A virtual disk integrity protection system and method based on a trusted cryptographic module
A technology of integrity protection and virtual disk, which is applied in the field of information security and can solve problems such as user file integrity verification problems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
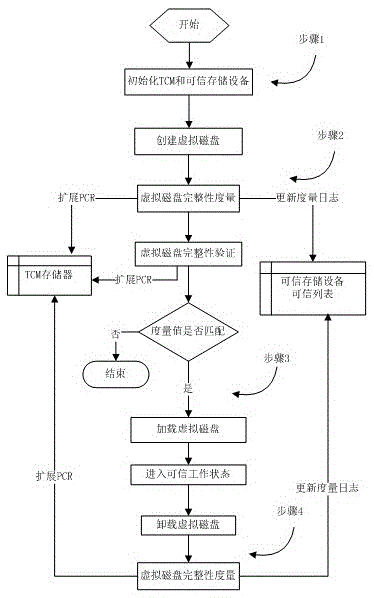
[0027] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
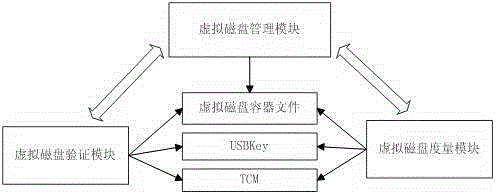
[0028] The embodiment of the present invention is realized by the written software system and the connected hardware equipment, figure 1 The system module structure diagram of the present embodiment is given, such as figure 1 As shown, the software system includes a virtual disk management module, a virtual disk measurement module and a virtual disk verification module, and the hardware device includes a trusted password module (TCM) and a trusted storage device (USBKey).
[0029] Such as figure 1 The shown virtual disk management module is a control module that manages the life cycle of virtual disks. It formats a virtual disk container file with a bootsector file header structure through the formatting method, and loads the virtual disk container file through the virtual disk driver as a virtual disk that the system can recognize. . Such a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More