Resource play method and system for intelligent terminal
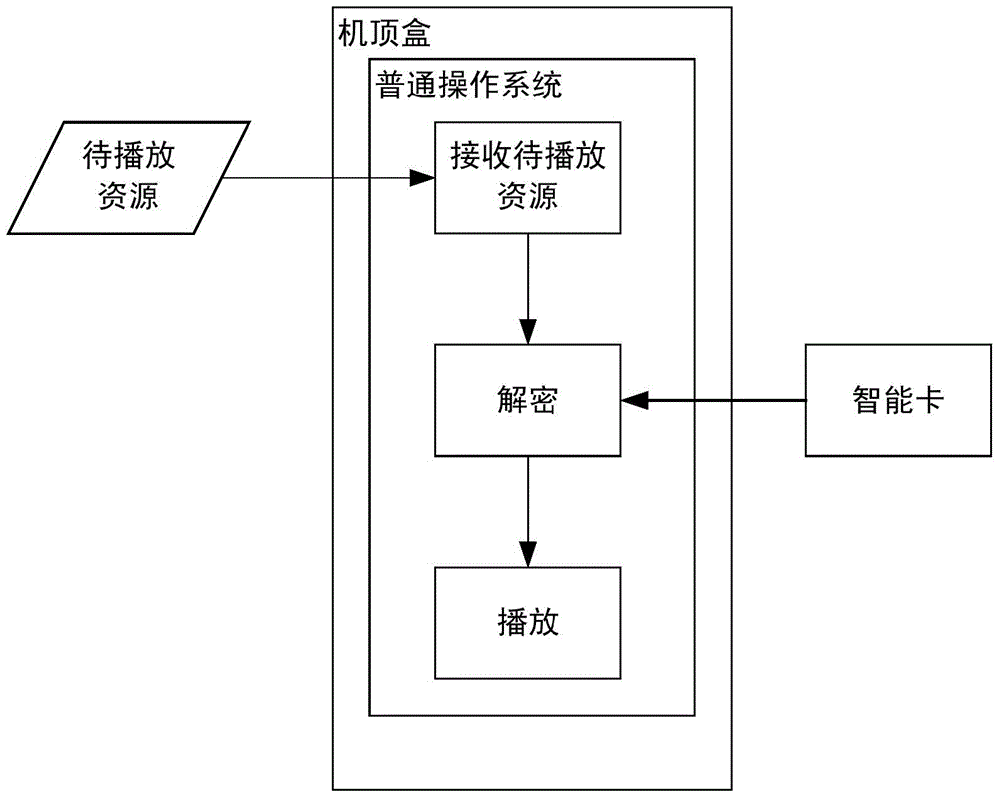
A technology of intelligent terminal and playback method, which is applied in the information field, can solve problems such as waste, easy to be cracked by physics, difficult to ensure decryption and playback security, and achieve the effect of ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
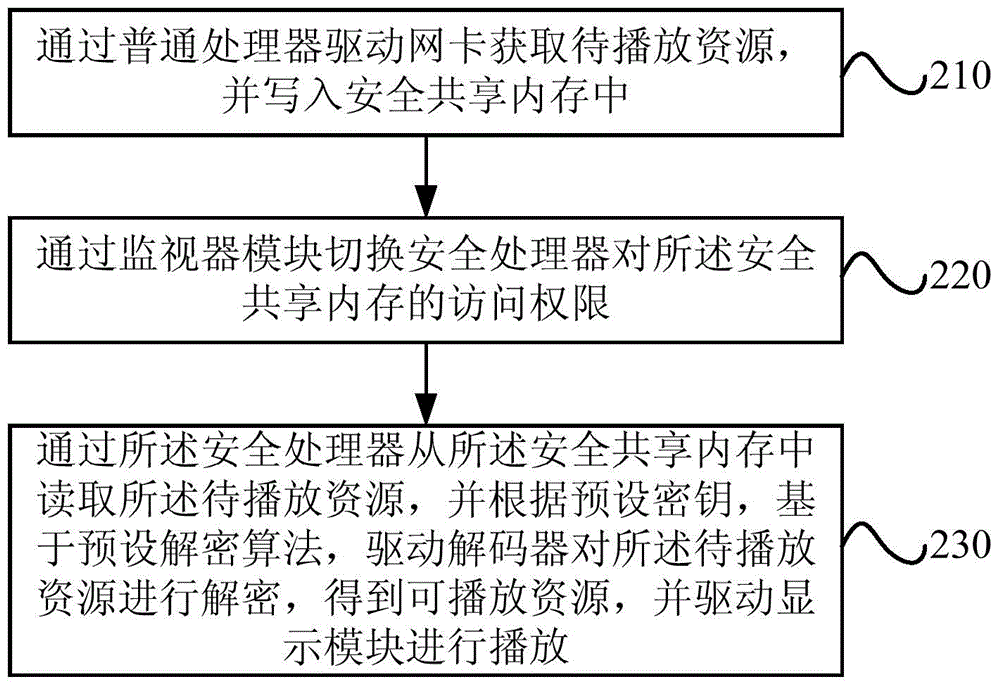
[0027] This embodiment provides a resource playing method for an intelligent terminal. The method of this embodiment may be executed by a resource playing system implemented by hardware and / or software for an intelligent terminal, and the implementation system is typically configured in an intelligent terminal capable of providing resource playing services.
[0028] For the sake of clarity, the smart terminal is first introduced.
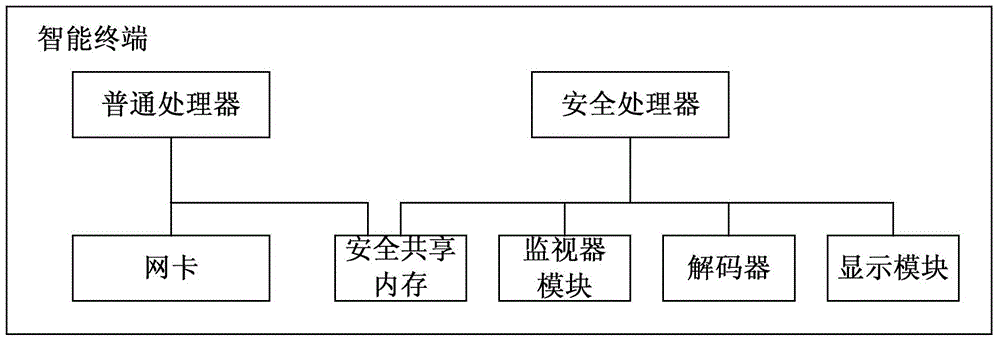
[0029] see Figure 2a , is a schematic structural diagram of a smart terminal provided in Embodiment 1 of the present invention. The intelligent terminal includes: a safe shared memory, a network card, a monitor module, a decoder, a display module, an ordinary processor and a safety processor.
[0030] Wherein, the network card is connected with the common processor, and the monitor module, the decoder and the display module are respectively connected with the safety processor through a safety bus, and the safety bus protocol based on the safety b...
Embodiment 2
[0055] This embodiment provides a resource playing system for a smart terminal, and the resource playing system is typically configured in the smart terminal provided in the above embodiment. The structural diagram of the resource playback system configured in the smart terminal is as follows Figure 3a shown.
[0056] The system includes: a common operating system module, a resource acquisition module, a safe operating system module, a decryption module and a playback module.
[0057] Among them, the resource acquisition module runs on the common operating system module and is used to pass through the network card (such as Figure 3a As shown, the network card belongs to the hardware layer) obtains the resources to be played, and writes them into the secure shared memory (such as Figure 3a As shown, the secure shared memory belongs to the hardware layer), and the resource to be played is an encrypted resource; as Figure 3a As shown, the common operating system module and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com