File transparent encryption method for adding end-of-file
A file encryption and transparent encryption technology, which is applied in the direction of instruments, electrical digital data processing, digital data protection, etc., can solve problems such as incompatible software
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0020] The composition and structure of the software and hardware system of the file transparent encryption method that adds the file tail is as follows:
[0021] PC, transparent encrypted file filter driver with file ending, WINDOWS system, driver configuration tool.
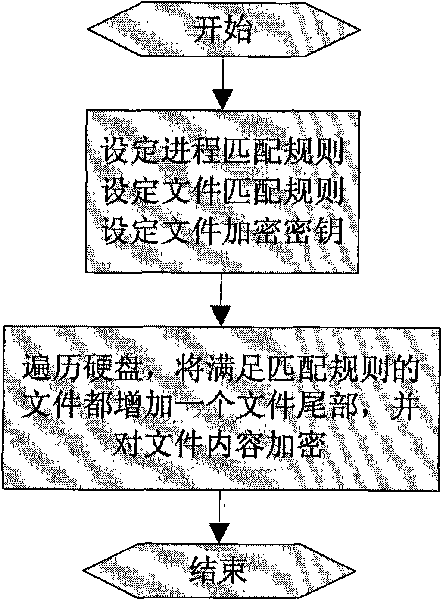
[0022] Step 1: Install the driver to the WINDOW system and start the driver
[0023] Step 2: Use the driver configuration tool to edit the rules for encrypted files. The specific content is as follows:
[0024] 1) What process: Use the name or fingerprint of the process to identify the process;
[0025] 2) What file: Use the file extension to identify the file;
[0026] 3) when to encrypt;
[0027] 4) Encrypt or decrypt when opening the file;
[0028] 5) Whether to encrypt when creating a new file;
[0029] 6) Whether to encrypt when overwriting files;
[0030] Step 3: Use the driver configuration tool to deliver the rules to the driver.
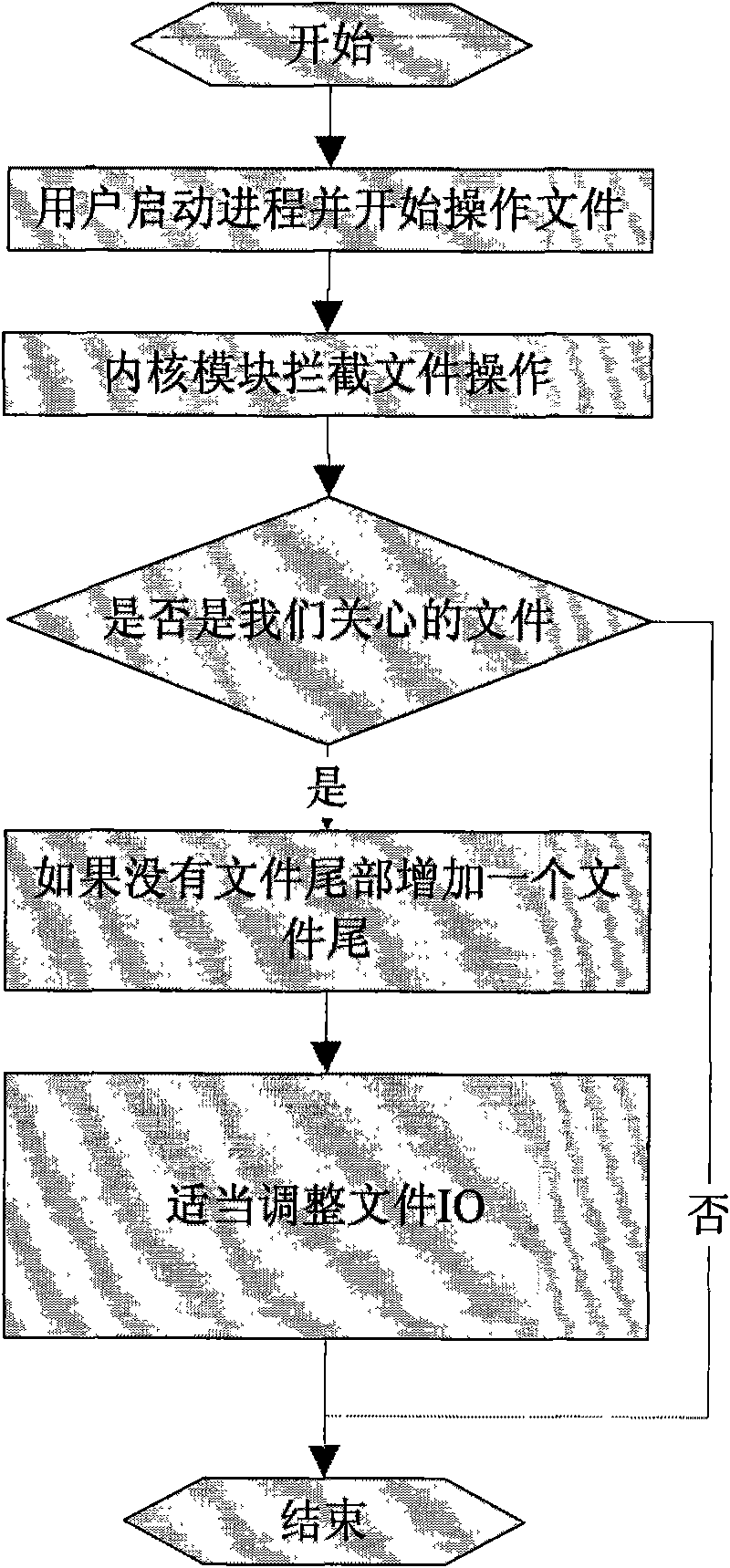
[0031] Step 4: The user uses his own software normally, the driv...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com