A method and system for stealth processing of files
A file processing and file technology, applied in transmission systems, digital transmission systems, electrical components, etc., can solve the problems of illegal reading or modification of data in the reserved area, lack of encryption and division methods, etc., to achieve data security. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
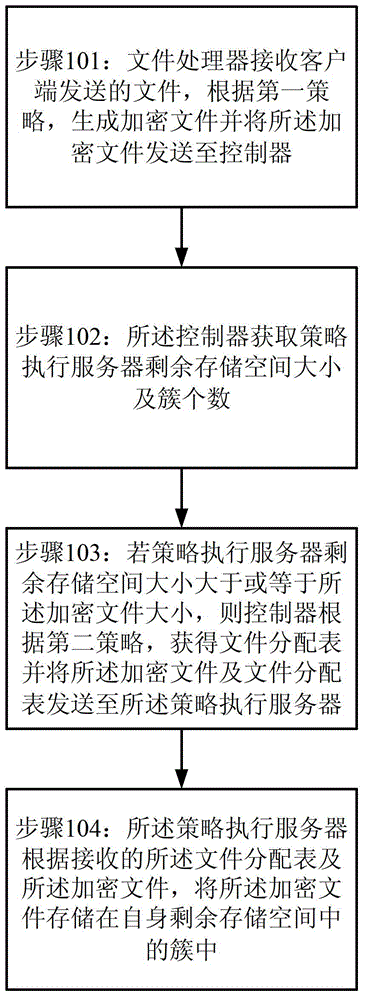
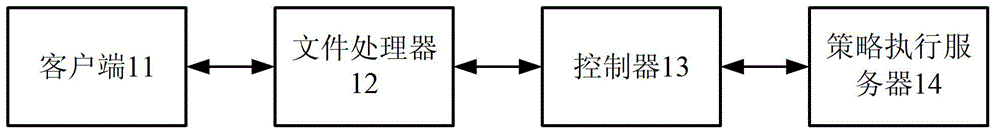
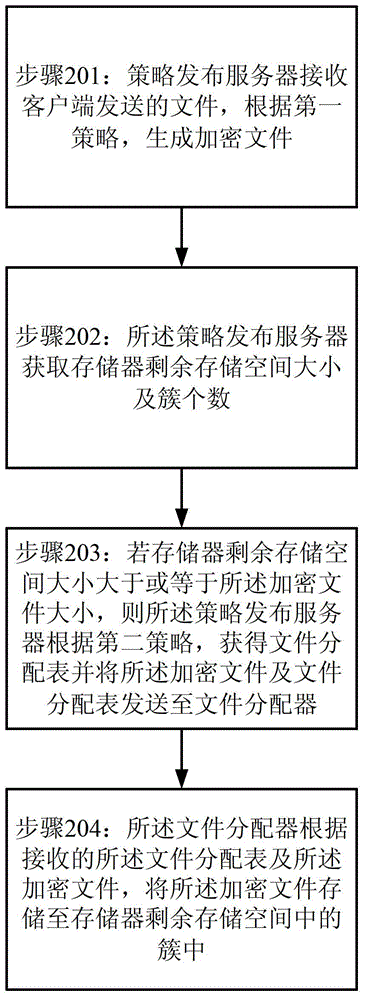
[0024] figure 1 Shown is a flow chart of the method for file concealment processing provided according to the first preferred embodiment of the present invention. Figure 9 Shown is a schematic diagram of a parabola provided according to a preferred embodiment of the present invention. figure 2 Shown is a schematic diagram of the file concealment processing system provided according to the first preferred embodiment of the present invention. Please also refer to figure 1 , figure 2 and Figure 9 . Such as figure 1 As shown, the method for invisible file processing provided by the first preferred embodiment of the present invention includes steps 101-104.
[0025] Step 101: The file processo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More