Cross-site scripting attack vulnerability detection method and device based on document object model
A technology of document object model and cross-site scripting attack, which is applied in the network field, can solve the problems of reducing vulnerability discovery ability and detection efficiency, and spending a lot of time, and achieve the effect of improving vulnerability discovery ability and detection efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] In order to make the object, technical solution and advantages of the present invention clearer, the implementation manner of the present invention will be further described in detail below in conjunction with the accompanying drawings.
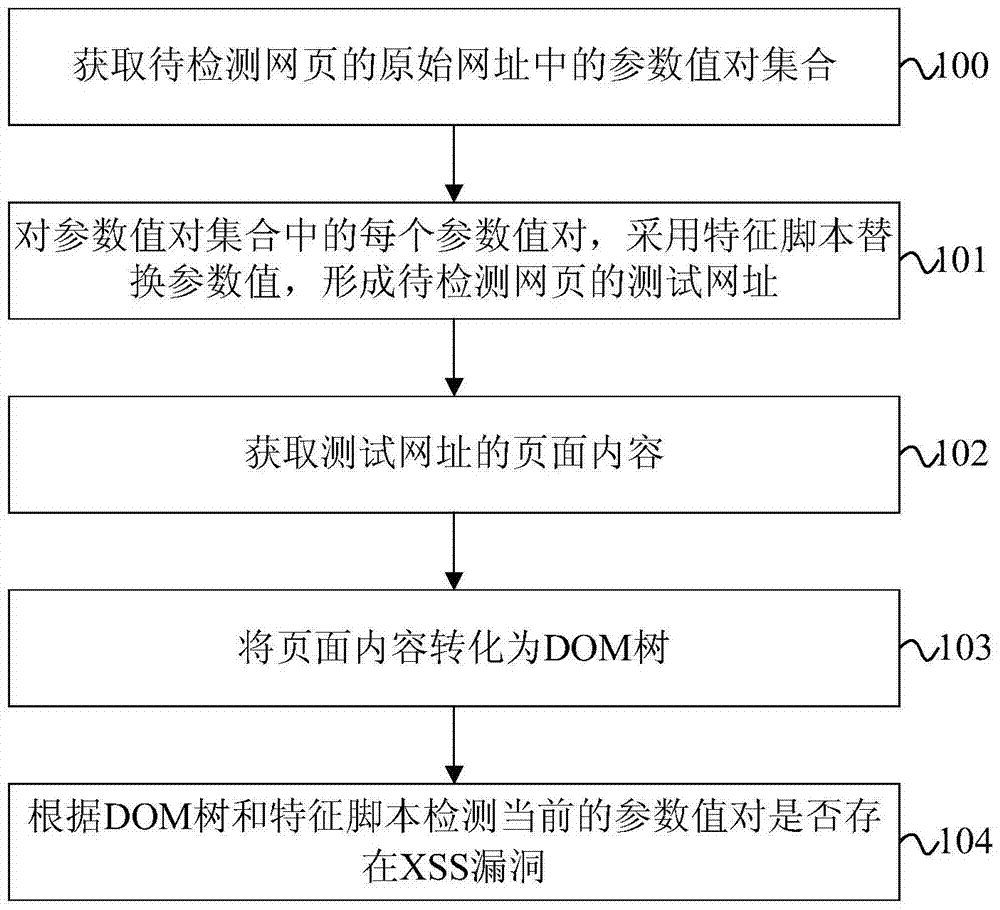
[0029] figure 1 It is a flowchart of a DOM XSS vulnerability detection method provided by an embodiment of the present invention. That is, the document object model (Document Object Model, DOM)-based cross-site scripting (Cross Site Script, XSS) vulnerability detection method of this embodiment is directly referred to as the DOM XSS vulnerability detection method for short. Such as figure 1 As shown, the DOM XSS vulnerability detection method of the present embodiment may specifically include the following steps:
[0030] 100. Obtain a set of parameter value pairs in the original URL of the webpage to be detected;
[0031] The set of parameter value pairs in this embodiment includes at least one parameter value pair.
[0032] In th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More