Trusted network access method and system for mobile terminal
A mobile terminal and network access technology, applied in wireless communication, electrical components, security devices, etc., can solve problems such as stealing and destroying companies, and achieve the effect of guaranteeing network resources
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
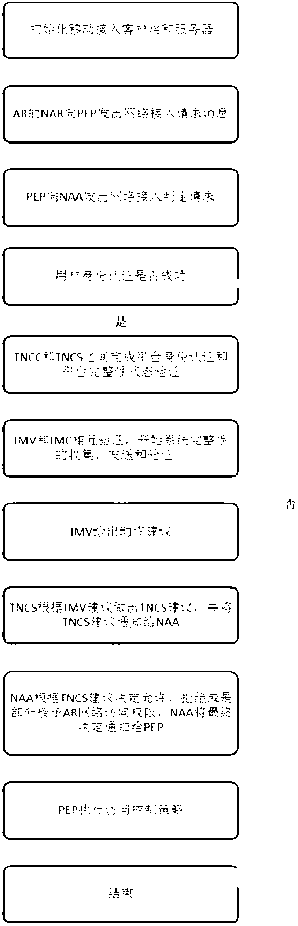
[0029] The mobile terminal trusted network access technology of the present invention will be described in detail below in conjunction with the accompanying drawings.
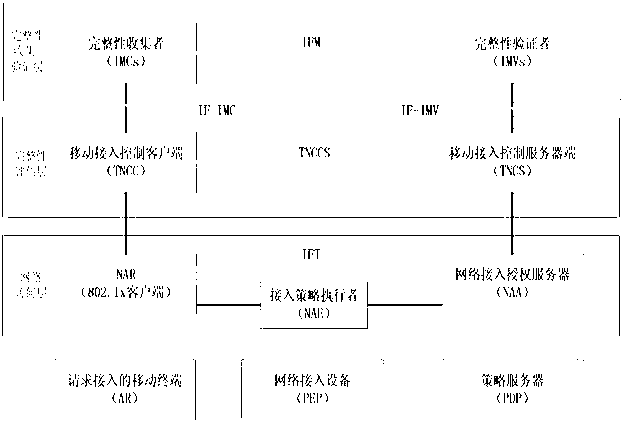
[0030] like figure 1 As shown, the mobile terminal trusted network access system includes a mobile terminal requesting access, an access control server and an access policy server.
[0031] 1. The mobile terminal (AR, Access Requestor) that issues the access request is connected to the PEP through wireless. It is usually installed with a common network access terminal to support general network access methods, such as 802.1x, and a complete AR is deployed on the AR. Integrity Measurement Collector Interface (IMC, Integrity Measurement Collector Interface), Trusted Network Connect Client (TNCC, Trusted Network Connect Client) and Network Access Requestor (NAR, Network Access Requestor).
[0032]2. Network access devices (PEP, Policy Enforcement Point), such as APs, VPN gateways, etc., need to support commonly u...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More