Outsourcing attribute encryption method supporting attribute cancellation
An attribute encryption and attribute technology, which is applied to the public key and key distribution of secure communication, to achieve the effects of reducing computing overhead, efficient revocation, and good encryption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
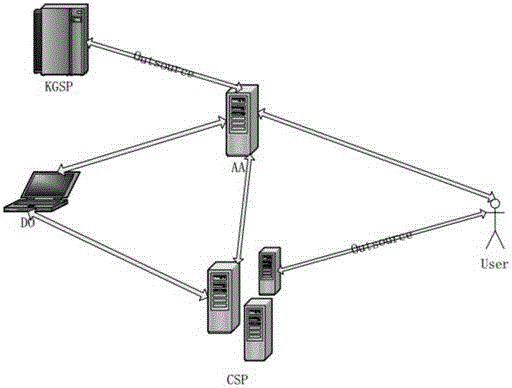
Method used
Image
Examples
Embodiment Construction
[0043] The present invention will be described in detail below in combination with specific embodiments.
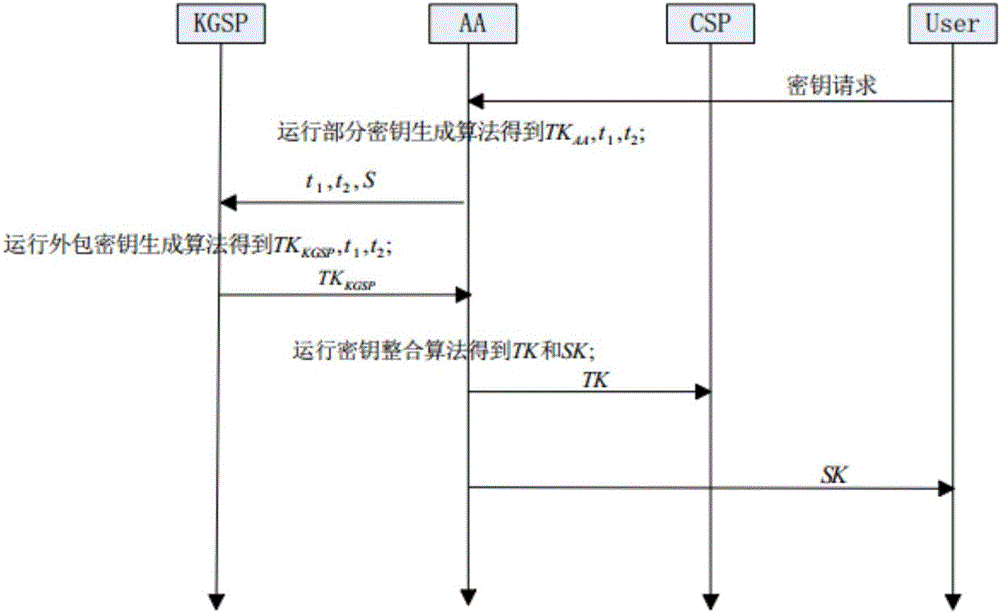
[0044]An outsourced attribute encryption method that supports attribute revocation in the present invention is specifically implemented according to the following steps:
[0045] Step 1, system initialization:
[0046] Specifically follow the steps below:
[0047] Input a security parameter λ and a description of the full set of attributes U={0,1} * , {0,1} * Represents a set {0,1,00,01,10,11,000,001,...} containing a combination of 0 and 1, and maps the full set of attributes to {0,1} * , and generate the corresponding parameter θ∈Z for the complete set of attributes p , where Z p ={0,1,....p-1}, the θ values of different attribute sets are different, choose a group G whose order is a prime number p, its generator is g and it satisfies the bilinear mapping e:G×G→ G T , choose a hash function F that maps an element in U to an element in G. Choose random numbers ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More