A Role-Based Resource Scope Control Method
A control method and resource technology, applied in the field of role-based resource scope control, can solve the problem that RBAC cannot control the resource scope, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
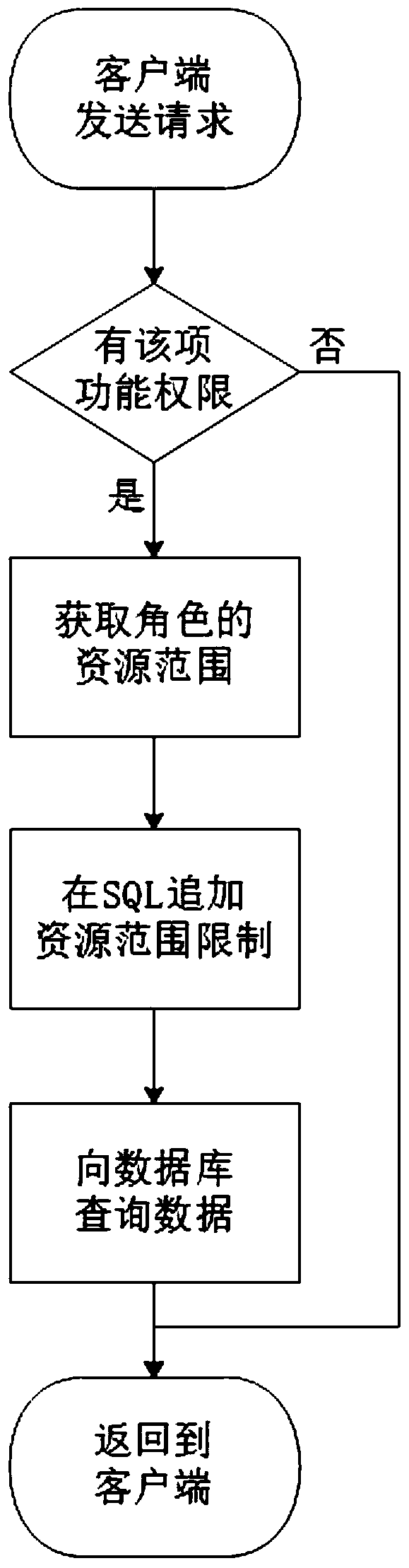
[0024] See attached Figure 1-3 Shown, method of the present invention implements according to following specific steps:
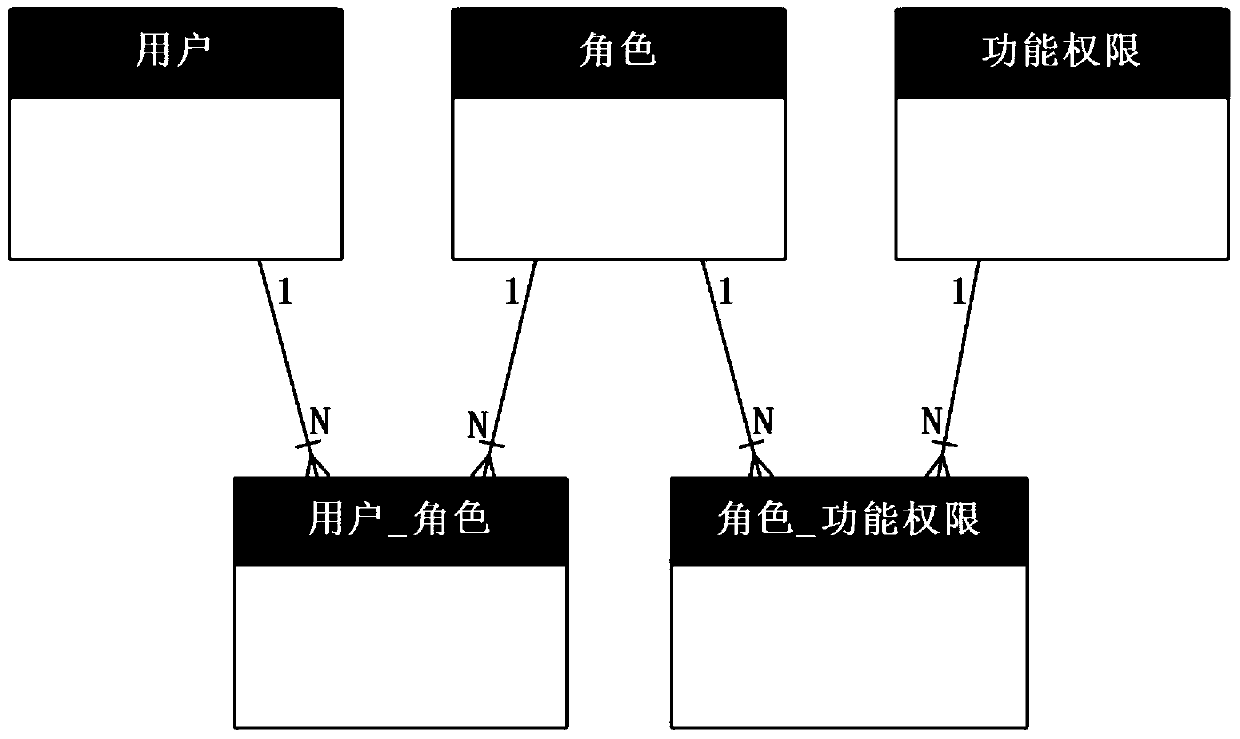
[0025] 1. Create a data table according to RBAC (role-based access control). Such as figure 1 shown.
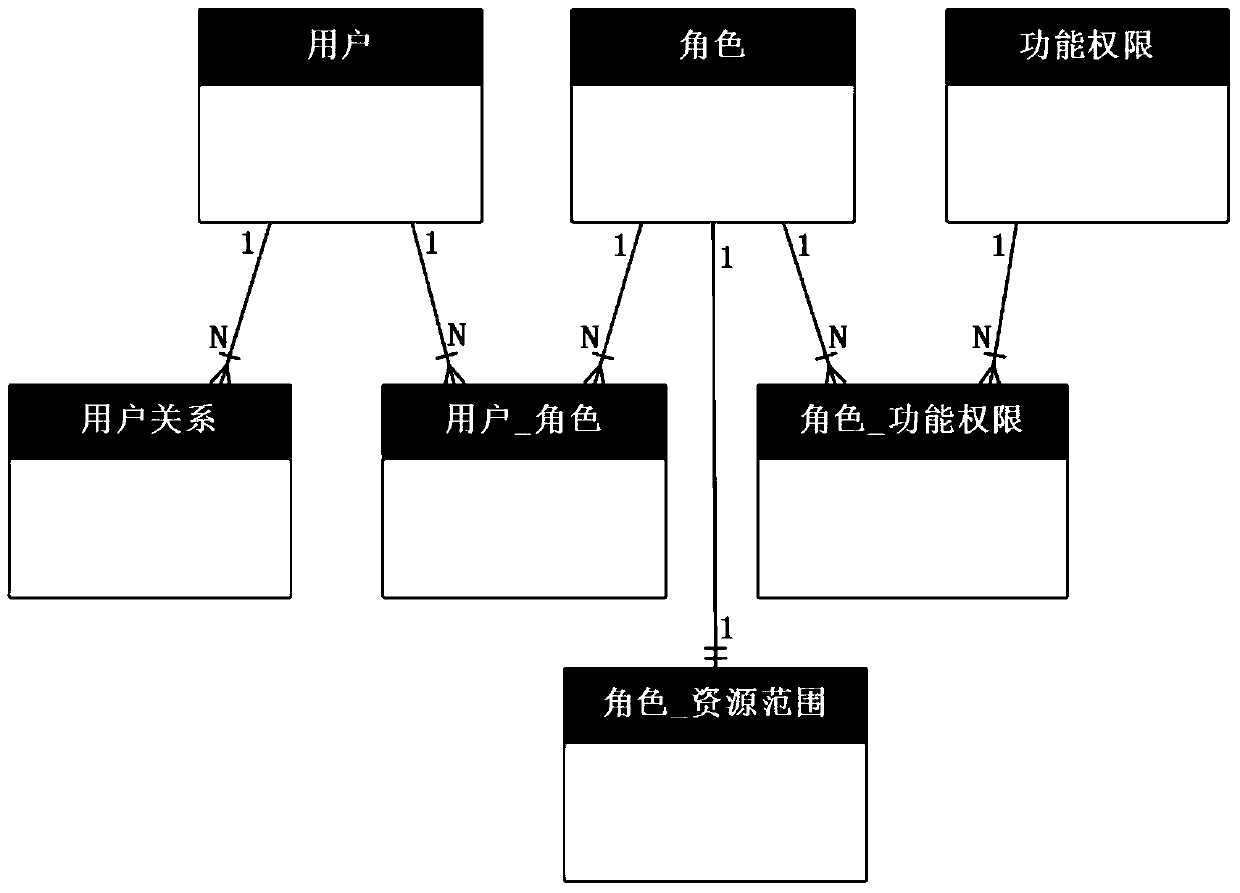
[0026] 2. Add the resource range table of the role to record the resource range owned by the role: self-built, some (optional), all; as needed, you can also add a user relationship table to record the user's superior, and control the resource range Sometimes, "some resources" need to be used. The entity-relationship diagram that constitutes RBRC, such as figure 2 shown.
[0027] 3. The SQL related to functional authority and resource scope is as follows (replace the question mark with the actual ID):
[0028]
[0029]
[0030]
[0031]
[0032] 4. When the client calls the server interface, it first judges whether it has the function authority, and if it does not have the function authority, it will report an error and return; if it has...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com