Method for realizing information security of intelligent terminal and intelligent terminal
A smart terminal and information security technology, applied in the field of communication, can solve the problems of easy cracking of information security software, information leakage, etc., and achieve good concealment and effectiveness, and the effect of protecting information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
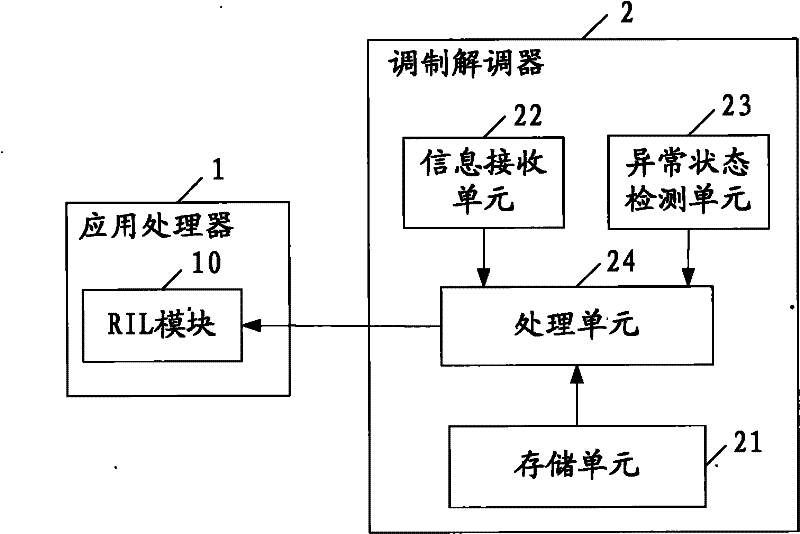
[0030] Embodiments of the present invention provide a method for realizing information security of an intelligent terminal and an intelligent terminal, which are applied to an intelligent terminal adopting an AP+MODEM framework, and the security configuration information is saved on the MODEM, which can effectively protect the information security of the intelligent terminal, and Concealment and effectiveness.
[0031] Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
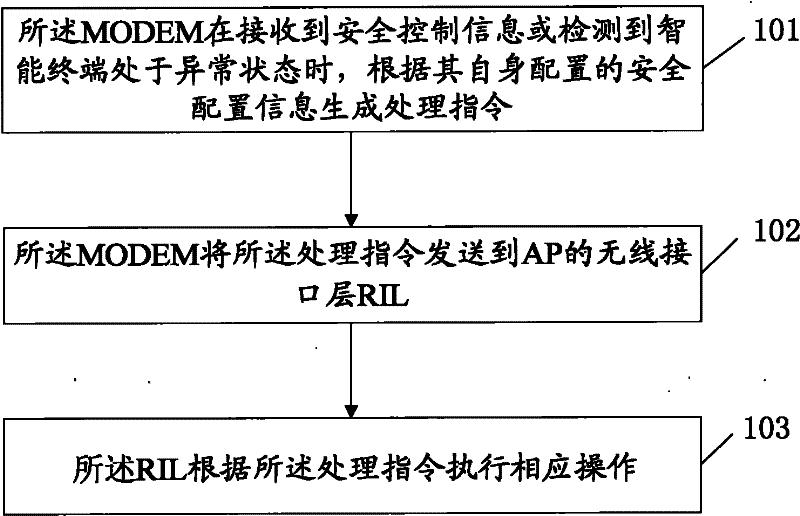
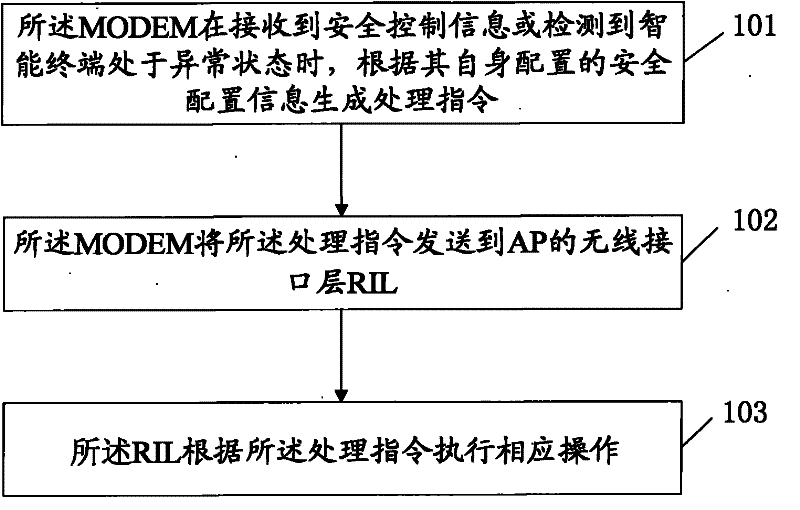
[0032] see figure 1 , is a flow chart of a method for realizing information security of an intelligent terminal in an embodiment of the present invention. The method is applied to an intelligent terminal including an application processor AP and a modem MODEM, that is, an intelligent terminal with an AP+MODEM framework, and includes the following steps :
[0033] Step 101: When the MODEM receives security control information or detects that t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More