Authentication method, authentication device and authentication system
An authentication device and authentication method technology, applied in the fields of authentication methods, devices and systems, can solve the problem of not being able to exchange data between users in real time, quickly and efficiently, and achieve the effect of improving security and exchanging data efficiently
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] The principles and features of the present invention are described below in conjunction with the accompanying drawings, and the examples given are only used to explain the present invention, and are not intended to limit the scope of the present invention.
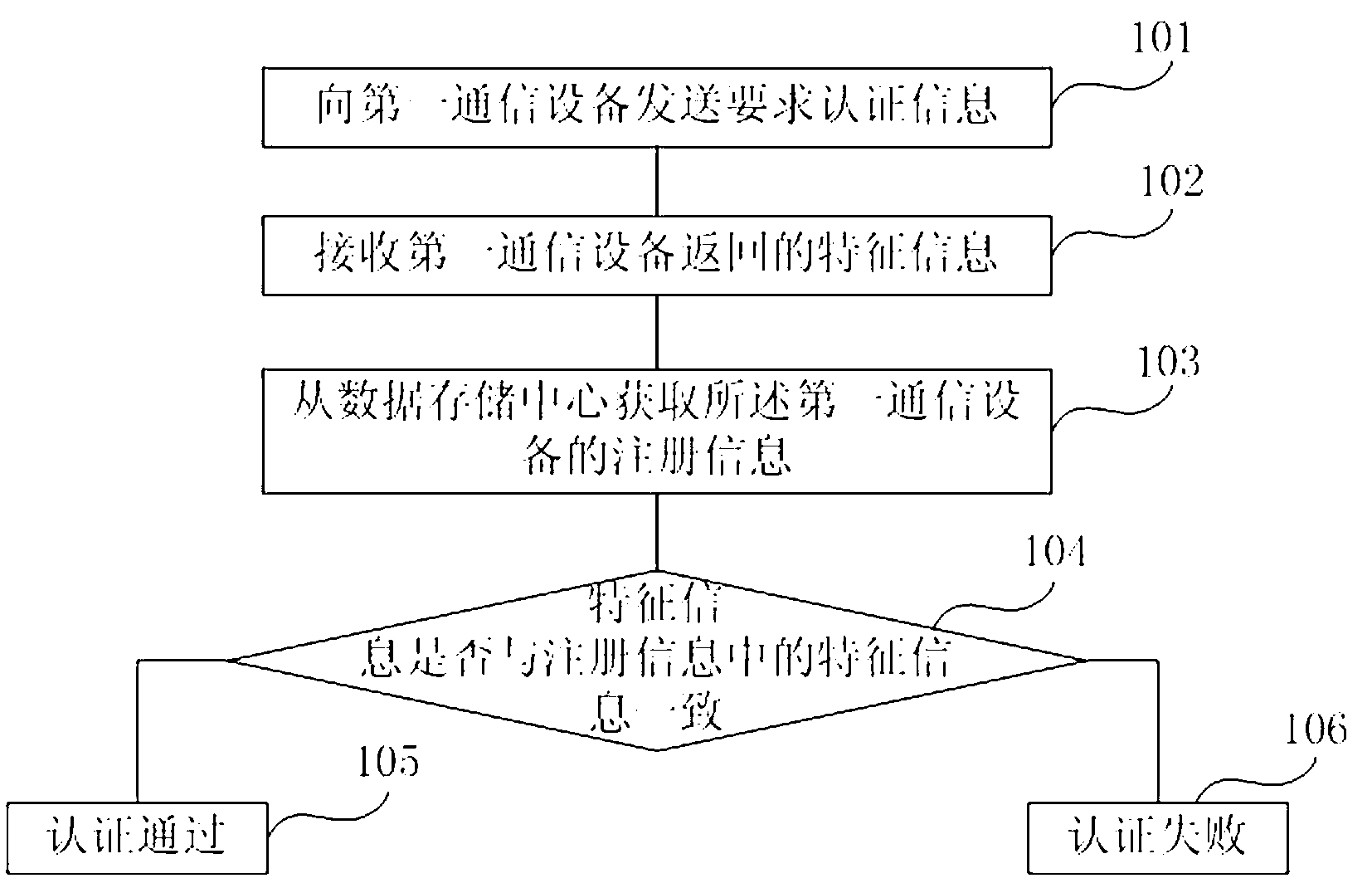
[0046] figure 1 It is a flow chart of the authentication method in the embodiment of the present invention. Such as figure 1 As shown, in this embodiment, the authentication method includes the following steps:
[0047] The premise of the authentication method in this embodiment is that after the first communication device successfully registers for the first time, the data storage center saves the registration information of the first communication device at the time of the first registration, and the registration information includes the characteristic information of the first communication device . That is to say, before performing the following step 101, the authentication method of the present invention may ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More