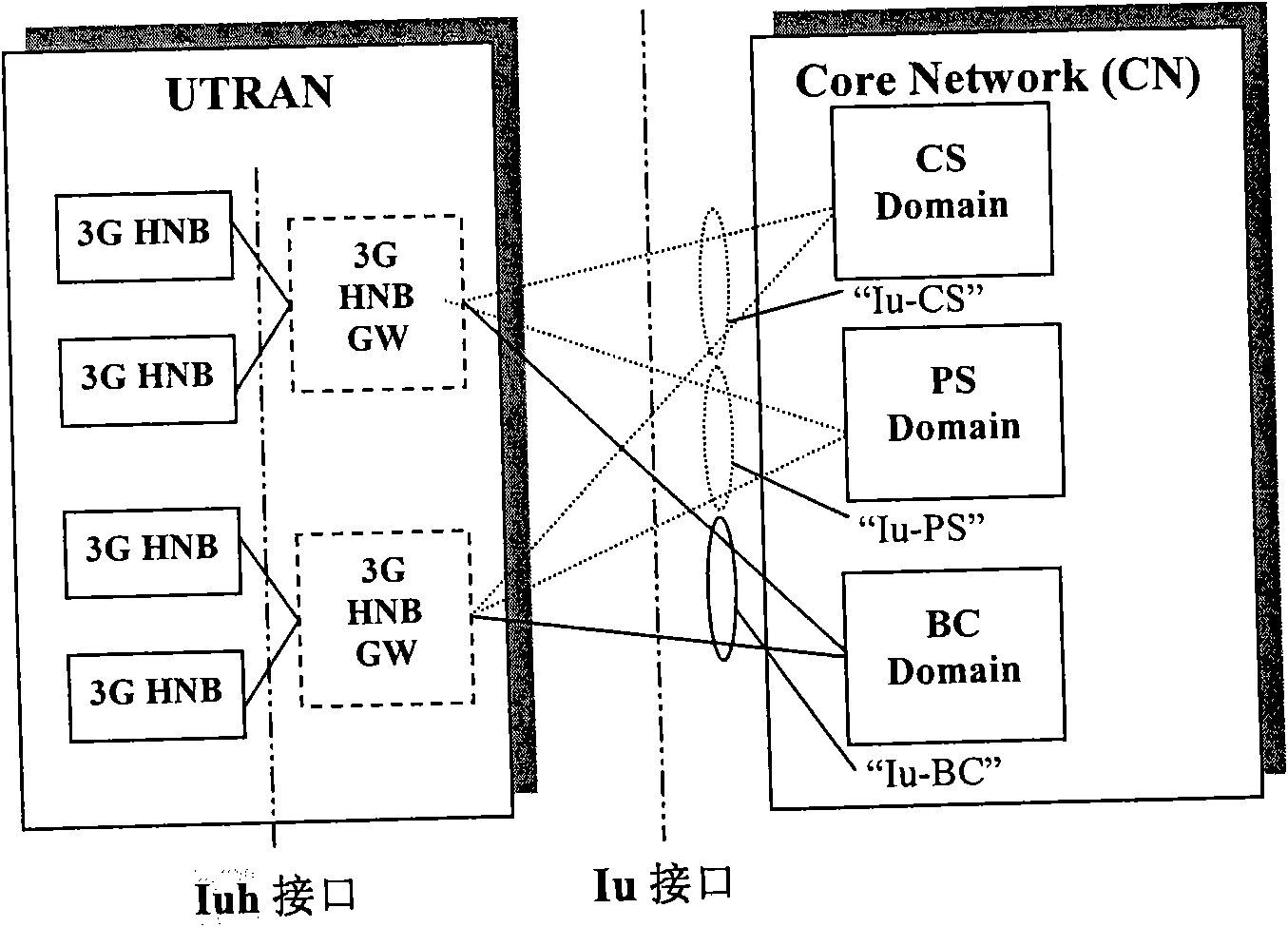
[0024] The embodiment of the present invention is described by taking 3G HNB as an example, but the present invention is not limited to 3G HNB, and also includes LTE HNB and HNB under other access systems.
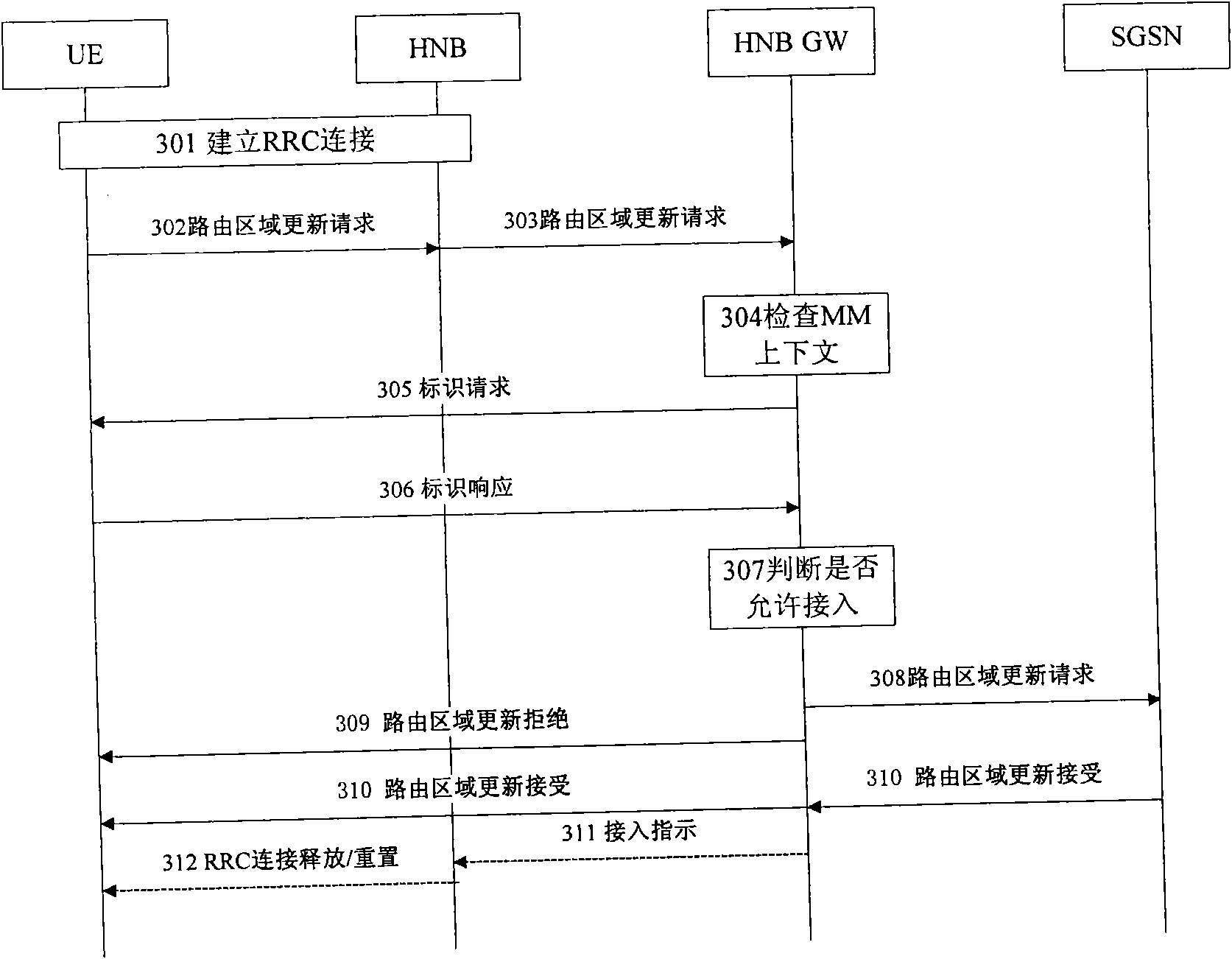
[0025] Embodiments of the present invention are as image 3 shown. The following is a detailed description of the graph. In the following description, detailed technical explanations are omitted for technologies not related to the present invention.
[0026] Step 301: UE establishes RRC connection with 3G HNB. From the perspective of the UE, the UE does not distinguish between the macro base station and the home base station. If the UE is in idle mode, when the user finds that the RAI of the current cell is inconsistent with the RAI saved by the UE, the user needs to initiate a routing update process. Or when the user turns on the UE, the user needs to initiate an Attach process; or when the routing update clock reaches the updating time, the UE needs to initiate a per...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More