Method and system for digital certificate signature
A digital certificate and digital signature technology, applied in the direction of user identity/authority verification, etc., can solve problems such as inability to defend against theft, no good connection between USBKey and mobile devices, and difficulties in user installation and use
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
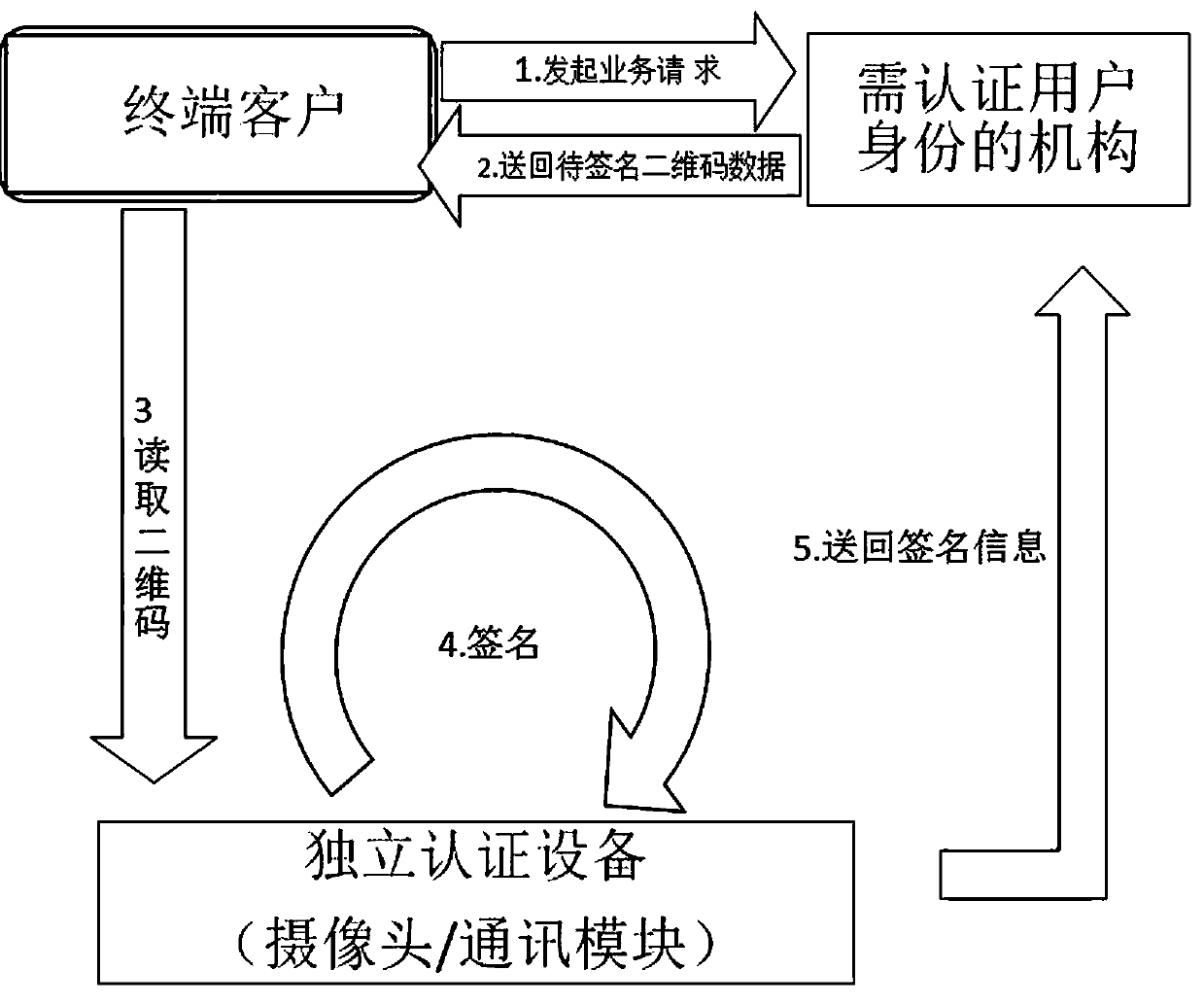
[0097] The present invention provides a digital certificate signature method. The system implementing the method includes an authentication institution, an institution that needs to authenticate the identity of the user, and a client. The method includes the following steps:
[0098] A1. The customer sends a business request to the organization that needs to authenticate the user's identity;
[0099] A2. The organization that needs to authenticate the user's identity sends the data to be signed to the customer;
[0100] A3. The customer uses an independent digital signature device to receive the data to be signed;
[0101] A4. The client uses an independent digital signature device to sign;
[0102] A5. The customer uses an independent digital signature device to send the signed data back to the organization that needs to authenticate the user's identity;
[0103] A6. The organization that needs to authenticate the user's identity receives the signed data;
[0104] A7. The ...
Embodiment 2
[0111] The present invention provides a digital certificate signature method. The system implementing the method includes an authentication institution, an institution that needs to authenticate the identity of the user, and a client. The method includes the following steps:
[0112] A1. The customer sends a business request to the organization that needs to authenticate the user's identity;
[0113] A2. The organization that needs to authenticate the user's identity sends the data to be signed to the customer;
[0114] A3. The customer uses an independent digital signature device to receive the data to be signed;
[0115] A4. The client uses an independent digital signature device to sign;
[0116] A5. The customer uses an independent digital signature device to send the signed data back to the organization that needs to authenticate the user's identity;
[0117] A6. The organization that needs to authenticate the user's identity receives the signed data;
[0118] A7. The ...
Embodiment 3
[0125] The present invention provides a digital certificate signature method. The system implementing the method includes an authentication institution, an institution that needs to authenticate the identity of the user, and a client. The method includes the following steps:
[0126] A1. The customer sends a business request to the organization that needs to authenticate the user's identity;
[0127] A2. The organization that needs to authenticate the user's identity sends the data to be signed to the customer;
[0128] A3. The customer uses an independent digital signature device to receive the data to be signed;
[0129] A4. The client uses an independent digital signature device to sign;
[0130] A5. The customer uses an independent digital signature device to send the signed data back to the organization that needs to authenticate the user's identity;
[0131] A6. The organization that needs to authenticate the user's identity receives the signed data;
[0132] A7. The ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More