Data protecting device and data protecting method
A data protection and data technology, applied in the field of encryption and decryption, can solve problems such as inability to effectively guarantee data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
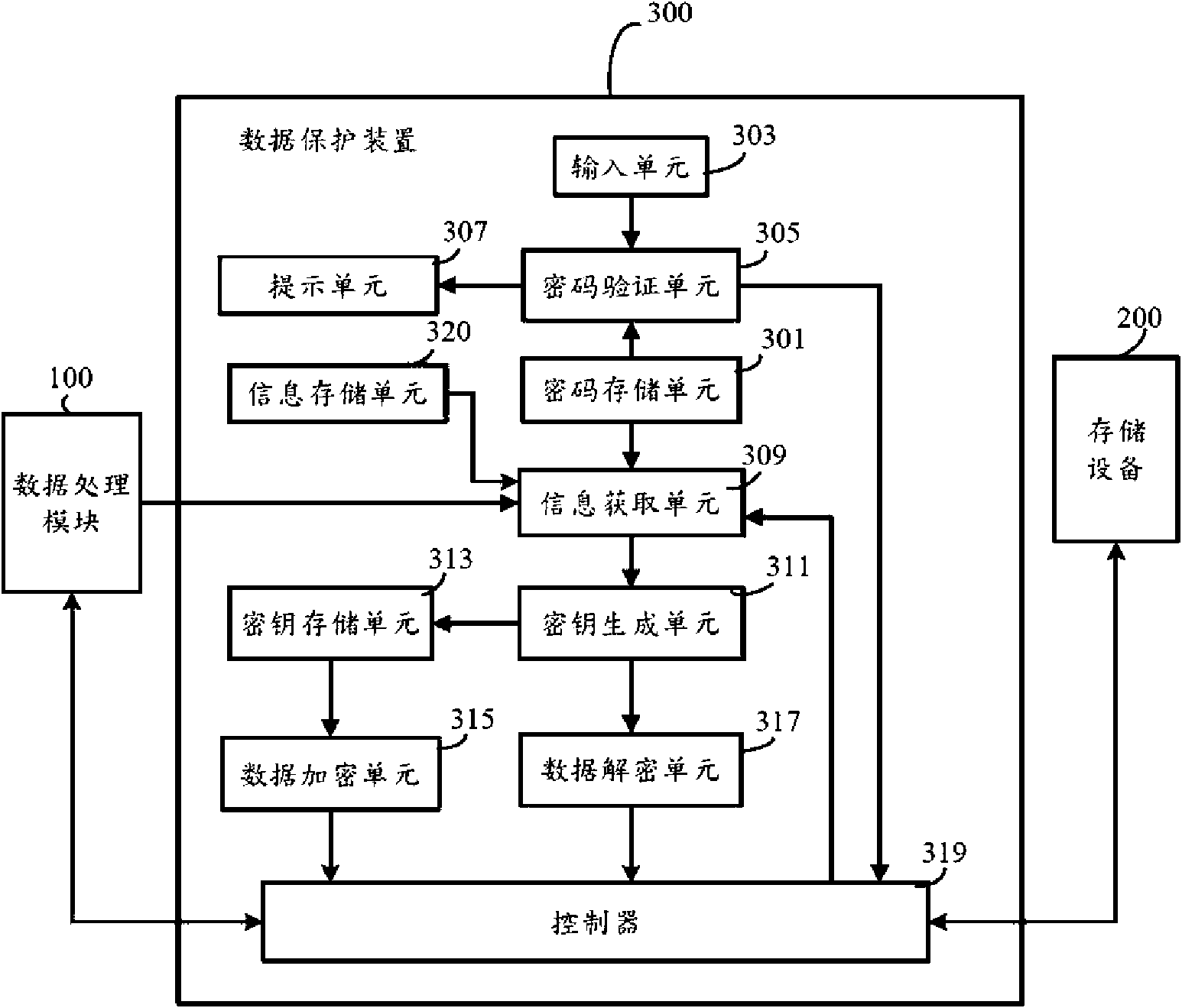
[0017] Please see figure 1 , the computer system includes a data processing module 100 , a storage device 200 and a data protection device 300 . Wherein, the storage device 200 may be a hard disk, a U disk, or the like. The data processing module 100 includes a motherboard, a CPU, and a B10S (basic input / output system), and is used for reading / writing data in the storage device 200 through the data protection device 300 . The data protection device 300 is a chip arranged on the motherboard, which has independent instructions and can be used as an independent user operating system for encrypting and decrypting data entering and leaving the storage device 200 . In other implementation manners, the data protection apparatus 300 may also be disposed in the storage device 200 . The data protection device 300 includes a password storage unit 301, an information acquisition unit 309, a key generation unit 311, a key storage unit 313, an input unit 303, a password verification unit ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More