Security vulnerability management method and system and device
A vulnerability management and security technology, applied in the computer field, can solve problems such as low efficiency and cumbersome work, and achieve the effect of improving work efficiency and unified management
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] In order to make the object, technical solution and advantages of the present invention clearer, the implementation manner of the present invention will be further described in detail below in conjunction with the accompanying drawings.
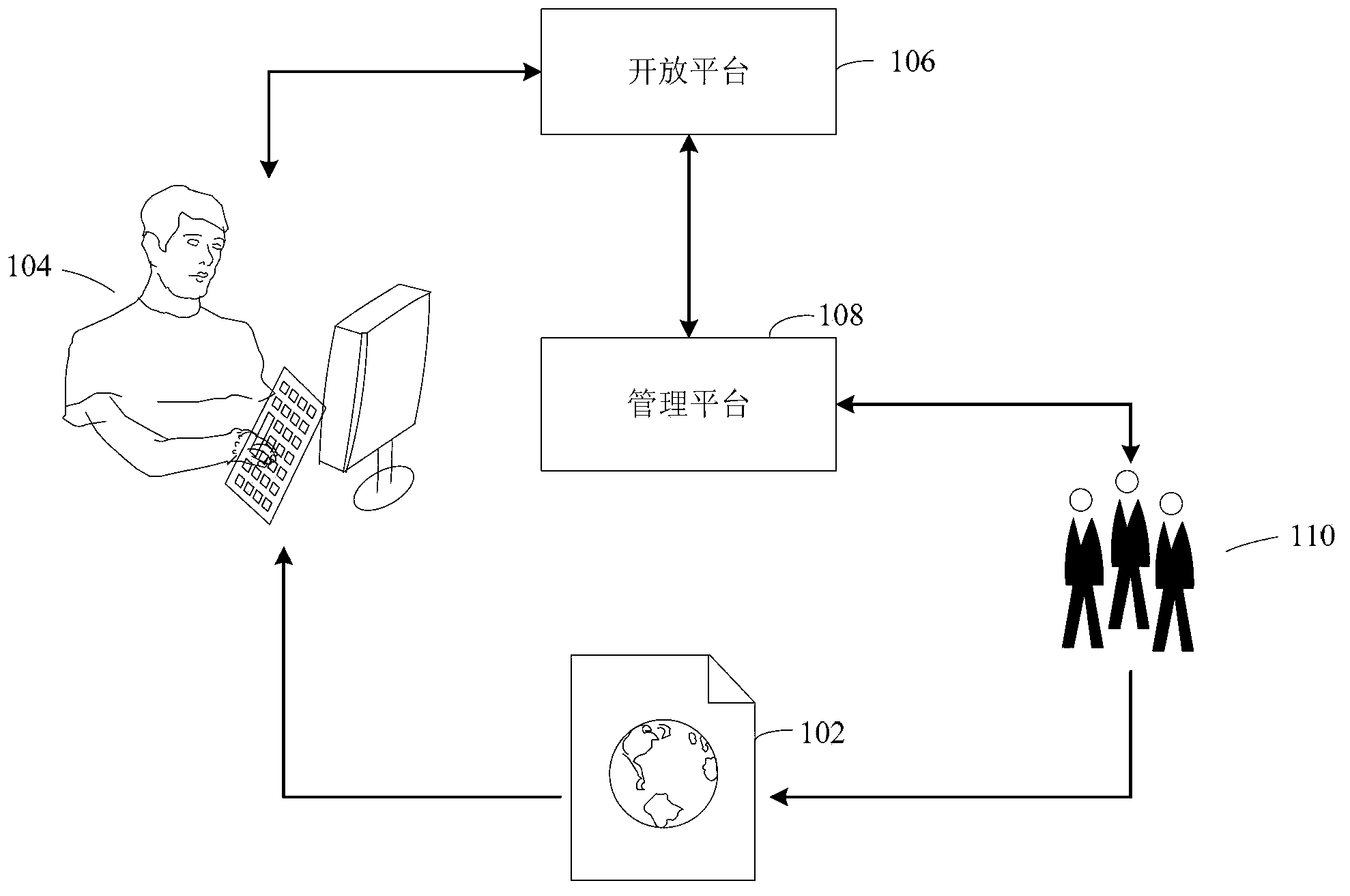
[0036] See figure 1 As shown in , it shows a schematic diagram of the implementation environment involved in the security vulnerability management method provided by some embodiments of the present invention. The implementation environment may include: Internet company products 102 , security researchers 104 , Internet company open platforms 106 , Internet company management platforms 108 and Internet company repair personnel 110 .
[0037] Products 102 of an Internet company are usually all or part of the products released by the Internet company, such as forums, chat applications, antivirus programs, browsers, and input methods.
[0038] The security researchers 104 can usually be outsiders of the Internet company, and these securit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More