A method and system for secure data transmission based on dual hardware
A technology of data security and transmission method, which is applied in the field of data security and its safe transmission, can solve problems such as theft, tampering, hidden dangers of data security, inconvenient use, etc., and achieve the effect of ensuring data security and timeliness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
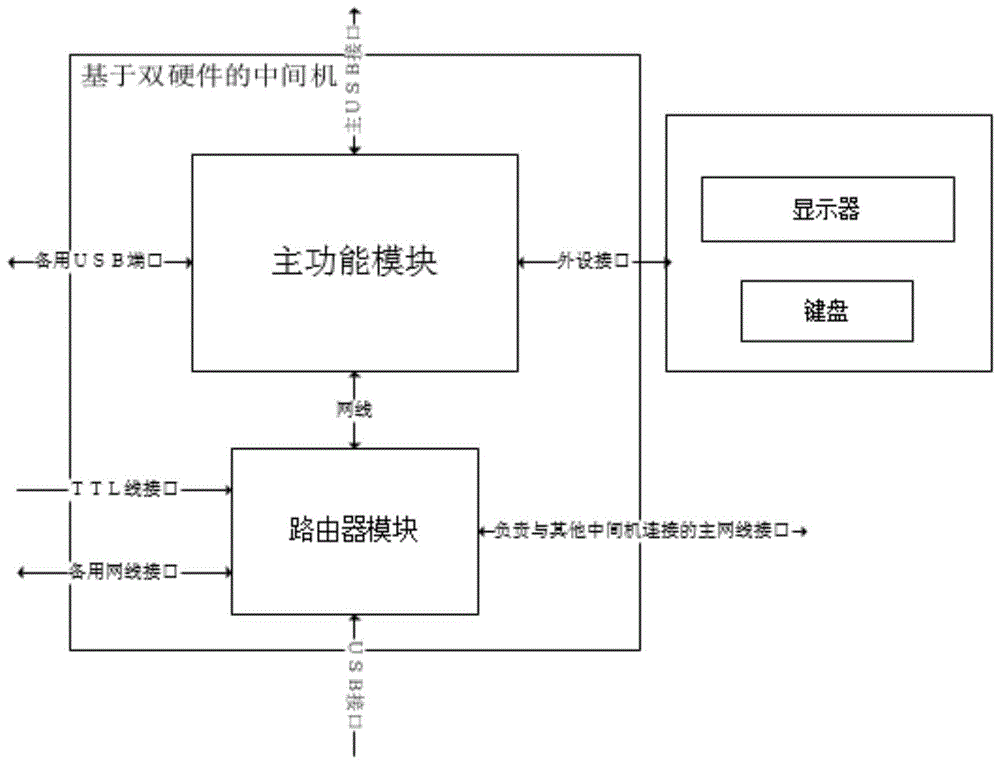
[0058] The present invention will be further described in detail below in conjunction with the embodiments and the accompanying drawings, but the embodiments of the present invention are not limited thereto.
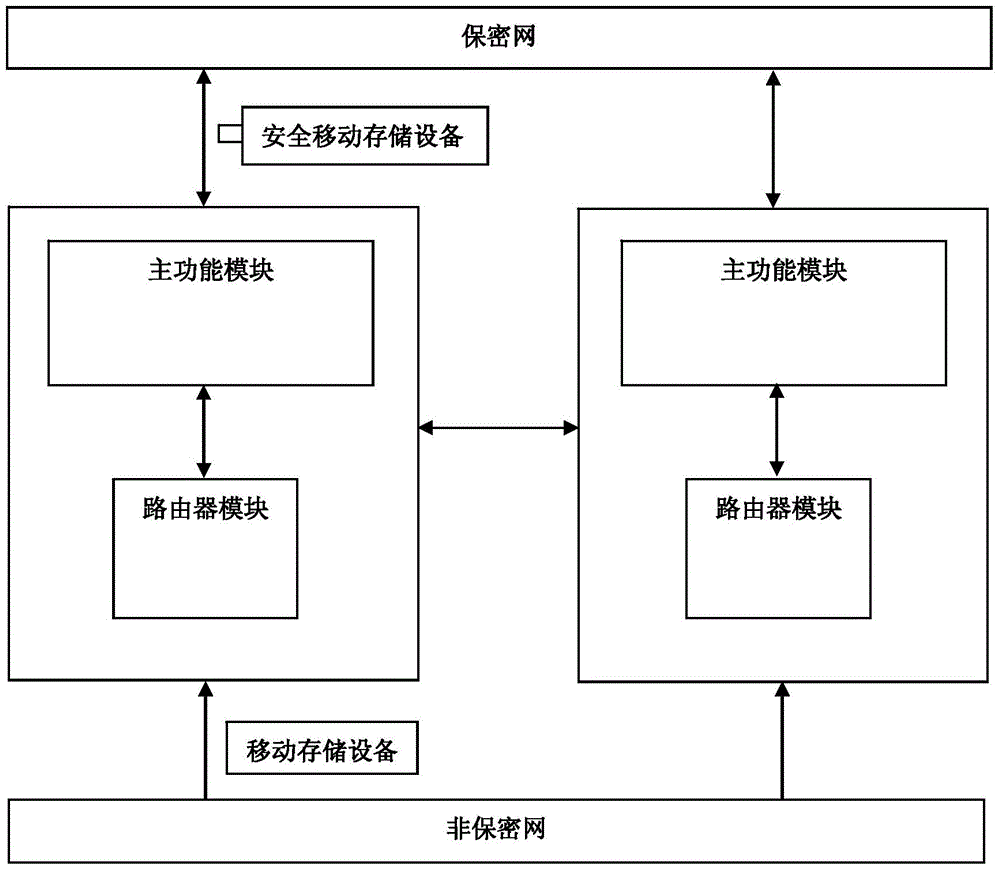
[0059] Please refer to figure 1 , figure 1 It is a flowchart of a data security transmission method based on dual hardware, and the specific implementation process is as follows:
[0060] The user downloads the data from the non-confidential network to the mobile storage device (such as U disk, mobile hard disk, SD card, etc.);
[0061] The user connects the mobile storage device to the middle machine based on dual hardware;
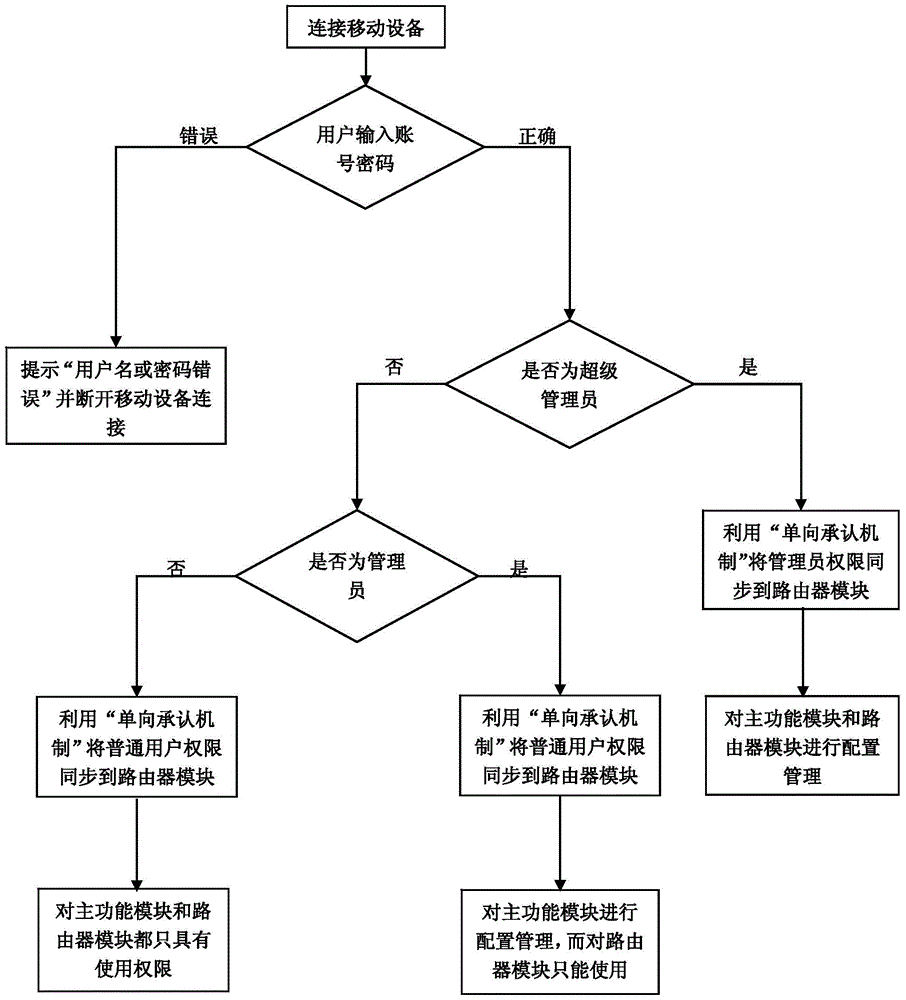
[0062] The middle machine implements access control, and the implementation process can refer to image 3 . The operating system on the main function module prompts the user to input the account password, and then performs authority determination. If it is determined as a super administrator, use the "one-way recognition mechanism" to synchron...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More