Malicious code detection and defense method
A malicious code detection and program technology, applied in the field of malicious code detection and defense systems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
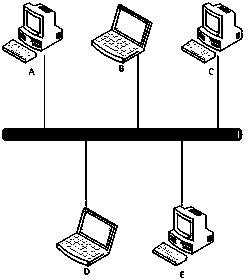
Image
Examples
Embodiment Construction
[0025] The invention provides a system including detection, response and defense.
[0026] (1) Detection
[0027] Detection is a key part of the invention, it is like a camera in a mall. Detection is done by setting watchpoints, which are set in the following aspects:
[0028] 1. Process creation and termination, remote thread creation, memory reading and writing, dynamic link library loading;
[0029] 2. Network port monitoring, data sending and receiving, and protocol interfaces such as HTTP provided by the operating system;
[0030] 3. Addition, deletion, modification of registry entries, and files corresponding to registry entries;
[0031] 4. Deletion and modification of operating system files, creation, copying, moving, and deletion of files in the system directory, installation, copying, moving, and deletion of applications;
[0032] 5. Loading and modification of kernel modules, creation, startup and modification of services, modification of SPI, BHO, SSDT, etc.
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More