Attacking control method for protecting kernel system
A control method and core technology, applied in the fields of platform integrity maintenance, instrumentation, electrical digital data processing, etc., can solve the problems of data lack of identification ability, reduce the security of core system protection, etc., and achieve the effect of ensuring safety and credibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
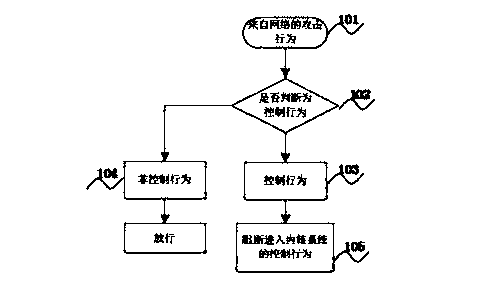
[0017] The embodiment of the present invention provides an attack control method for protecting the kernel system to solve the existing traditional data control technology, which only records or modifies the data entering the honeypot system, but has no ability to identify the data itself. The present invention is mainly used for active, efficient and system-level safety defense of the pre-defense system, server and active trapping system of the network.
[0018] In order to make the object, technical solution, and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the accompanying drawings and examples.
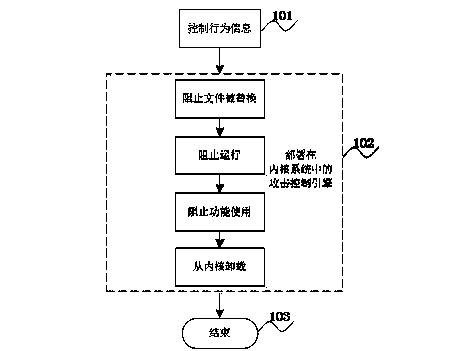
[0019] The invention prevents the kernel file from being replaced by the attack behavior through the control attack engine deployed in the kernel system, prevents the attack behavior from running, so that the use of the attack function is lost, and finally deletes it from the kernel system. Some of ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More