Safe content access method
An access method and content security technology, applied in the field of content security access, can solve the problems of reducing data management, high cost of key maintenance, and achieve the effects of improving key security, reducing return frequency, and reducing overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
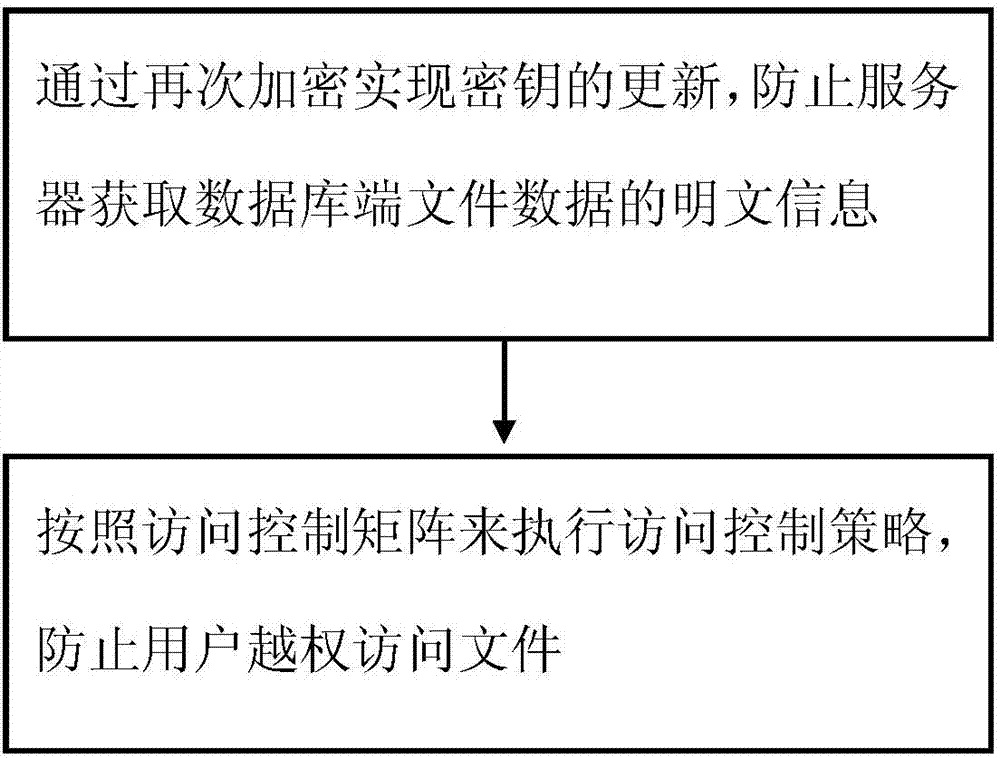
[0012] The following is attached to illustrate the principle of the present invention Figure one A detailed description of one or more embodiments of the present invention is provided together. The present invention is described in conjunction with such an embodiment, but the present invention is not limited to any embodiment. The scope of the present invention is limited only by the claims, and the present invention covers many alternatives, modifications and equivalents. In the following description, many specific details are set forth in order to provide a thorough understanding of the present invention. These details are provided for the purpose of example, and the present invention can be implemented according to the claims without some or all of these specific details.
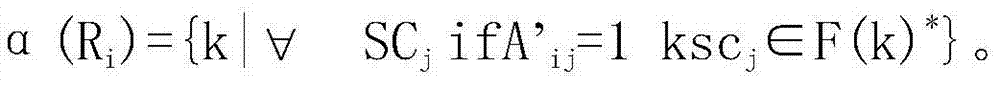
[0013] An aspect of the present invention provides a method for securely accessing content. figure 1 It is a flowchart of a method for securely accessing content according to an embodiment of the present ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More