Information interception method, device and system
A technology for information content and sending information, applied in the information field, can solve the problem of not being able to intercept spam messages in a timely and effective manner, and achieve the effect of simple and timely interception
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only a part of the embodiments of the present invention, rather than all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative work shall fall within the protection scope of the present invention.
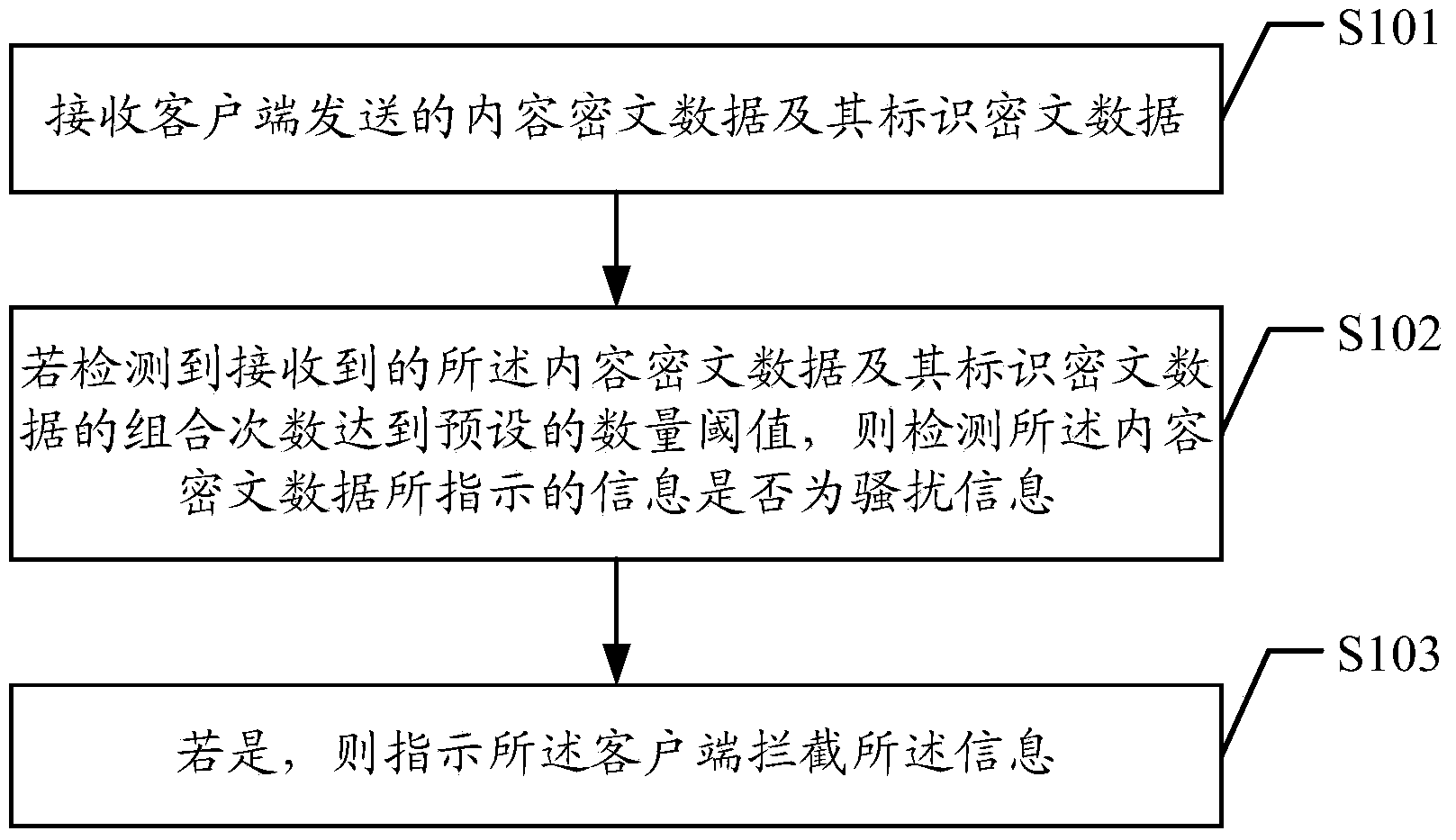
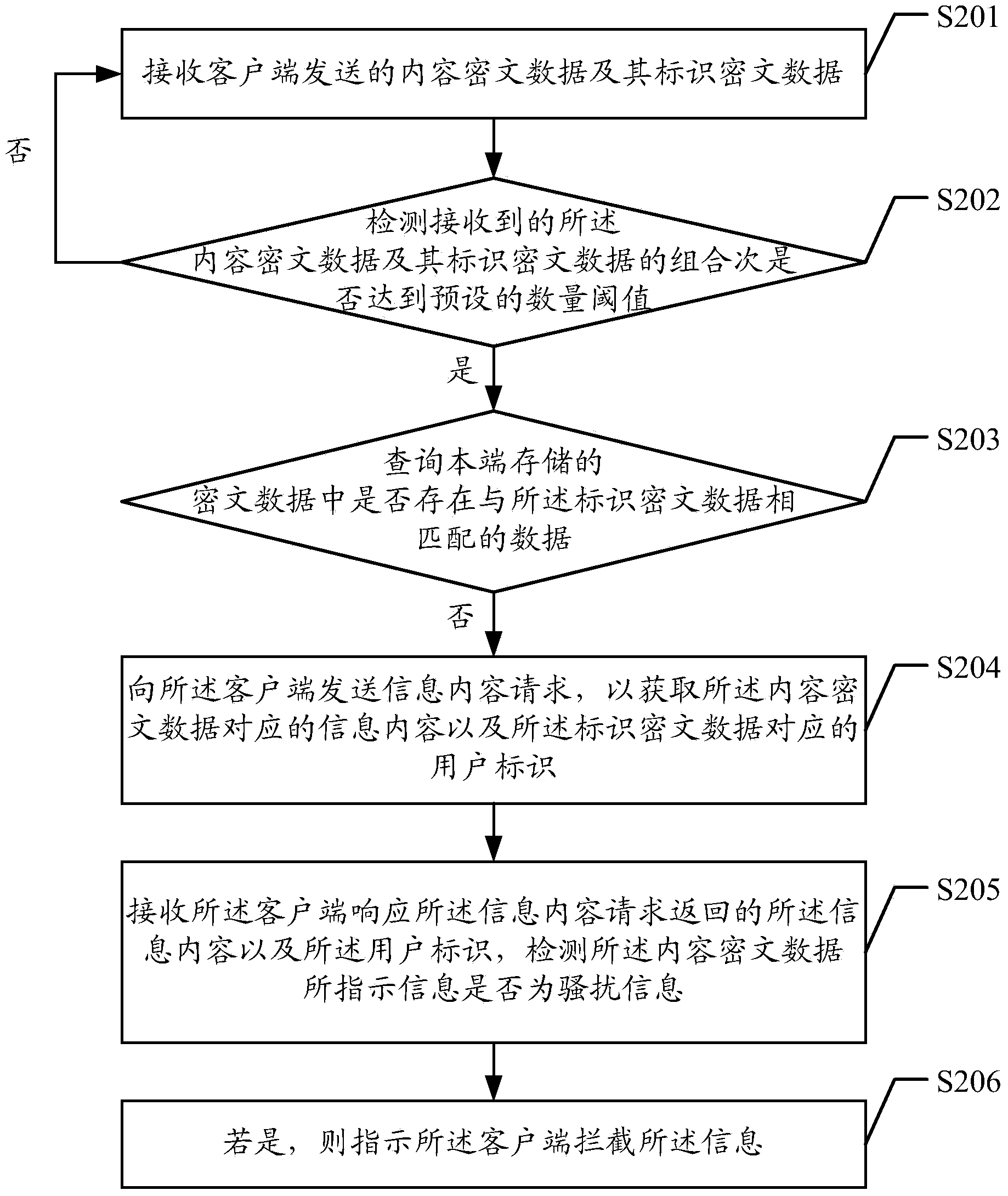
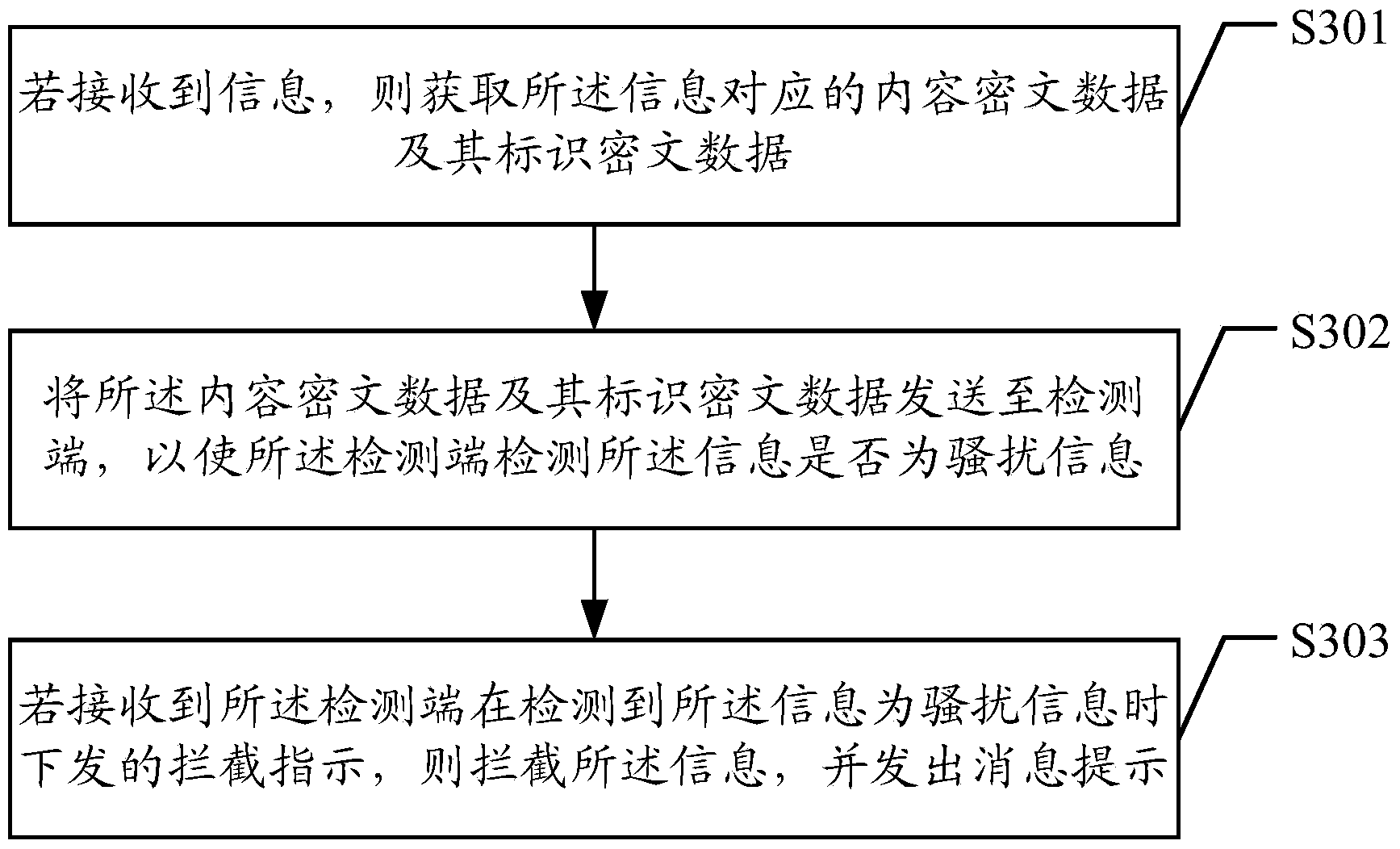
[0039] See figure 1 , Is a schematic flow chart of an information interception method provided by an embodiment of the present invention. The method in the embodiment of the present invention can be specifically applied to a detection terminal that can be used to detect and store information data such as a cloud server. Specifically, the Methods include:
[0040] S101: Receive the content ciphertext data and its identification ciphertext d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More