Multi-authority ciphertext-policy attribute-based encryption method
An attribute-based encryption and authorization mechanism technology, which is applied to the public key and key distribution of secure communication, can solve the problems of reducing the calculation cost in the decryption stage, increasing the calculation time, and affecting the battery life of mobile devices.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other. The present invention will be described in detail below with reference to the accompanying drawings and examples.
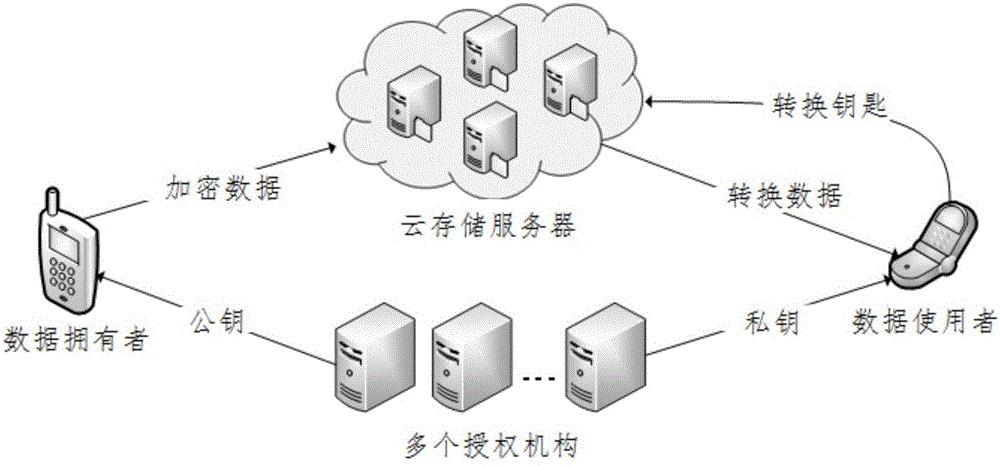
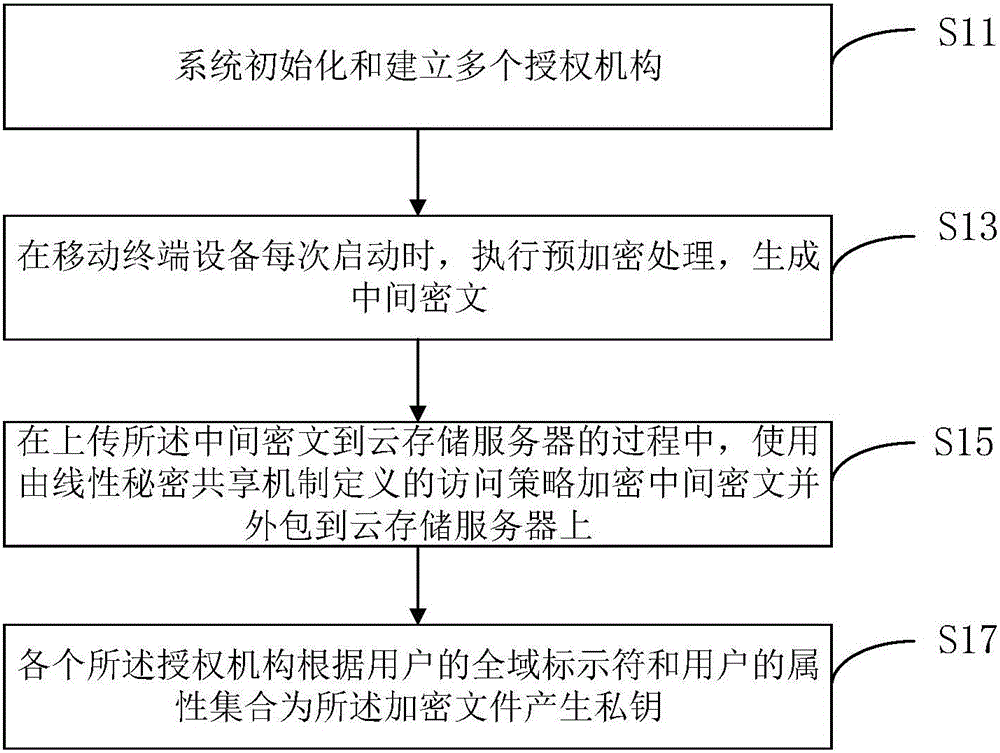
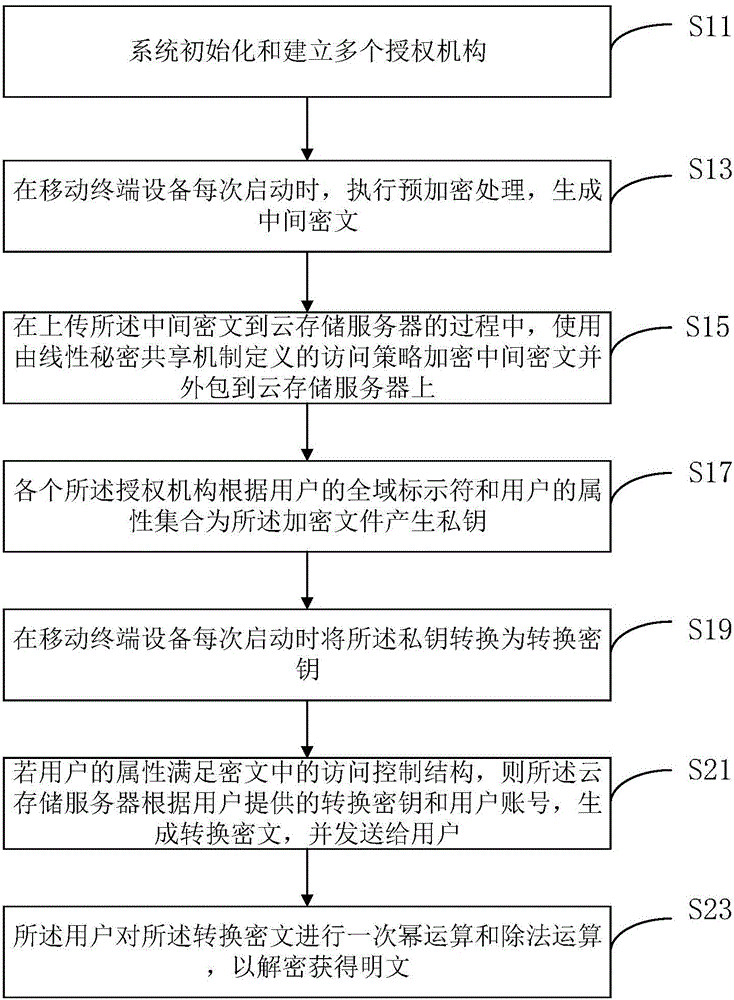
[0043] Figure 1 to Figure 3 Some embodiments according to the invention are shown.
[0044] Such as figure 1 and figure 2 As shown, the ciphertext policy attribute-based encryption method of multiple authorities includes the following steps:
[0045] Step S11, system initialization and establishment of multiple authorized institutions;
[0046] Step S13, when the mobile terminal device is started each time, perform pre-encryption processing to generate intermediate ciphertext;
[0047] Step S15. During the process of uploading the intermediate ciphertext to the cloud storage server, use the access policy defined by the linear secret sharing mechanism to encrypt the intermediate ciphertex...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com