Cloud storage data security auditing method allowing group-user identity revocation
A data security and user identity technology, applied in the field of data security, can solve problems such as indistinguishability and loss of cloud users
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] The present invention will be further described below in combination with specific embodiments.
[0043] A cloud storage data security audit method that allows group user identity revocation, specifically as follows:
[0044] 1.1 Meaning of the symbols used in the method
[0045] M represents the shared data stored in the cloud server, which consists of n data blocks m 1 ,…,m n Composition; n represents the total number of blocks of shared data; d represents the total number of users in the group;
[0046] Order G 1 and G 2 Respectively represent the cyclic group of order p, g is G 1 A generator of , w is G 1 A random element in . p is a prime number with a length of 160 bits; q is a prime number much smaller than p with a length of 64 bits;
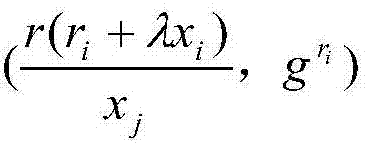
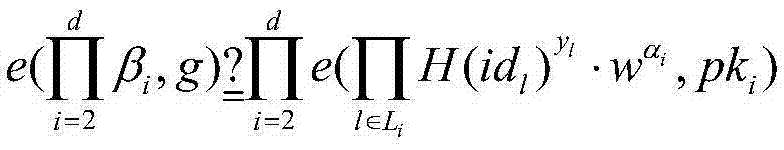
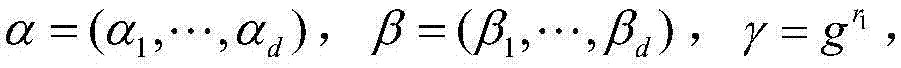
[0047] H represents a one-way hash function, and the definition mapping is H:{0,1} * →G 1 , where G 1 is a cyclic group whose order is a prime number p; H' is a collision-resistant hash function, and the definition mapp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More