Encryption system and method for resisting re-encryption key leakage and capable of cancelling attributes
An encryption system, re-encryption technology, applied in transmission systems, digital transmission systems, public keys for secure communications, etc. Solve the problem of proxy re-encryption server key leakage and other issues
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0090] The present invention will be further described below with reference to the accompanying drawings.
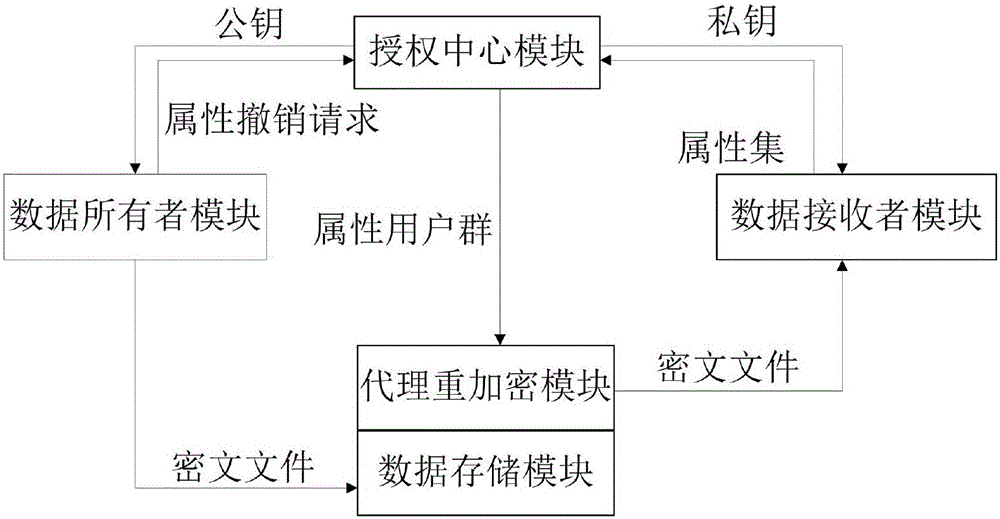
[0091] Refer to the attached figure 1 , to further describe the system of the present invention.
[0092] The system of the present invention includes an authorization center module, a data owner module, a data storage module, an agent re-encryption module, and a data receiver module. The data owner module is respectively connected with the authorization center module and the data storage module. The data receiver module is respectively connected with the authorization center module and the data storage module. The authorization center module is respectively connected with the data owner module, the data receiver module and the proxy re-encryption module. The proxy re-encryption module is respectively connected with the authorization center module and the data storage module. in:
[0093] The authorization center module is used to set the parameters of the encryptio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More