Method and device for compatible management of encryption algorithm
An encryption algorithm and ciphertext technology, applied in secure communication devices, digital transmission systems, electrical components, etc., can solve problems such as incompatibility and affecting the normal use of electronic wallets, and achieve the effect of reducing costs and ensuring work performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
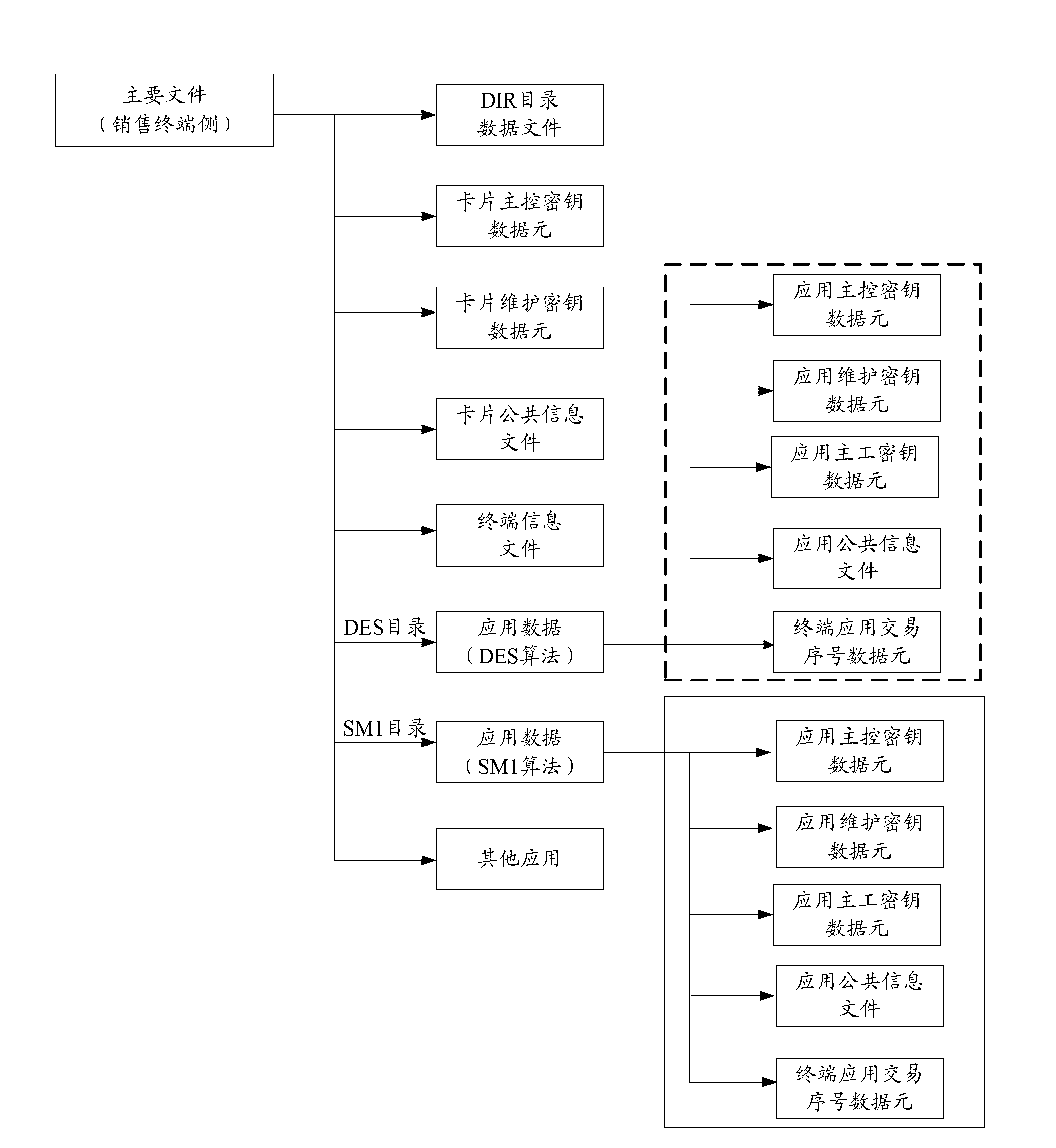
[0031] In order to realize the application compatibility of multiple encryption algorithms, there are several ways to choose from:
[0032] 1. Set the DES algorithm and the newly defined national standard encryption algorithm in the electronic account carrier at the same time, and the sales terminal that can support the use of the two encryption algorithms can choose to use it for the electronic account carrier through different AIDs (Application Identifer, application identifier). which algorithm.
[0033] 2. The sales terminal that can support the use of two encryption algorithms sends an algorithm selection instruction to the electronic account carrier, and the corresponding encryption algorithm can only be used if the instruction verification is successful.
[0034] 3. A sales terminal that can support two encryption algorithms to send instructions to an electronic account, which encryption algorithm to use for the instruction, and which encryption algorithm to use by defa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More