Mobile terminal and data protection method thereof
A mobile terminal and data protection technology, applied in digital data protection, encryption device with shift register/memory, telephone communication, etc., can solve the problem of low data security, to ensure security, reliable protection, prevent The effect of read and write operations
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
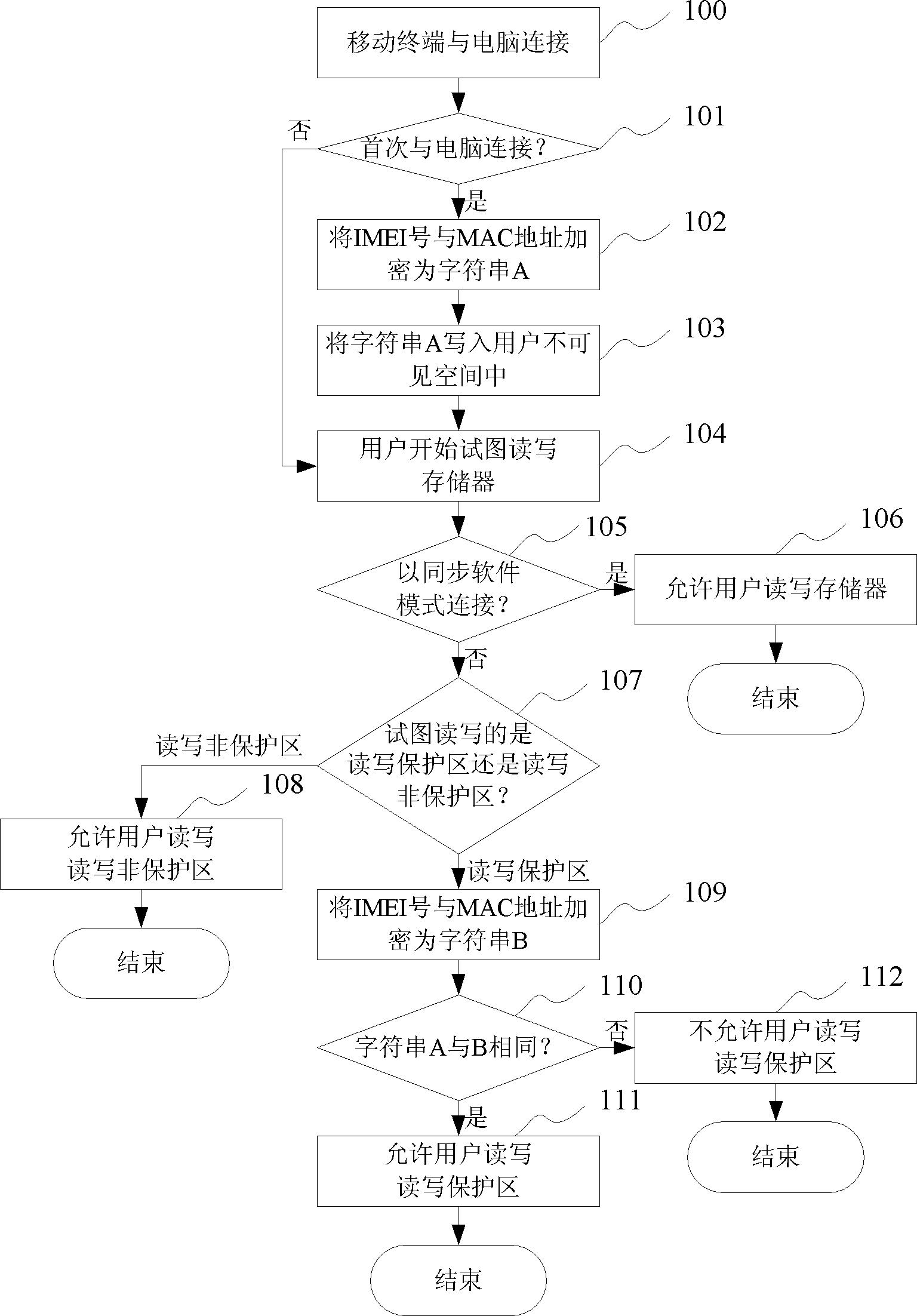
[0037] The preferred embodiments of the present invention are given below in conjunction with the accompanying drawings to describe the technical solution of the present invention in detail.
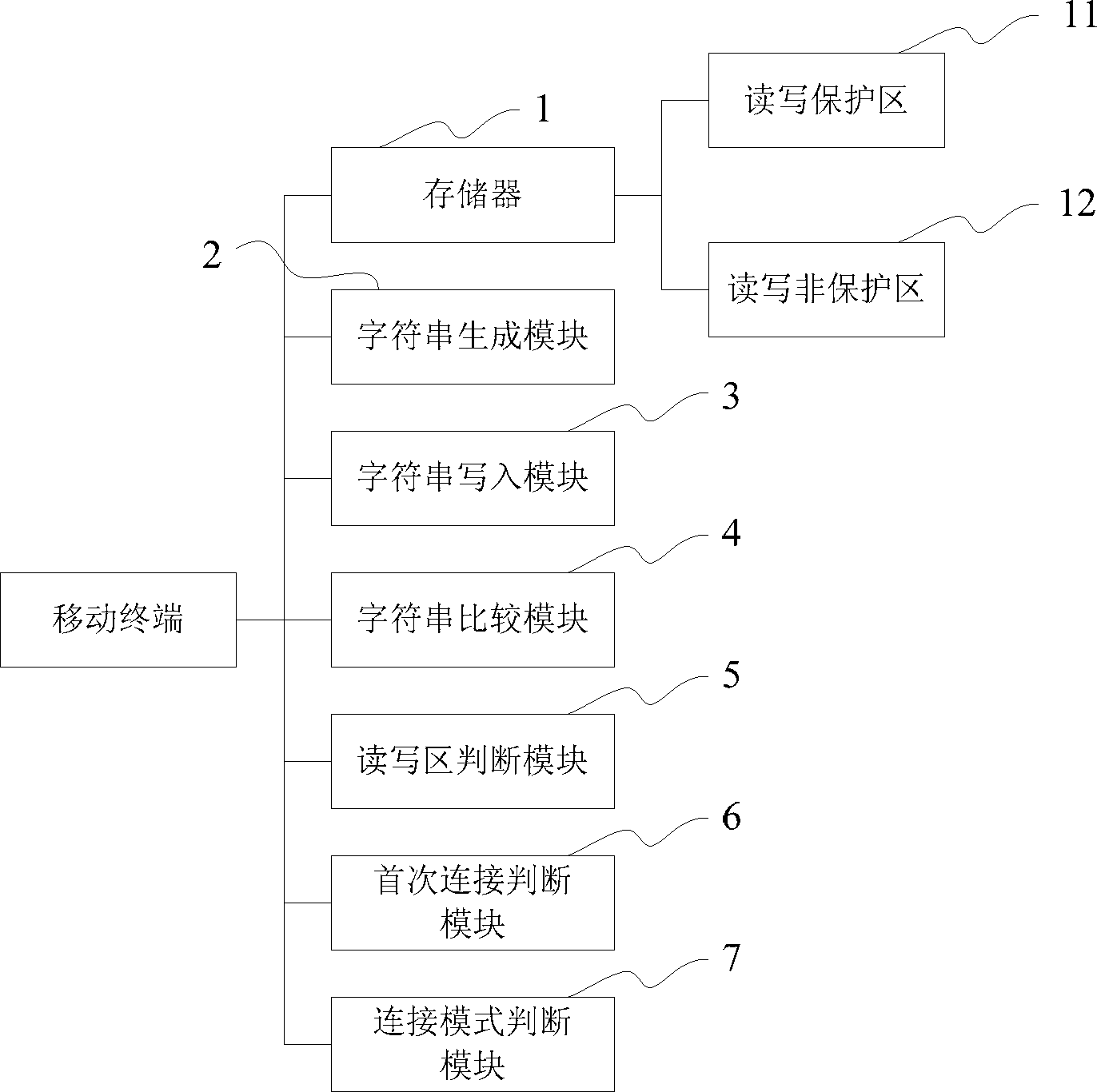
[0038] refer to figure 1 As shown, in the mobile terminal of the present invention, its memory 1 includes a read-write protected area 11 and a read-write unprotected area 12 . In addition, the mobile terminal also includes: a character string generation module 2 , a character string writing module 3 , a character string comparison module 4 , a read-write area judging module 5 and a first-time connection judging module 6 .
[0039] The character string generating module 2 is used to generate a character string by using an encryption algorithm, such as MD5, to generate the IMEI number of the mobile terminal and the MAC address of the computer connected to the mobile terminal.
[0040] The character string writing module 3 is used for writing the character string generated by the character...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More