A differential computing method and system for network behavior characteristics
A network and behavior technology, applied in the field of differential computing systems with network behavior characteristics, can solve the problems of large impact on write performance, large data volume, poor flexibility, etc., to meet online real-time computing, reduce data volume, improve The effect of flexibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
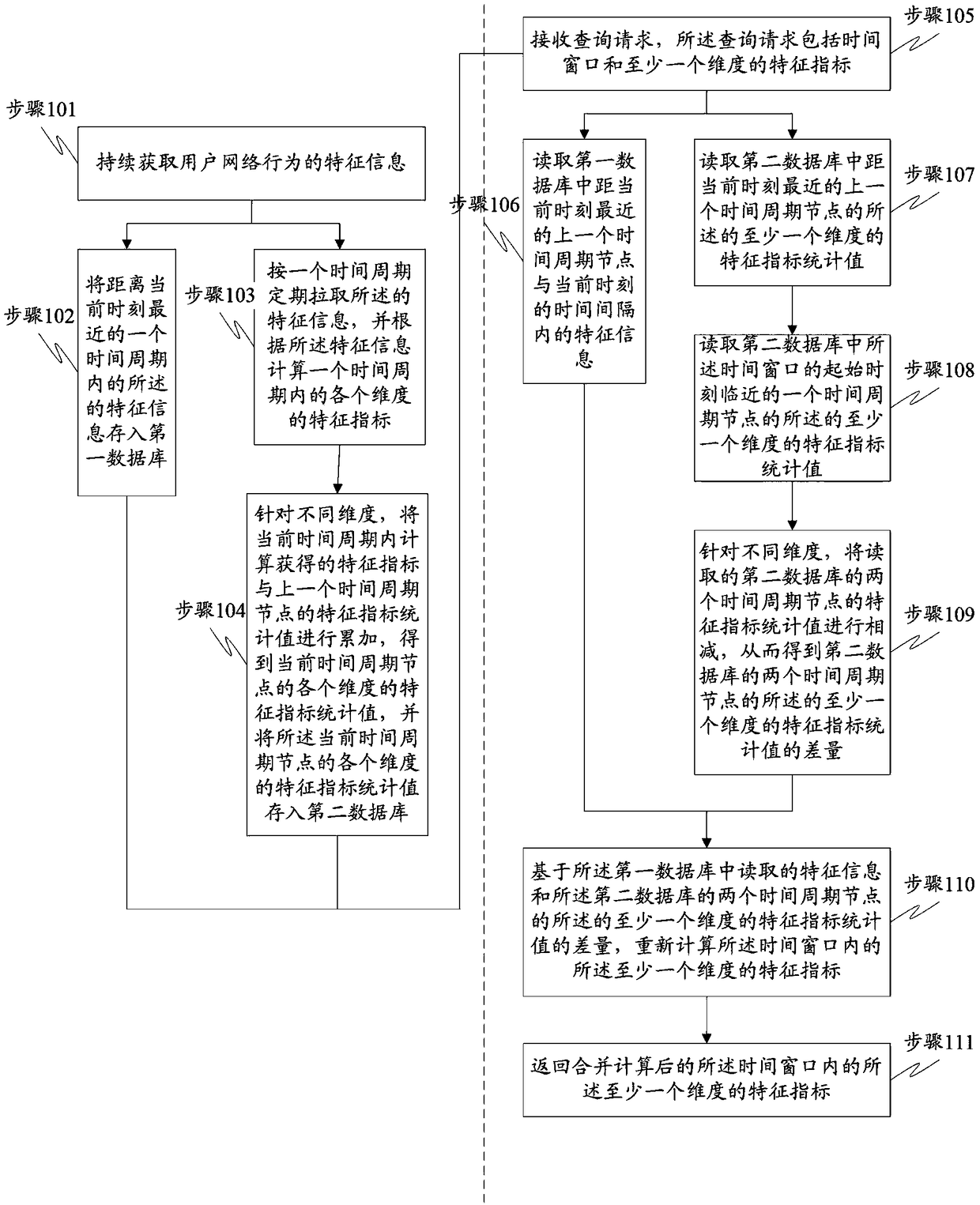
[0078] refer to figure 1 , which shows a flow chart of Embodiment 1 of the difference calculation method for network behavior characteristics according to the present invention, which may specifically include the following steps:
[0079] Step 101: Continuously acquire characteristic information of the user's network behavior.
[0080] Real-time monitoring of user network behavior, once there is a user operation, will collect the characteristic information of the above operation. The above operation can be for the user to register, log in, trade, etc. on the network. The above characteristic information means that when the operation is registration, the characteristic information will include user name, email address, mobile phone number, etc., and when the operation is login, the characteristic information will include Username, password, login IP, device ID, etc.
[0081] Step 102: Store the feature information within a time period closest to the current moment in the firs...
Embodiment 2
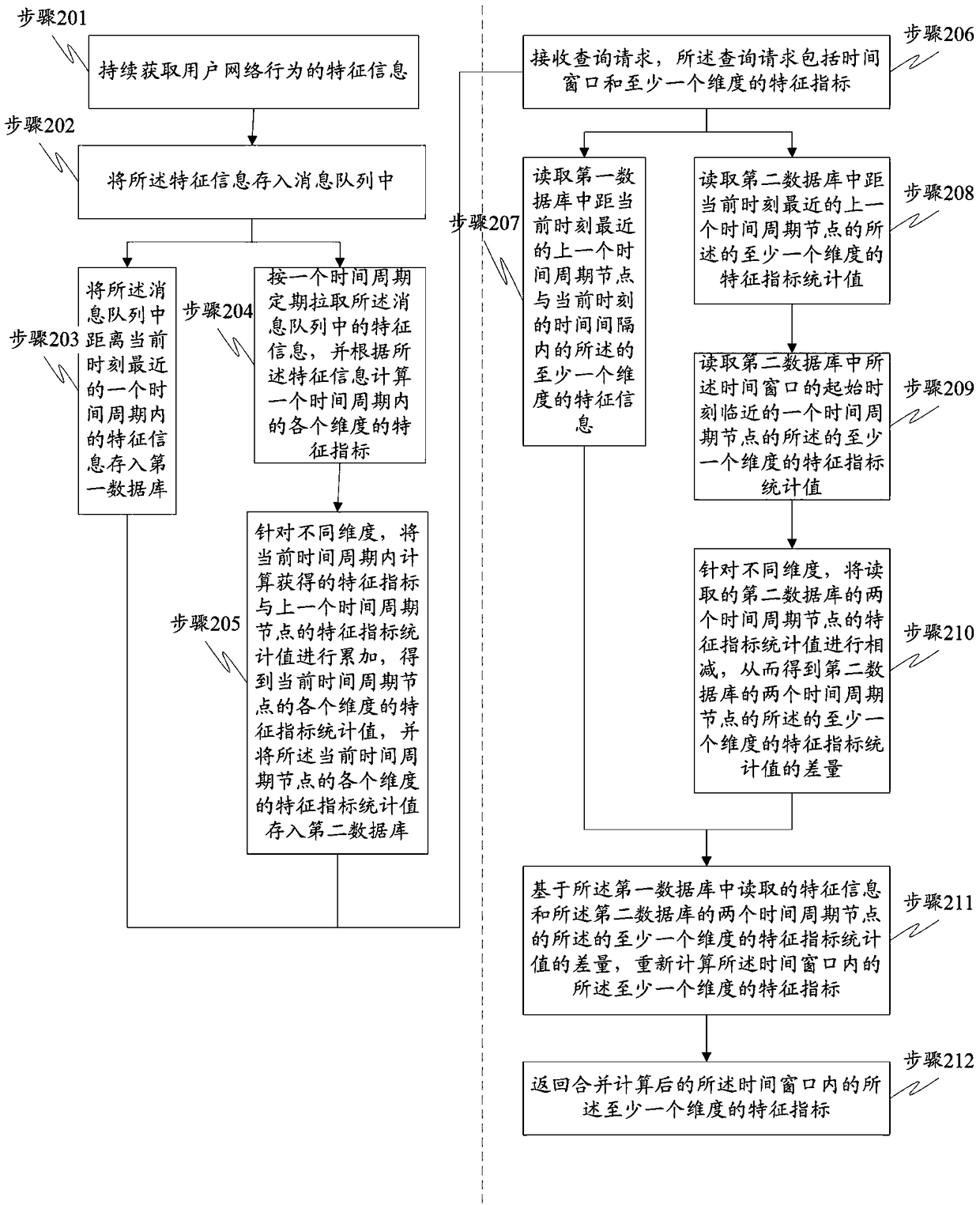
[0118] refer to figure 2 , which shows a flow chart of Embodiment 2 of the difference calculation method according to the network behavior characteristics of the present invention, which may specifically include the following steps:
[0119] Step 201: Continuously acquire characteristic information of the user's network behavior.
[0120] The embodiment of the present invention combines Figure 2A Describe the specific logic frame diagram.
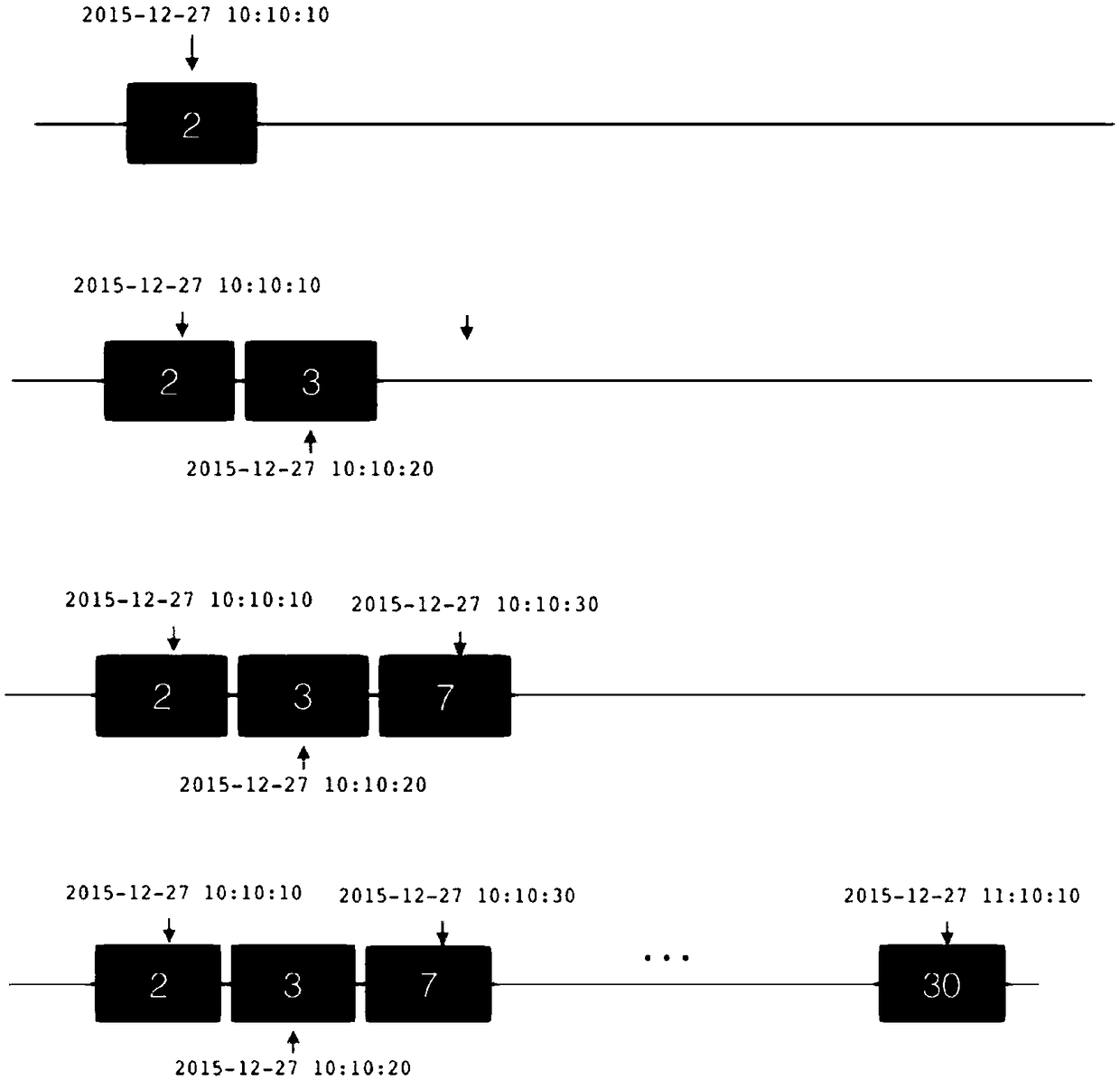
[0121] In this embodiment, the user's network behavior is collected in real time to obtain characteristic information of the user's network behavior. The characteristic information of the user's network behavior includes the user's registration, login, transaction and other operations on the network. The user's operation is called an event, and each event includes the attribute fields related to this operation. For example, the login event will include the user name, password, login IP, device ID, etc. combine Figure 2A , when the u...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More