Encryption and decryption method of ciphertext
A technology of encryption, decryption and ciphertext, applied in the field of information communication security and security, it can solve the problems of limited thesaurus dictionary size, low embedding rate and security, and extremely strict requirements for differences in word meanings, and achieve high efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
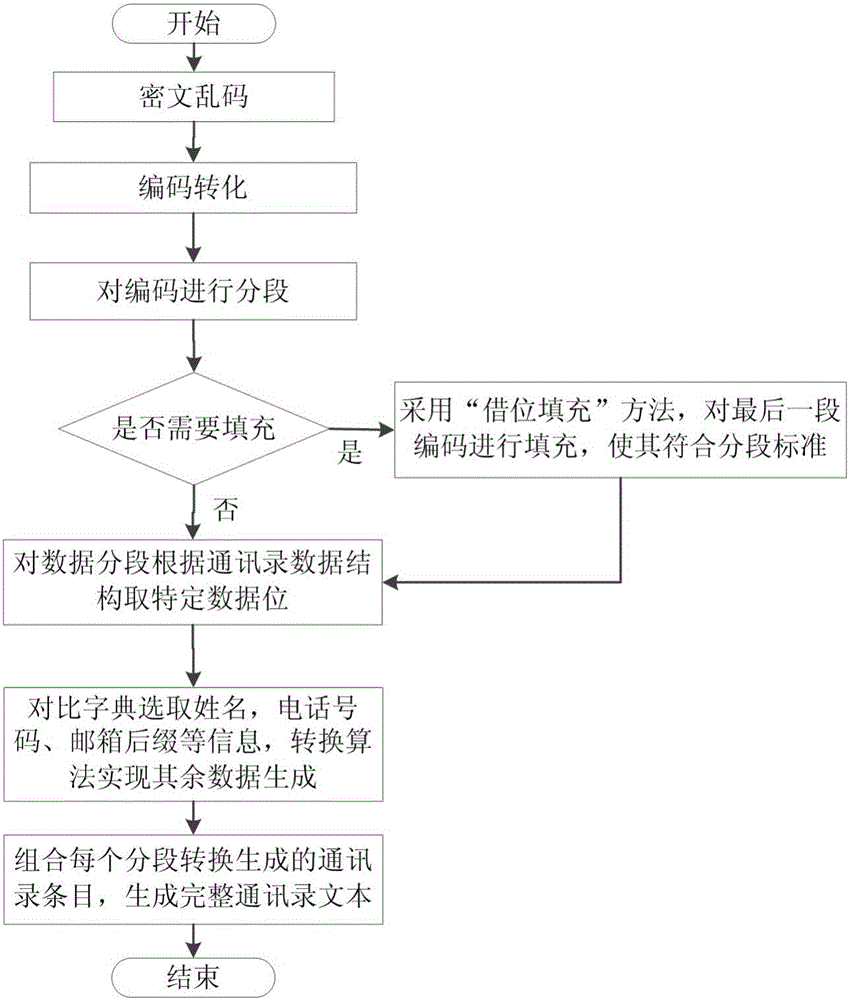
[0029] Embodiment 1: as Figure 1 ~ Figure 3 As shown, a method for encrypting and decrypting ciphertext, the method includes a dictionary generation module, an address book conversion module and a ciphertext conversion module, and the encryption steps are as follows:
[0030] (1) Dictionary generation module: collect the surnames and commonly used names of Chinese citizens, generate corresponding databases respectively, and remove the data with low randomness. The establishment of the dictionary satisfies the rationality of names, including the common use and pronunciation of Chinese population names ,significance;
[0031] (2) Obtain the plaintext that needs to be transmitted;
[0032] (3) encryption: adopt symmetric encryption algorithm and key generator to generate the key of encrypted plaintext to encrypt the plaintext in step (2) to generate ciphertext garbled characters;
[0033] (4) Address book conversion module: determine the maximum conversion rate according to th...
Embodiment 2
[0037] Embodiment 2: Example of address book format text:
[0038] 密钥生成:输入任一字符串的安全参数:164512121;输入初始密钥:50DAC7E4375BA89899FCC3D4BBFEFB9B;安全参数和初始密钥生成实际密钥:1937CBD97F321D7E2E2748B3BBED6A911589855E5B5491E28A43ACBD9E11284D,明文:FAB69830108696702FB6926DABE13C6FEA1FFFD4C5F8205E727B069ECD83E41E141BC93776E3898C1A30ACABBA45E56C592CFF2Fa8FCE907FA47F232402ABC7;采用对称加密算法获得密文乱码:50DAC7E4375BA89899FCC3D4BBFEFB9B; The generated meaningful address book text is shown in Table 1.
[0039] Table 1 Address Book Format
[0040] Name
[0041] Decryption process: Enter the actual key and address book, and use the symmetric encryption algorithm to obtain the plaintext.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More