Network trapping method based on honey pot
A network and honeypot technology, applied in the field of honeypot-based network trapping and network trapping, can solve problems such as false alarms, user troubles, failure to provide protection, etc., and achieve reasonable design effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
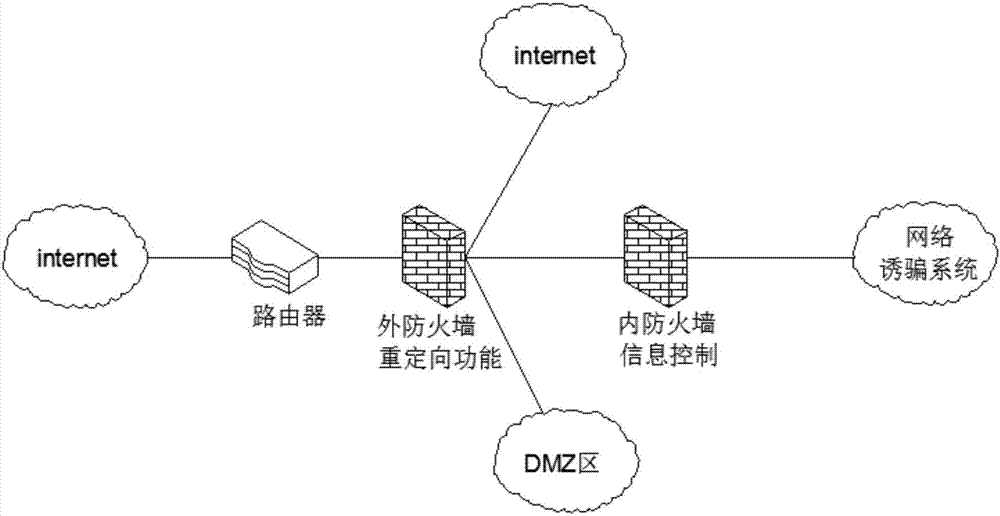
[0024] see figure 1 , a honeypot-based network trapping method, including
[0025] The external firewall, as the first line of defense of the network, protects the servers that provide web services;
[0026] Internal firewall, set the information control function of "wide entry and strict exit";
[0027] Network phishing system, containing various forged files and information, simulating real network resources to attract attackers to attack and invade honeyp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More